Raxis Blog Posts by Category
-
 Choosing a Penetration Testing Company: Part 2Brad Herring continues our three-part “Choosing a Penetration Testing Company” series with a look at the factors to consider when choosing the best vendor.
Choosing a Penetration Testing Company: Part 2Brad Herring continues our three-part “Choosing a Penetration Testing Company” series with a look at the factors to consider when choosing the best vendor. -
 Cisco Releases Patch for CVE-2025-20188 – 10.0 CVSSCritical Alert – Patch Immediately. Cisco Releases Patch for CVE-2025-20188 – 10.0 CVSS. This vulnerability affects Cisco Catalyst 9800 wireless controllers.
Cisco Releases Patch for CVE-2025-20188 – 10.0 CVSSCritical Alert – Patch Immediately. Cisco Releases Patch for CVE-2025-20188 – 10.0 CVSS. This vulnerability affects Cisco Catalyst 9800 wireless controllers. -
 Choosing a Penetration Testing Company: Part 1Cole Stafford starts our three-part “Choosing a Penetration Testing Company” series by looking at what penetration testing is and the types of penetration tests.
Choosing a Penetration Testing Company: Part 1Cole Stafford starts our three-part “Choosing a Penetration Testing Company” series by looking at what penetration testing is and the types of penetration tests. -
 Understanding PTaaS: Penetration Testing as a ServiceWhat does Penetration Testing as a Service (PTaaS) really mean? In this blog we discuss the details and how do you find the best PTaaS for your organization.
Understanding PTaaS: Penetration Testing as a ServiceWhat does Penetration Testing as a Service (PTaaS) really mean? In this blog we discuss the details and how do you find the best PTaaS for your organization. -
 Cybersecurity: It’s how to say “Yes.”Contrary to common misconceptions, cybersecurity acts as a powerful enabler in the digital age, fostering innovation, driving business growth, and empowering organizations to harness technology’s full potential. By building trust, accelerating innovation, enabling emerging technologies, enhancing efficiency, ensuring compliance, supporting remote work, and protecting intellectual property, robust cybersecurity measures create a secure foundation for organizations to thrive and innovate in an increasingly interconnected world.
Cybersecurity: It’s how to say “Yes.”Contrary to common misconceptions, cybersecurity acts as a powerful enabler in the digital age, fostering innovation, driving business growth, and empowering organizations to harness technology’s full potential. By building trust, accelerating innovation, enabling emerging technologies, enhancing efficiency, ensuring compliance, supporting remote work, and protecting intellectual property, robust cybersecurity measures create a secure foundation for organizations to thrive and innovate in an increasingly interconnected world. -
 Accepting Penetration Test Risks & How Compensating Controls Can HelpTim Semchenko discusses documenting acceptance of risks and implementing compensating controls as options when pentest findings cannot be fixed immediately.
Accepting Penetration Test Risks & How Compensating Controls Can HelpTim Semchenko discusses documenting acceptance of risks and implementing compensating controls as options when pentest findings cannot be fixed immediately. -
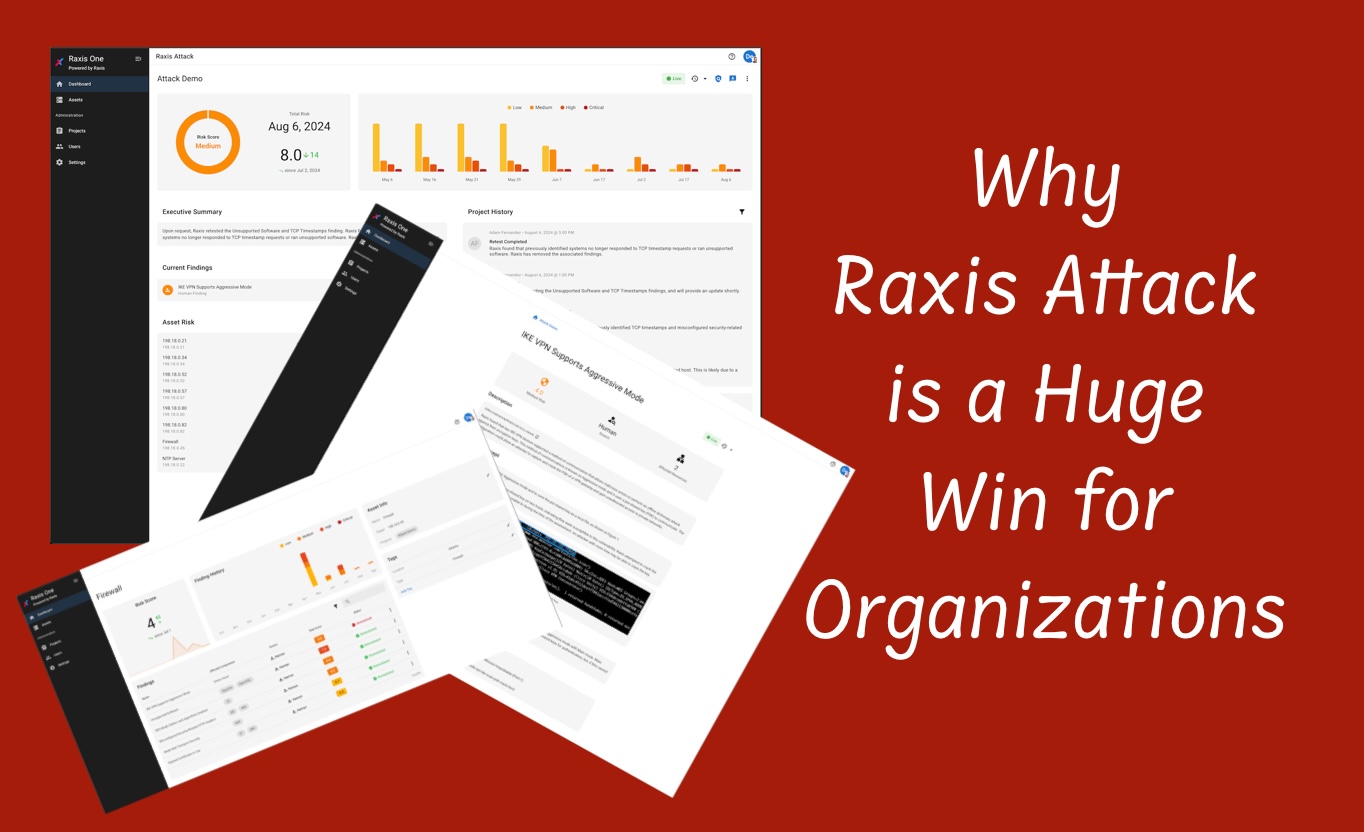 Why Raxis Attack PTaaS is a Huge Win for OrganizationsWith the recent launch of Raxis Attack, a powerful PTaaS service, Caroline Kelly is excited to share how it can help organizations of all sizes stay secure.
Why Raxis Attack PTaaS is a Huge Win for OrganizationsWith the recent launch of Raxis Attack, a powerful PTaaS service, Caroline Kelly is excited to share how it can help organizations of all sizes stay secure. -
 The CrowdStrike Outage: Lessons LearnedJust a few days ago the world felt the rippling effects of a third-party push to networks across the globe. What would have normally been a routine undertaking instead caused mass disruption of information systems and brought businesses of all sizes to a standstill. Almost everyone was impacted by this incident in one way or […]
The CrowdStrike Outage: Lessons LearnedJust a few days ago the world felt the rippling effects of a third-party push to networks across the globe. What would have normally been a routine undertaking instead caused mass disruption of information systems and brought businesses of all sizes to a standstill. Almost everyone was impacted by this incident in one way or […] -
 Ongoing Cyber Attack Disrupts Car DealershipsWednesday thousands of car dealerships across North America experienced a cyberattack resulting in widespread outages and significant operational degradation.
Ongoing Cyber Attack Disrupts Car DealershipsWednesday thousands of car dealerships across North America experienced a cyberattack resulting in widespread outages and significant operational degradation. -
 Password Length: More than Just a Question of CompliancePassword length requirements are a key part of password security, but, with PCI, NIST, OWASP, and CIS offering different recommendations, what length is best?
Password Length: More than Just a Question of CompliancePassword length requirements are a key part of password security, but, with PCI, NIST, OWASP, and CIS offering different recommendations, what length is best? -
 SOC 2 Compliance: Is it Right for Your Organization?SOC 2 is a compliance and privacy standard that outlines how to manage customer data & related systems to ensure confidentiality, integrity, and availability.
SOC 2 Compliance: Is it Right for Your Organization?SOC 2 is a compliance and privacy standard that outlines how to manage customer data & related systems to ensure confidentiality, integrity, and availability. -
 Raxis Achieves SOC 2 Type 2 ComplianceWe are thrilled to announce that Raxis has successfully achieved SOC 2 Type 2 compliance, providing assurance to our clients that their data is handled securely
Raxis Achieves SOC 2 Type 2 ComplianceWe are thrilled to announce that Raxis has successfully achieved SOC 2 Type 2 compliance, providing assurance to our clients that their data is handled securely
Categories
- Careers
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet The Team
- Mobile Apps
- Networks
- Password Cracking
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Unsupported Software Unpatched Systems
- Web Apps
- What People Are Saying
- Wireless
