The Exploit articles categorized as Penetration Testing
-
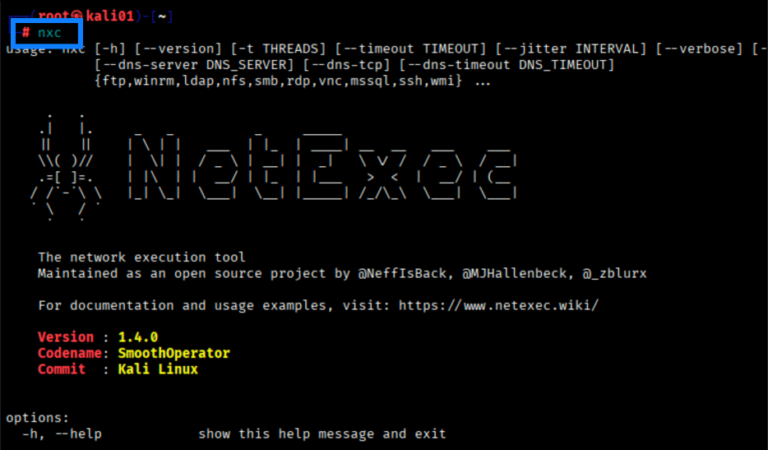
Cool Tools: NetExec (NXC) Fundamentals
By Scottie Cole Now that CrackMapExec is no more, how is a pentester to rapidly test credentials, enumerate assets, spray passwords, and more? Learn the basics of NetExec here. May 19, 2026 -

Bypassing ChatGPT’s Open-Source Model Security Restrictions for Agentic Hacking
By Ryan Chaplin Ryan Chaplin wondered what it would take to bypass ChatGPT’s open-source model security restrictions to allow AI to hack his website. See how he did it here. May 5, 2026 -
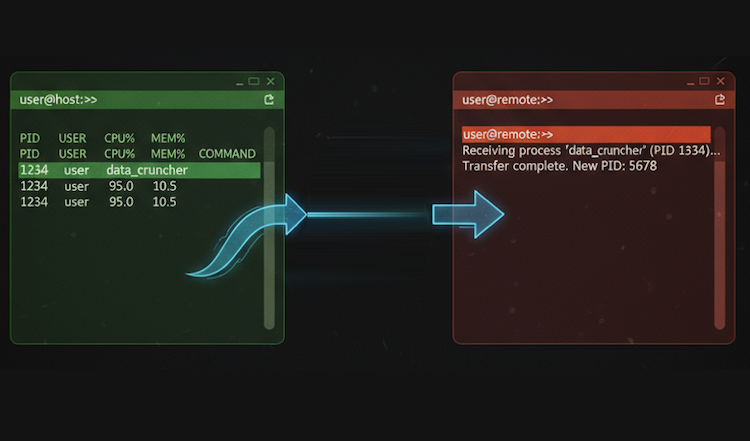
Cool Tools Series: Reptyr
By Jason Taylor Jason Taylor brings highlights reptyr in our Cool Tools series, showing how to take a long-running process, like an Nmap scan, and move it to a new screen. April 7, 2026 -

Five Things to Always Do After Getting Domain Admin
By Andrew Trexler So you got DA on your red team or internal network penetration test. Here are the five things that Principal Penetration Tester Andrew Trexler does next. March 24, 2026 -

The Hidden Risks in Your Password: What You Type Matters More Than You Think
By Brad Herring Raxis has discovered and cracked our fair share of password hashes. Some that we have discovered may surprise you… and their bosses. Learn what not to do. March 10, 2026 -
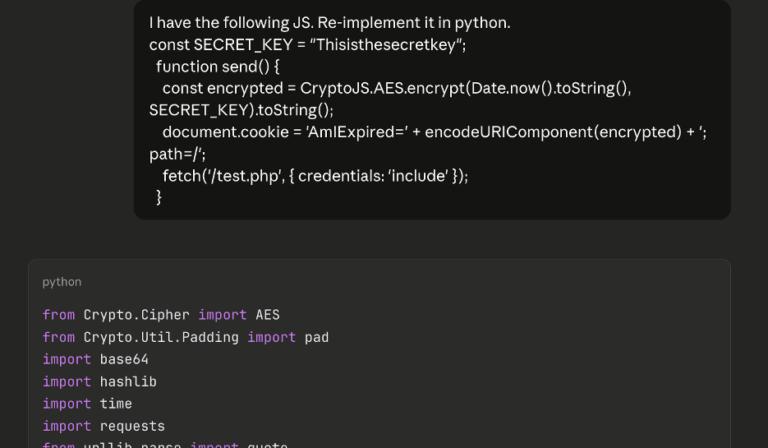
AI-Augmented Series: AI Scripting for Brute-Forcing on a Web App Pentest
By Andrew Trexler On a recent web app pentest, Andrew Trexler used AI to find client-side code that stopped his brute-force attack then used AI again to thwart that code. March 4, 2026