Breach and Attack Simulation
Validate your security controls with expert-led simulations that demonstrate effective defenses, exceeding automated tools.
What is Breach and Attack Simulation (BAS)?

Go beyond scans to demonstrate exactly how attackers could infiltrate your networks, escalate privileges, and impact your business
Breach and Attack Simulation is Part of Our Red Team Arsenal
Integrated into every Raxis Red Team engagement, BAS delivers continuous, realistic attack simulations across cloud, APIs, networks, physical, and social vectors.
From Headline Fear to Hands On Proof
Stop doom-scrolling breach news. As a cornerstone of Raxis Red Team, BAS lets you witness a controlled breach firsthand, transforming hypothetical risks into executive-ready storyboards with redacted evidence and remediation guidance.
Continuous Protection Through Red Team-Driven BAS
Managed via Raxis One, our Breach and Attack Simulation runs at regular intervals as part of Red Team exercises—preventing “test-prep syndrome” and maintaining urgency while ensuring compliance (PCI, SOC 2, HIPAA, and more).
Are Your Security Controls Actually Working?
Organizations spend heavily on firewalls, EDR, SIEM, and other security tools—but rarely know if they’ll stop a real attack.
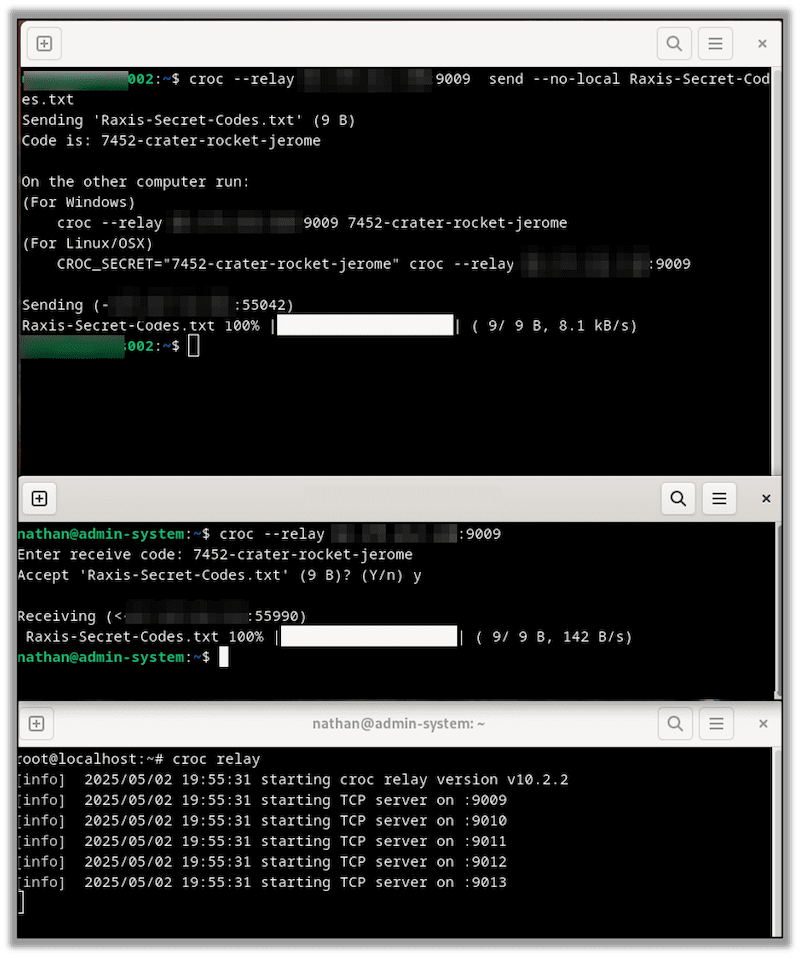
The Raxis Difference: Human-Led BAS
Our breach and attack simulation services are conducted by the same elite penetration testers who perform Red Team operations for Fortune 500 companies.
Adaptive Thinking
Our experts think like attackers, adapting techniques to your specific environment.
Creative Exploitation
Real hackers find unexpected paths—our team replicates that creativity.
Business Context
We understand what matters to your organization and prioritize accordingly.
Validation Over Volume
We focus on exploitable vulnerabilities, not generating alert noise.
Benefits of Raxis BAS
Measure Real Security Posture
Get quantifiable metrics on detection and prevention effectiveness.
Prioritize Remediation
Understand which vulnerabilities pose the greatest actual risk.
Validate Security Investments
Prove ROI on security tools and demonstrate value to leadership.
Meet Compliance Requirements
Our experts think like attackers, adapting techniques to your specific environment.
Improve Blue Team Effectiveness
Test your SOC’s detection and response capabilities safely.
Stay Ahead of Threats
Test against the latest attacker techniques as they emerge.
Safe, Controlled Environment
All simulations are conducted safely without disrupting operations.
AI-Augmented Human Expertise
We use AI to accelerate reconnaissance, pattern detection, and initial scans. Then, our human experts take over.
Intelligent Automation
Human Intelligence
What We What We Simulate & Validate
Full kill chain attack scenarios that follow a real intrusion end to end, from initial access through impact. Each one shows how an attacker would move through your environment and where your defenses need to hold.