Penetration Testing
Penetration tests that think like attackers. Not run the scans you already have.
Raxis Attacks.
Raxis Protects.
Automated scanners find known issues. Raxis validates what matters by thinking like an attacker: chaining weaknesses, testing business logic, bypassing defenses, and proving real impact before an adversary can.
Attack Paths, Not Isolated Findings
A low-severity issue rarely tells the whole story. Raxis engineers connect misconfigurations, exposed services, weak access controls, and application flaws to show how small gaps can become material business risk.
Custom Tooling and Tradecraft
Every environment is different, so every test should be too. Our team uses custom scripts, payloads, and attack chains to validate risk in your specific network, application, cloud, API, or mobile environment.
Human Judgment Where It Matters
AI-assisted reconnaissance and automation help expand coverage, but humans make the critical calls. Raxis engineers validate exploitability, test business logic, assess compensating controls, and separate real risk from scanner noise.
Clear Impact, Clear Fixes
The goal is not a longer findings list. It is a clear picture of what an attacker could do, which vulnerabilities matter most, and what your team should fix first.
Real Exploits Expose Real Risk
Exploiting software vulnerabilities is now the number one way attackers breach organizations, overtaking stolen credentials for the first time. Most of those attacks hit known weaknesses, the kind a real adversary surfaces but the scanners your team already runs walk right past.
Raxis validates risk the way attackers exploit it, then shows you exactly how to shut it down.
2026 PENETRATION TESTING THREAT DATA
SOURCE: VERIZON DBIR 2026
The throughline: the vulnerabilities getting exploited are already known and already scannable. They just weren’t validated or fixed. Closing that gap is what a Raxis pentest does.
Why Choose Raxis for Penetration Testing
Every Raxis penetration test is run by senior, US-based engineers, the same people from your scope call through your remediation retest. We test your environment by hand, report each finding with the steps to reproduce and remediate it, and retest once your team has made the fixes. Why companies choose us comes down to who does the work and how usable the results are.
What Is Penetration Testing?
Penetration testing services are authorized, simulated cyberattacks run by security engineers to find and exploit vulnerabilities before real attackers do. Companies often use them to meet compliance requirements.
Types of Penetration Testing
Expert-led assessments across every layer of your technology stack — available through both Raxis Strike and Raxis Attack PTaaS.
Penetration Test Quality Matters
A checkbox pentest satisfies your auditor.
A Raxis penetration test shows you where you’re actually exposed.
Breaches Exploit What Scanners Miss
IBM’s Cost of a Data Breach Report says a U.S. data breach now costs $10.22 million, and organizations take an average of 241 days to identify and contain one. Many exploit known vulnerabilities that a thorough penetration test can help validate, prioritize, and drive to remediation.Z
Validated Exploits, Not Scan Dumps
Every critical Raxis finding includes a proof-of-concept exploit and a step-by-step attack storyboard showing the full kill chain. From initial access to data exfiltration, you’ll see exactly what an attacker could do.
Remediation You Can Act On
Raxis penetration testing delivers prioritized, specific fix guidance, and definitely not a 200-page PDF of raw scanner output. Your engineering team gets clear steps to close the gaps, and subsequent retesting.
Raxis Offers PTaaS and Point-in-time Pentests
How Raxis Penetration Testing Works
Guided by the MITRE ATT&CK framework and grounded in NIST 800-115, our methodology reflects how real adversaries operate — not how textbooks say they should.
Penetration Testing for Compliance
Raxis penetration testing services help organizations validate security controls and produce evidence for major compliance frameworks.
PCI DSS 4.0
Raxis supports PCI DSS Requirement 11.4 with manual exploitation, segmentation validation where applicable, and the documented testing methodology QSAs expect under v4.0.
HIPAA Security Rule
Supports the Security Rule’s risk analysis and evaluation expectations, including §164.308(a)(1)(ii)(A) and §164.308(a)(8), with web application and network penetration testing that surfaces real ePHI exposure.
SOC 2
Produces auditor-ready evidence for the security Trust Services Criteria, showing your controls hold up to real exploitation rather than policy review alone.
GLBA Safeguards Rule
Delivers periodic penetration testing and vulnerability assessment evidence for FTC Safeguards Rule testing expectations under 16 CFR 314.4(d).
ISO/IEC 27001:2022
Delivers technical vulnerability testing evidence aligned with ISO/IEC 27001:2022 Annex A 8.8 for management of technical vulnerabilities.
CMMC 2.0
Supports DoD contractors protecting CUI with penetration testing evidence aligned to CMMC 2.0, NIST SP 800-171 objectives, and advanced Level 3 expectations where applicable.
NIST SP 800-115
Our methodology follows NIST SP 800-115, the federal technical guide to security testing and assessment.
GDPR Article 32
Supports Article 32(1)(d)’s requirement to regularly test and evaluate the effectiveness of your security measures, with risk-based testing scaled to your processing.
OWASP Testing Guide
Manual exploitation built on the OWASP Web Security Testing Guide, going beyond automated vulnerability scanning.
OWASP Top 10 for LLMs
AI application testing aligned to the OWASP Top 10 for LLM Applications and the MITRE ATLAS adversarial framework for AI-enabled systems.
FTC Section 5
Real-world exploit validation that helps demonstrate reasonable security practices under Section 5 of the FTC Act.
CIS Controls v8
Supports CIS Critical Security Control 18 with penetration testing that validates whether defenses work as intended.
NIST CSF 2.0
Provides real exploitation evidence that informs NIST CSF 2.0 risk management across Govern, Identify, Protect, Detect, Respond, and Recover outcomes.
FedRAMP
Supports FedRAMP penetration testing requirements for cloud service providers, following FedRAMP Penetration Test Guidance and required attack vectors.
Black Box, Grey Box, and White Box Penetration Testing
Our penetration tests follow industry standards to ensure comprehensive coverage.
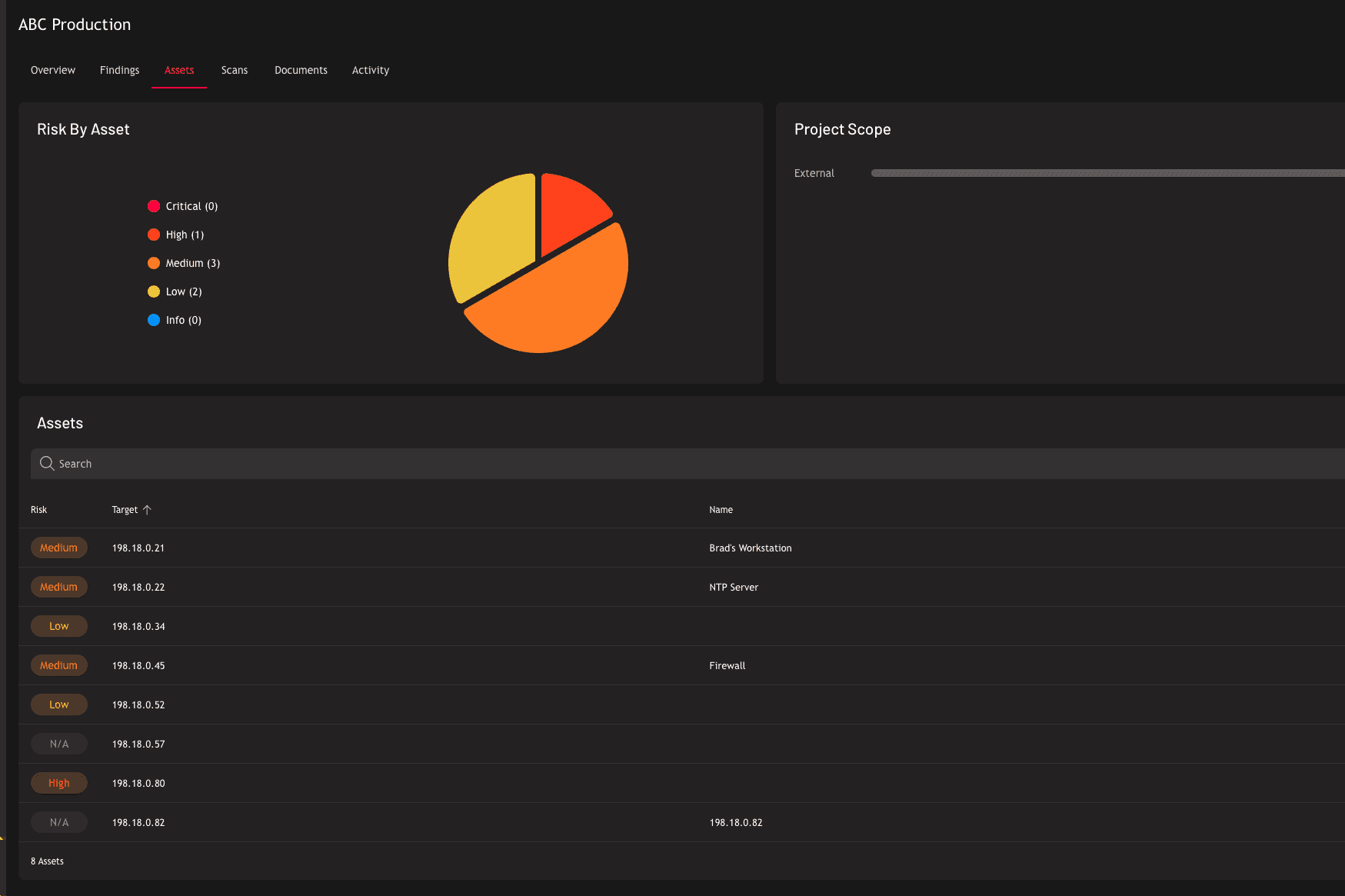
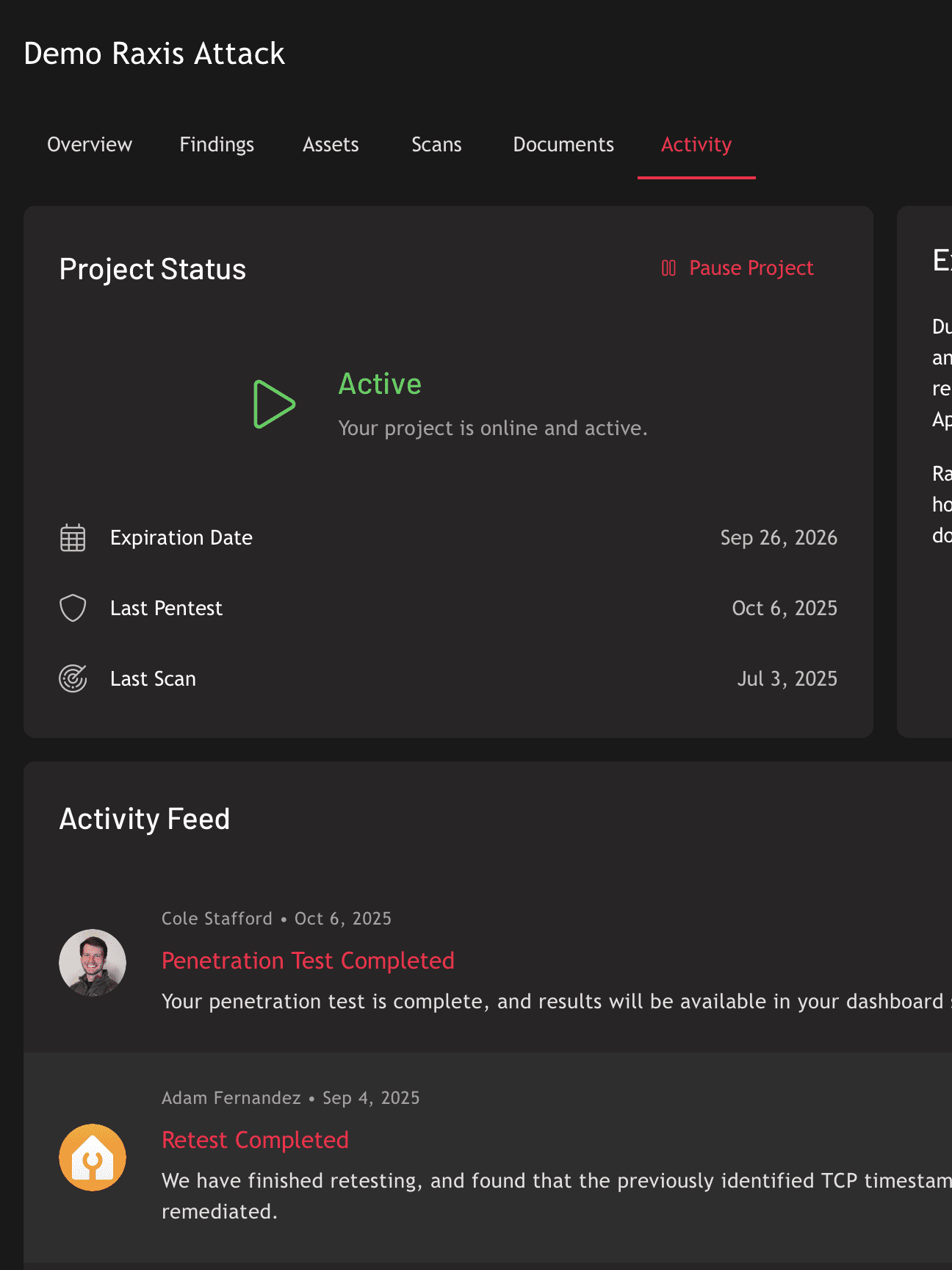
Real-Time Visibility Through Raxis One
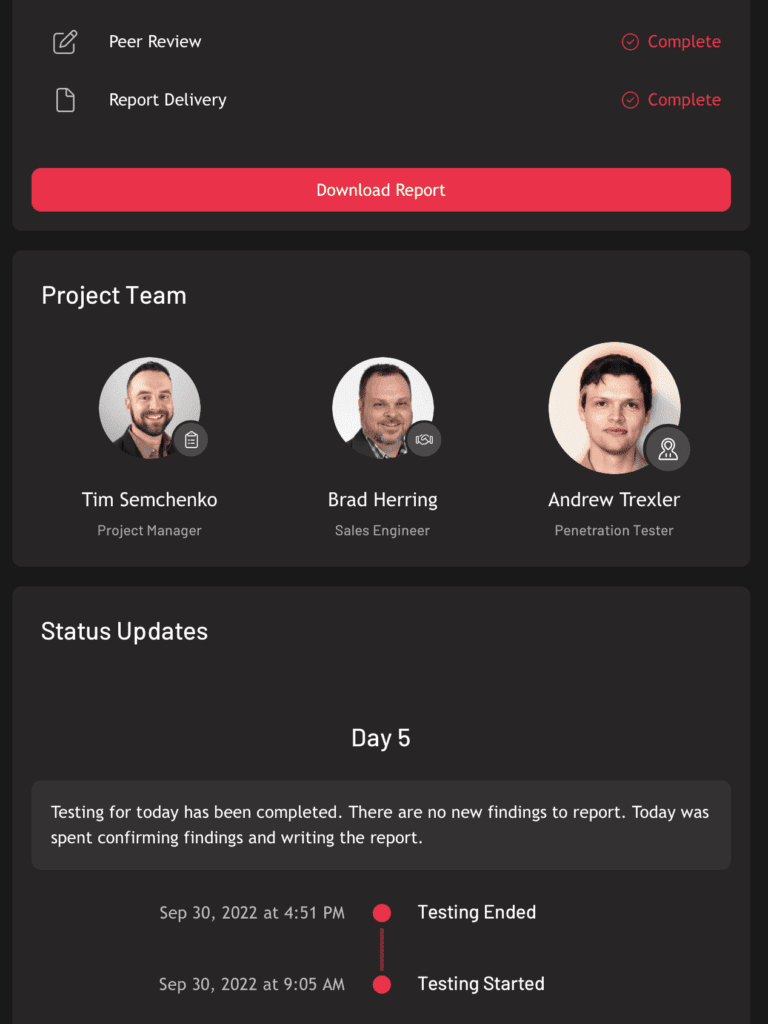
Every Raxis penetration test is managed through the Raxis One platform. This gives you live progress updates, interactive findings, attack storyboards, and remediation tracking in one place. No waiting weeks for a PDF.
Post Engagement Feedback
These real reviews come from security and engineering leaders we’ve worked with. Clutch verifies every review through a direct interview with the client, so each one is independently confirmed. Read the full set on our Clutch profile.
Feb 2, 2026 – Penetration Testing for Nonprofit Educational Institution
“Raxis’ expertise, top-notch customer service, and attention to detail were impressive.”
– CISO, The American College of Financial Services
July 11, 2025 – Application Penetration Testing for Logistics Company
“Raxis did an excellent job on fully testing this application.”
-Senior Security Analyst, Logistics Company
Oct 14, 2022 – Penetration Testing for Spam Filtering Company
“They had a high level of professionalism and knowledge about cybersecurity.”
– Manager Systems Engineering, Spam Filtering Company