Attack Surface Management
Raxis One allows you to Discover, Analyze, and Monitor assets across your platform.
This Is What Attack Surface management Was Meant to Be
Unrivaled Penetration Testing
The Raxis Pentest Team uses the same techniques that today’s malicious hackers use, including detection evasion, recent exploits, social engineering, and chained attacks. This is not a vulnerability scan, as our pentesters will breach your perimeter, pivot to other opportunities, exfiltrate critical data, obtain and crack password hashes, and demonstrate how a foothold would be maintained.
Advanced Social Engineering
Social engineering is a powerful attack vector that targets the greatest weakness in any organization: its people. Whether it’s through phishing, smishing, vishing, whaling, direct interaction, or other pretext, a well-executed social engineering test can manipulate your employees to reveal sensitive data in ways you never imagined.
Security Framework Analysis
A robust enterprise solution that gets down to brass tacks, we map your policies and procedures’ maturity across industry standard security controls. An extensive interview and documentation process leaves no stone unturned. Your greatest strengths, weaknesses, and all points between are spelled out in a detailed gap analysis and roadmap.
Red Team Assessment
In most of our Red Team assessments, physical security is deemed in scope to gain a full view of every potential avenue of attack. We test physical security to ensure that intruders can’t gain access to systems that may be protected by physical access controls. This often includes badge readers, wireless networks, electronic door locks, and network-connected cameras.
See Your Attack Surface Like Never Before
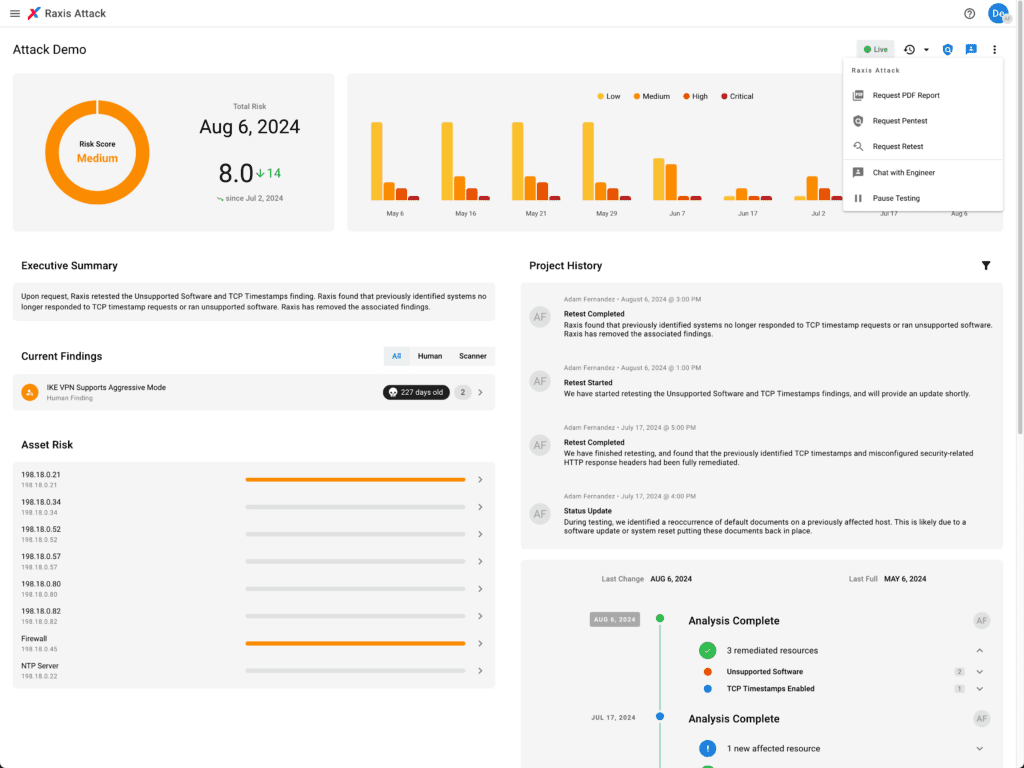
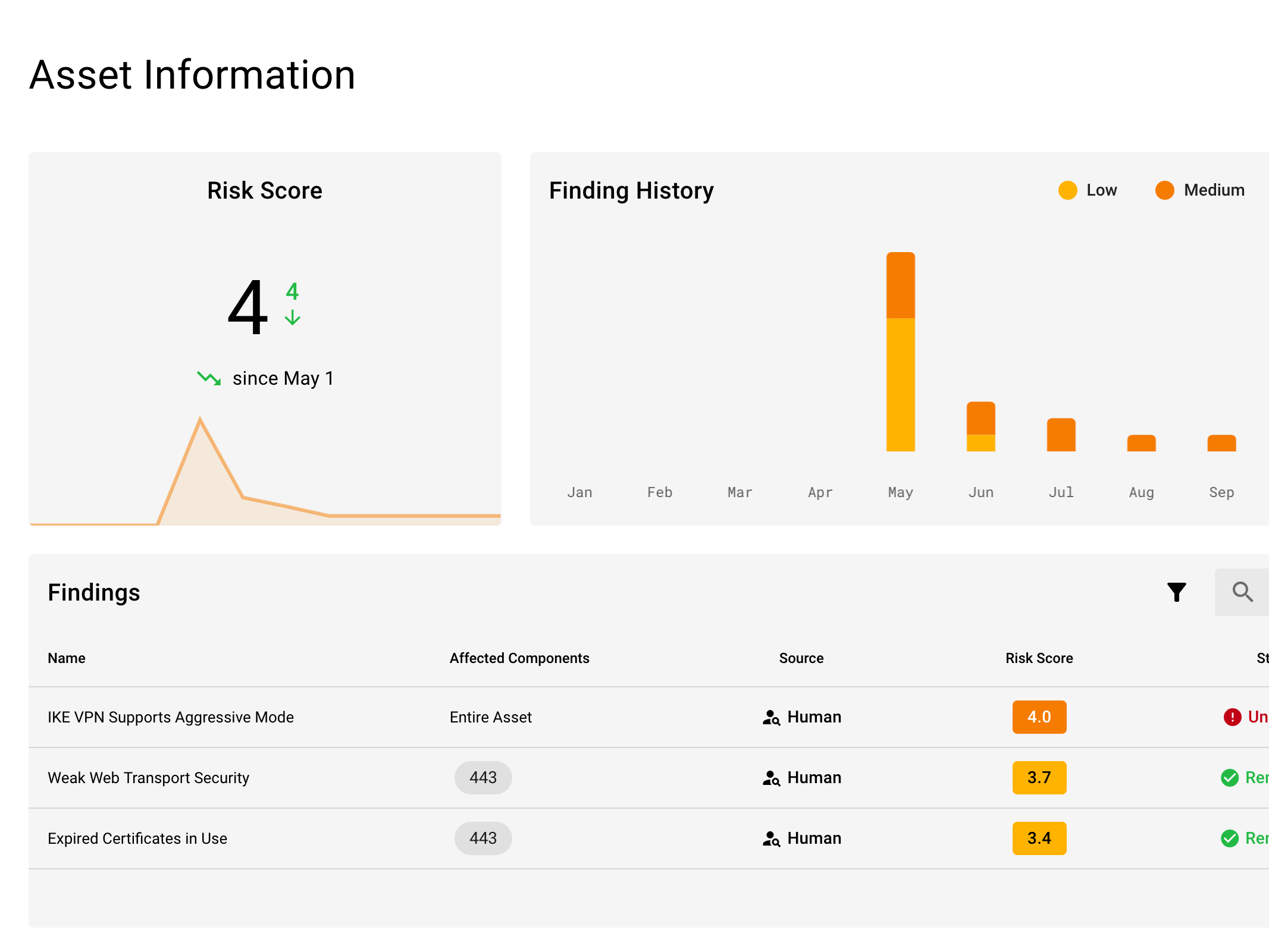
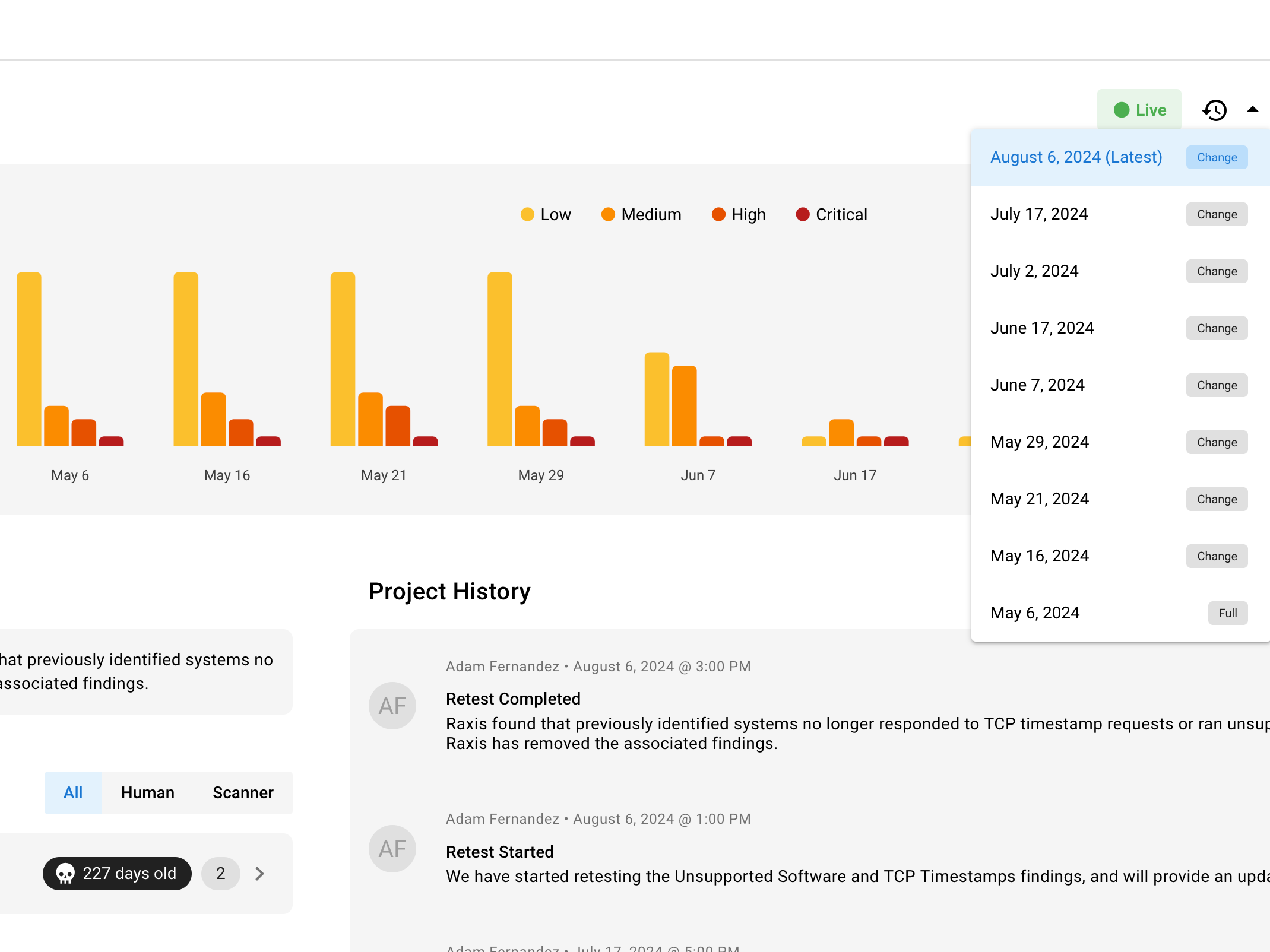
Use Raxis One, our innovative console for Attack Surface Management, to manage the latest details on your attack surface in real time, prioritize remediation, and easily retest your technology platforms.
Every Asset in View
Gain complete visibility into your digital landscape with Raxis’ advanced Attack Surface Management. Our cutting-edge tools and expert analysis uncover every asset—servers, cloud instances, applications, and more—ensuring no vulnerability goes unnoticed. By mapping your entire attack surface, we empower you to proactively address risks, prioritize remediation, and stay ahead of potential threats. With Raxis One, you’ll have the clarity and confidence to secure every corner of your infrastructure, keeping your organization protected in an ever-evolving threat landscape.
Scanning Isn’t Seeing
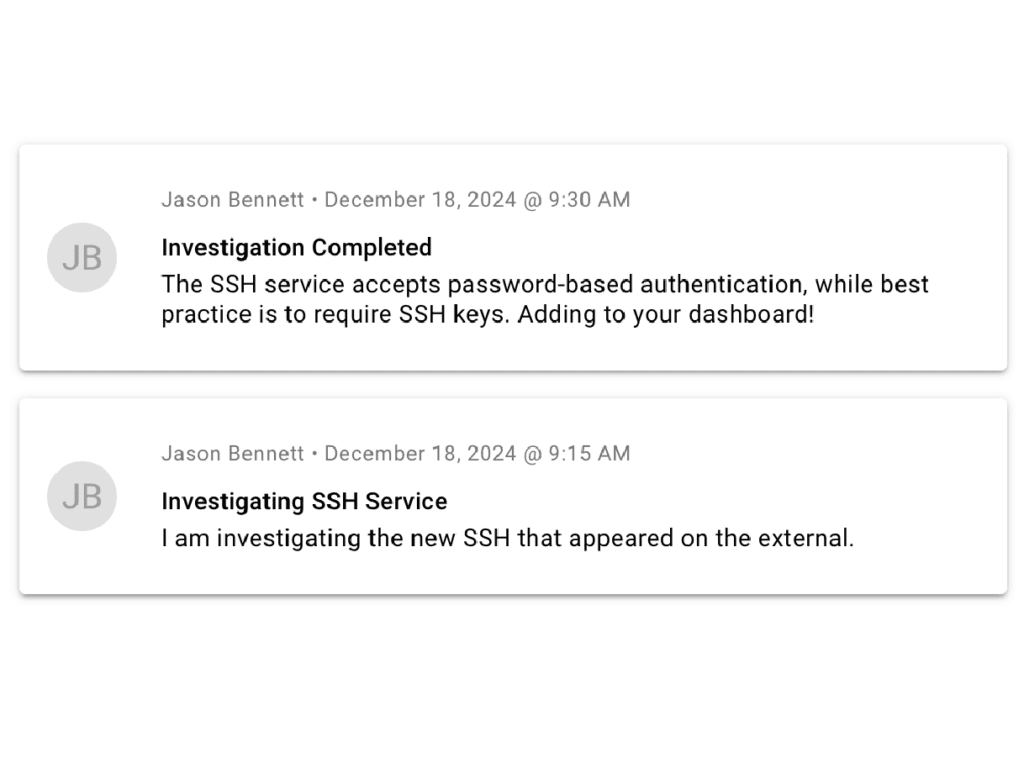
Much of the conversation around Attack Surface Management involves staying ahead in a technological arms race. Companies, including Raxis, are turning more to automation to stay ahead of the threats. But there is a tremendous difference between set-it-and-forget-it tech and integrated systems that extend the capabilities of human experts.
Human Powered Automation
Automation tools, while efficient and fast, lack the ingenuity, adaptability, and creativity of real hackers. They follow predefined rules and algorithms, which makes them excellent at identifying known vulnerabilities but incapable of uncovering complex, context-specific weaknesses or anticipating novel attack vectors. This is where Raxis steps in, leveraging the expertise of seasoned penetration testing engineers who think and act like real attackers. These professionals simulate sophisticated, real-world attack scenarios that automated tools simply cannot replicate, uncovering hidden vulnerabilities that could otherwise remain undetected.