Penetration Testing as a Service
(PTaaS)
Unlimited testing, real-time findings, and direct engineer access through Raxis Attack.
Continuous Pentesting, Human-Led
Kick off a penetration test in as little as 24 hours.
Get actionable results as we find them.
Built for Faster, Better Pentesting
Trusted pentesters, concise reporting, and a workflow built for busy teams.
Inside Raxis Attack PTaaS
Raxis Attack combines human expertise, workflow integration, and on-demand retesting in one platform.
Unlimited Testing & Retesting
Test as often as you need, after every sprint, release, or infrastructure change. We retest every fix as many times as needed and confirm it holds. No per-test fees and no retest fees, ever.
Direct Engineer Access
No ticket queues. No AI chatbots. Raxis Attack gives you a direct line to a US-based pentester working your engagement. Ask questions, discuss findings, and collaborate on fixes.
DevSecOps Integration
Connect Raxis One to GitHub, GitLab, Jira, Slack, and Teams. Findings flow into your existing workflows, so developers see vulnerabilities in the tools they already use every day.
AI-Augmented,
Human-Led Testing
AI-powered tools accelerate reconnaissance and expand coverage. Expert testers validate, chain exploits, and demonstrate real business impact.
Real-Time Findings
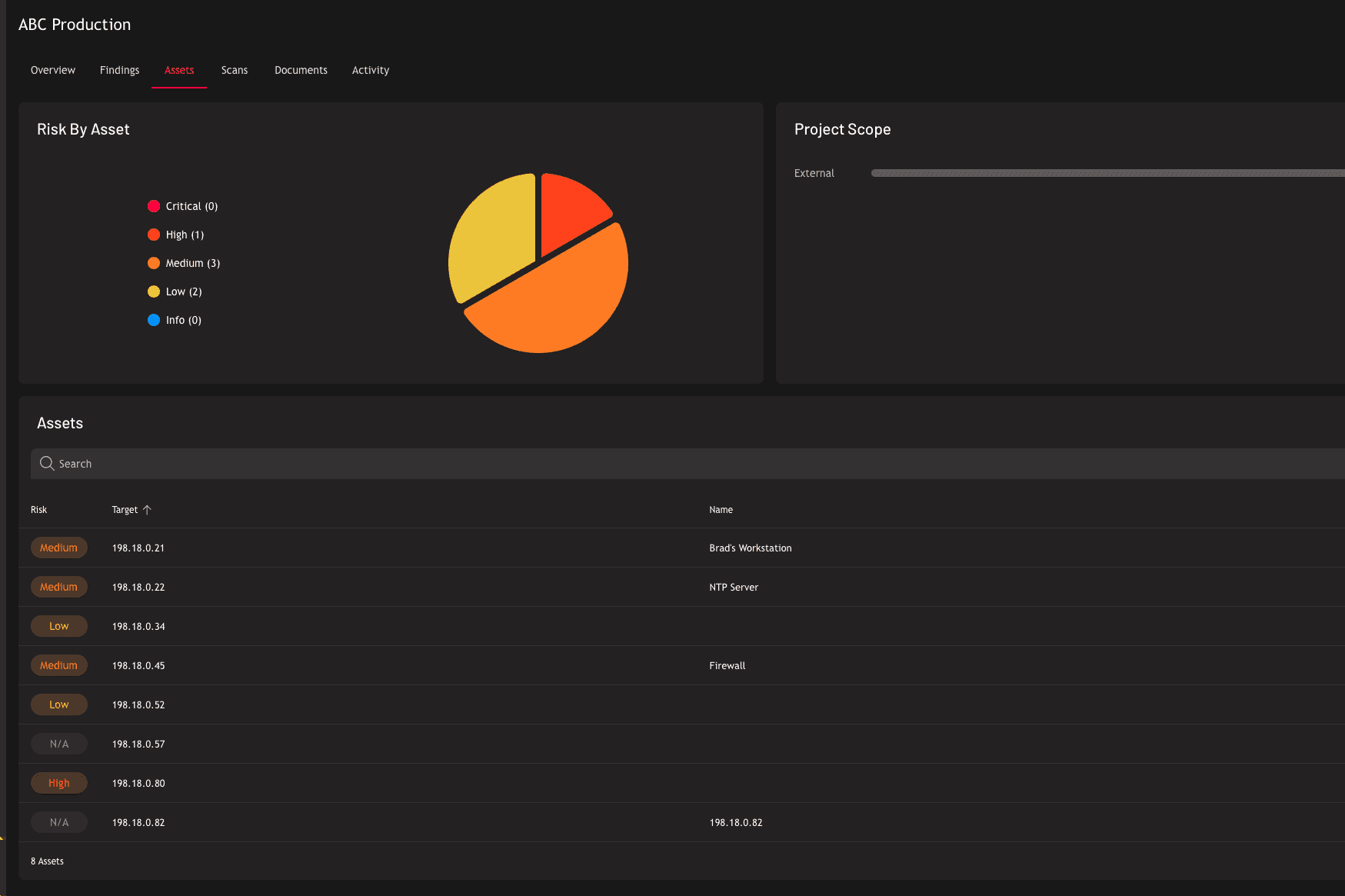
Every vulnerability appears in the Raxis One portal as it is discovered, with proof-of-concept screenshots, risk ratings, and remediation guidance. No waiting for a final report.
Continuous Compliance
Raxis Attack meets the recurring penetration testing requirements behind PCI DSS, HIPAA, SOC 2, ISO 27001, CMMC, and more. Generate audit-ready reports from Raxis One on demand. See how each framework maps to Raxis Attack PTaaS.
PTaaS vs. Point-in-Time Pentests
What Raxis Attack PTaaS Covers
Continuous, expert-led testing across every layer of your stack. Each focus area links to the dedicated methodology Raxis uses for in-depth, point-in-time engagements as well.
Predictable Pricing for Continuous Testing
Raxis Attack is a subscription-based PTaaS model built for ongoing validation, recurring retesting, and better long-term value than one-off pentests.
Subscription, Not One-Time
Pay for access to a service, not a single report. Predictable annual spend covers recurring testing throughout the term.
1–3 Year Commitments
Annual subscription is typical; multi-year commitments (1–3 years) improve planning, budgeting, and total value.
Recurring Testing & Retesting
Validate after code changes, releases, or infra updates without negotiating new projects. Retest fixes as often as needed.
Better Value Over Time
More validation cycles for the spend. Continuous coverage beats the cost of repeated standalone tests.
How Raxis Attack PTaaS Works
Guided by the MITRE ATT&CK framework and grounded in NIST SP 800-115.
Post-Engagement Feedback
“I was skeptical of PTaaS. Turns out the unlimited testing and direct connection to the pentester is incredibly valuable for development speed.”
Raxis Hack Stories
Our stories are based on real events encountered by Raxis engineers; however, some details have been altered or omitted to protect our customers’ identities.
The Always-On Defense
Our customer is a large enterprise with thousands of IP addresses and hundreds of services. With this large attack surface in place, they initially engaged Raxis for traditional internal and external network penetration tests. Pleased with the information they obtained there, they rolled up their sleeves and began knocking out critical and high risk remediations. But they didn’t stop there. These folks know that the cybersecurity threat landscape is always changing, so they made the leap to Raxis Attack.
Continuous, human-led PTaaS replaced the annual scramble, and the Raxis One dashboard became their daily command center. Now, the moment a Raxis tester confirms a finding, it materializes on their dashboard with a proof-of-concept screenshot, a risk-rating, an attack narrative, and prescriptive remediation steps. When something new appears, they wait. They use the chat with a pentester feature to work directly with the Raxis pentest team if they have questions, and they remediate the findings in real time. Broadcast poisoning, once a big vector in their environment, is a now a no-go for attackers. Their team is ready to squelch each new vulnerability as soon as it appears.
The result? A once-vulnerable environment is now one of the hardest targets we test. Critical and high risk findings are rare and are retired in days when they do appear. The gap that annual testing used to leave wide open has effectively vanished. This is what continuous penetration testing looks like in practice: real testers, real exploits, real-time findings, and a security team that stays one step ahead because they never stop hearing from the people trying to break in.