Manual Penetration Testing Services
Penetration testing services that think like attackers. Not run the scans you already have.
What Are Penetration Testing Services?
Penetration testing services are authorized, simulated cyberattacks performed by security engineers to find and exploit vulnerabilities before real attackers do. Unlike automated scans that flag known issues, Raxis penetration testing services use manual exploitation and attack chaining to prove what an adversary could actually accomplish across your networks, applications, cloud, wireless, IoT, OT, and AI systems.
Penetration Testing Threat Data
Attackers Are Exploiting Vulnerabilities Faster Than Ever
Exploited vulnerabilities are now the second most common way attackers breach organizations — and the gap is closing fast. Most target known weaknesses that a thorough penetration test would have caught. If your provider is running the same scanners your team already uses, you’re not finding what attackers will.
Why Other Penetration Test Companies Fall Short
Types of Penetration Testing Services
Expert-led assessments across every layer of your technology stack — available through both Raxis Strike and Raxis Attack PTaaS.
Why Penetration Test Quality Matters
A checkbox pentest satisfies your auditor. A Raxis penetration test shows you where you’re actually exposed.
Breaches Exploit What Scanners Miss
The average U.S. data breach now costs $10.22 million, and organizations take an average of 241 days to identify and contain one. Most exploit vulnerabilities a thorough penetration test would have caught.
Validated Exploits, Not Scan Dumps
Every critical Raxis finding includes a proof-of-concept exploit and a step-by-step attack storyboard showing the full kill chain. From initial access to data exfiltration, you’ll see exactly what an attacker could do.
Remediation You Can Act On
Raxis penetration testing delivers prioritized, specific fix guidance, and definitely not a 200-page PDF of raw scanner output. Your engineering team gets clear steps to close the gaps, and subsequent retesting.
The Raxis Difference: Manual Penetration Testing Services
Scanners find known vulnerabilities. Raxis engineers find the ones that matter — and prove they’re exploitable.
Raxis Strike and Raxis Attack: Two Ways to Test
Raxis offers continuous penetration testing and point-in-time assessments — both powered by the same elite team and AI-augmented methodology.
How Raxis Penetration Testing Works
Guided by the MITRE ATT&CK framework and grounded in NIST 800-115, our methodology reflects how real adversaries operate — not how textbooks say they should.
Penetration Testing for Compliance
Raxis penetration testing services satisfy requirements across every major security and compliance framework.
ISO/IEC 27001:2022
Comprehensive assessments aligned with Annex A.12.6.1 requirements.
CMMC 2.0
Supports DoD contractors with specialized CUI penetration testing (SI.3.218).
NIST SP 800-115
Testing methodology aligned with federal technical assessment guidelines.
GDPR Article 32
Risk-based testing that supports Data Protection Impact Assessments.
OWASP Testing Guide
Enhanced with manual exploitation that goes well beyond automated OWASP scanning.
OWASP Top 10 for LLMs
AI application testing aligned to the OWASP Top 10 for LLM Applications and MITRE ATLAS framework.
FTC Section 5
Demonstrates “reasonable security” with real-world exploit validation.
Black Box, Grey Box, and White Box Penetration Testing
Our penetration testing service scoping options follow industry standards to ensure comprehensive coverage.
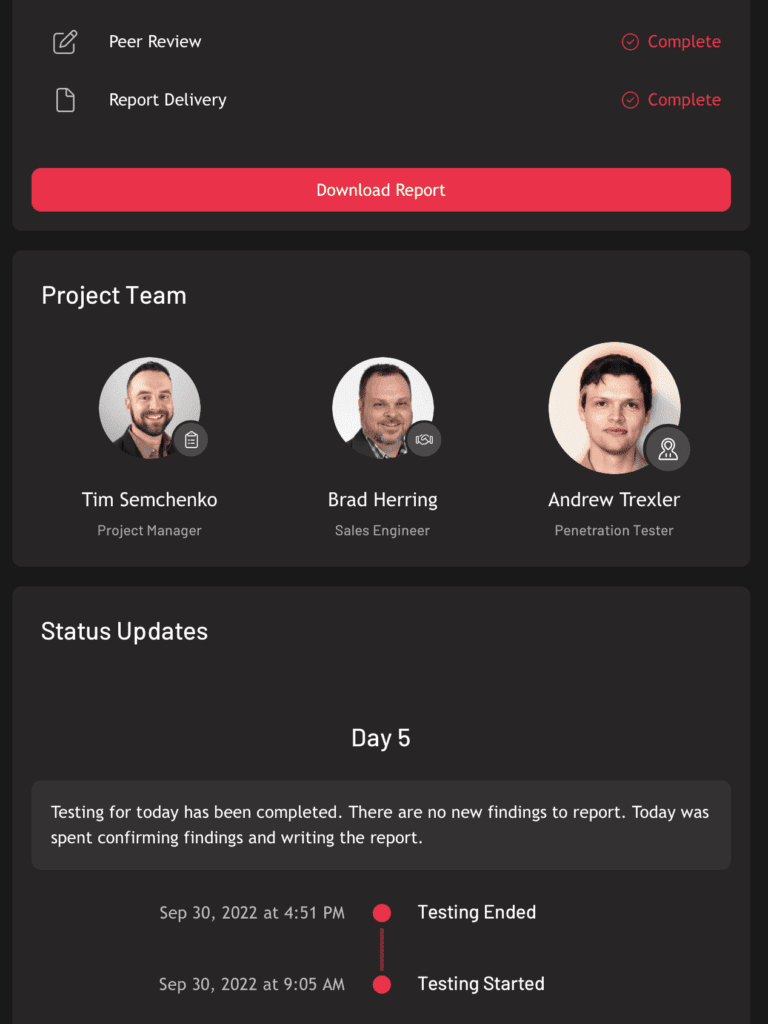
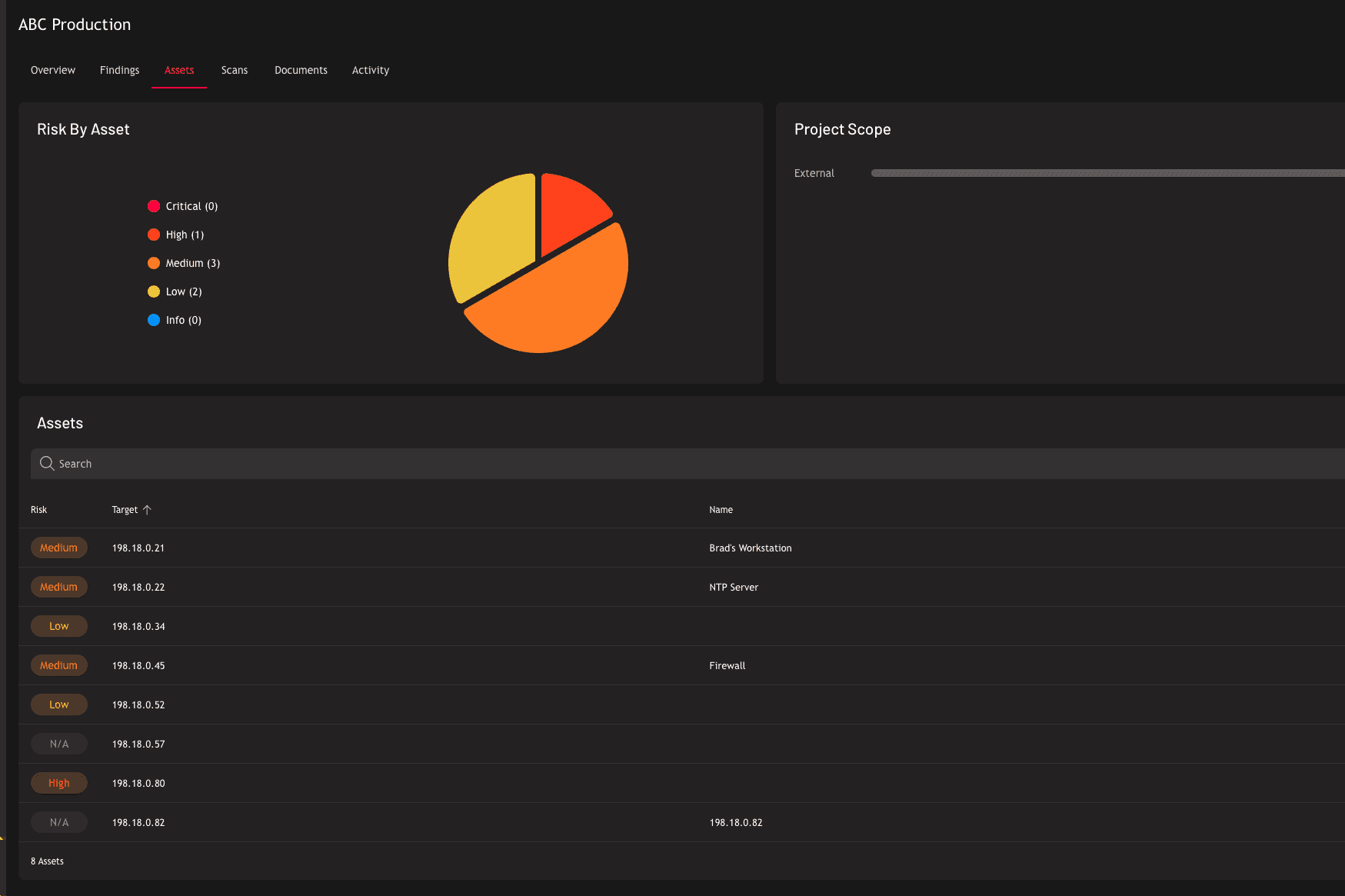
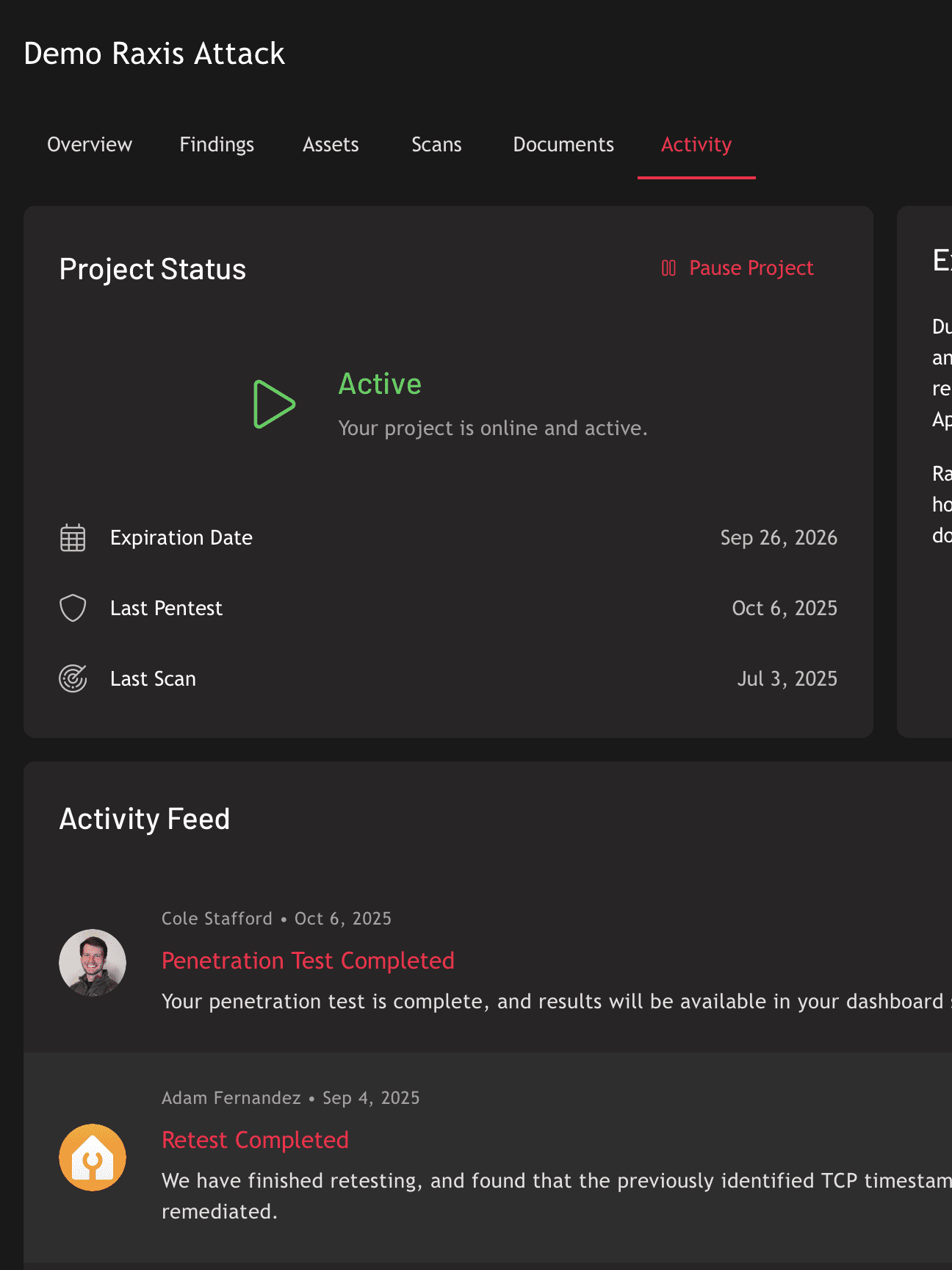
Real-Time Visibility Through Raxis One
Every Raxis penetration test is managed through the Raxis One platform — giving you live progress updates, interactive findings, attack storyboards, and remediation tracking in one place. No waiting weeks for a PDF.