The Exploit articles categorized as Security Recommendations
-
Keep Your Cookies in the Cookie Jar: HttpOnly and Secure Flags
By Raxis Research Team How can cookies be used against you? And how do you keep that from happening? Raxis’ Matt Dunn explains. September 3, 2021 -

Hurricane Ida: Limiting the Damage
By Scottie Cole Lead penetration tester Scottie Cole is a Gulf Coast resident and former first responder. Read his tips for avoiding hackers and scams that can be as costly as a natural disaster. September 1, 2021 -
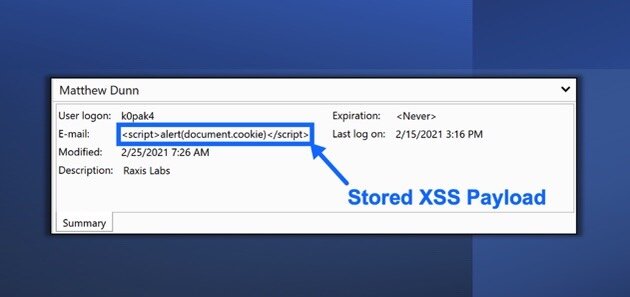
PRTG Network Monitor Stored Cross-Site Scripting Vulnerability (CVE-2021-29643)
By Raxis Research Team Raxis lead penetration tester Matt Dunn uncovers a new vulnerability in the PRTG Network Monitor (CVE-2021-29643). Read more here. August 20, 2021 -

Don’t Take the Smishbait
By Bonnie Smyre Unwanted text messages are annoying, but some also hide malicious links. Here are some ways to avoid being “smished.” July 30, 2021 -
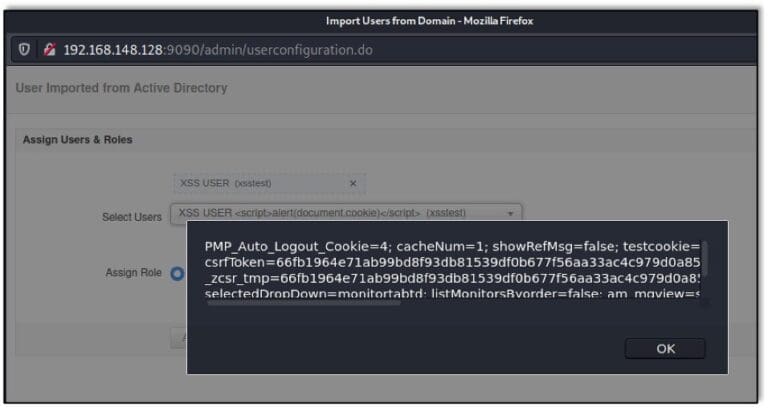
ManageEngine Applications Manager Stored Cross-Site Scripting Vulnerability (CVE-2021-31813)
By Raxis Research Team Raxis’ Matt Dunn has discovered another ManangeEngine cross-site scripting (XSS) vulnerability, this time in the Applications Manager product (CVE-2021-31813). June 25, 2021 -
Why Mutual Assured Destruction is an Incomplete Cyber Defense Strategy
By Bonnie Smyre Is the threat of full-scale retaliation enough to prevent large-scale cyberattacks? Raxis’ Bonnie Smyre explains why this Cold War strategy is not effective. May 14, 2021