The Exploit articles categorized as Security Recommendations
-

CIS vs. NIST: Understanding Cybersecurity Standards and Frameworks
By Brian Tant Raxis’ CTO Brian Tant discusses two important gap analysis tools security professionals use to assess cyber defenses: CIS 18 and NIST 800-53. January 7, 2022 -
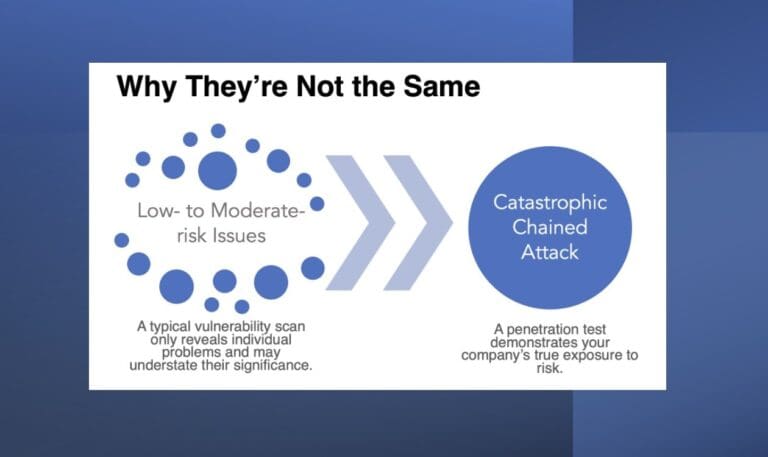
Chained Attacks and How a Scan Can Leave You Vulnerable
By Tim Semchenko Vulnerability scans are useful tools for protecting your network. Find out why you shouldn’t rely on them exclusively. December 10, 2021 -
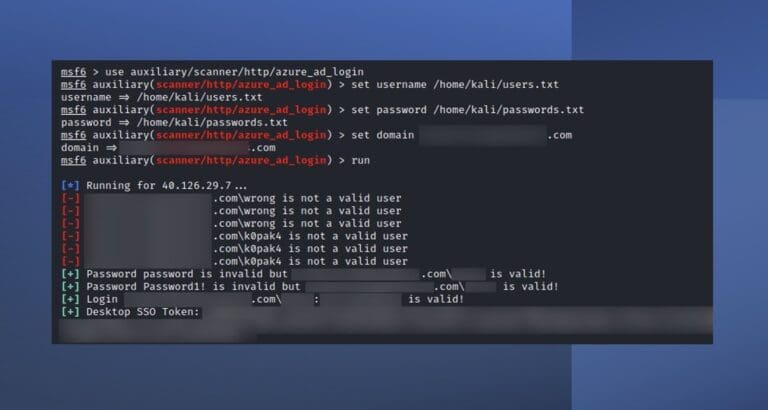
New Metasploit Module for Penetration Testing: Azure AD Login Scanner
By Raxis Research Team Raxis’ Matt Dunn has published another Metasploit module, this one describing a vulnerability in Azure’s Active Directory Seamless Single Sign-on. Learn more here. November 23, 2021 -

Introduction to Cross-Site Scripting
By Raxis Research Team This video covers the basics of cross-site scripting, including reflected, stored, and DOM-based XSS as well as remediation to protect against these attacks. October 29, 2021 -
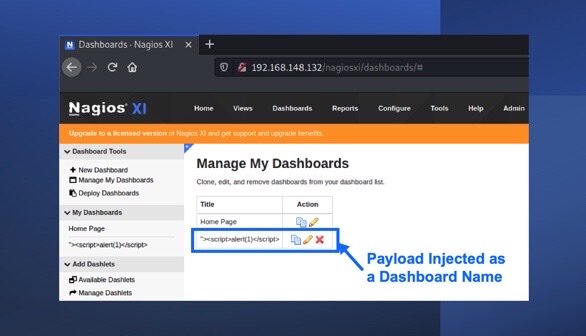
Nagios XI Stored Cross-Site Scripting (XSS): CVE-2021-38156
By Raxis Research Team Nagios is open-source network and system monitoring software. Raxis’ Matt Dunn has discovered a cross-site scripting vulnerability that could leave users open to attack. September 17, 2021 -
Keep Your Cookies in the Cookie Jar: HttpOnly and Secure Flags
By Raxis Research Team How can cookies be used against you? And how do you keep that from happening? Raxis’ Matt Dunn explains. September 3, 2021