Wireless Network Penetration Testing
Ensure that your wireless networks are properly safeguarded against potential threats from outside attackers and intruders.
How Does Penetration Testing Work Against Wireless Networks?
Raxis uses several techniques to leverage your wireless network with the goal of reaching the internal network and other critical systems.
Guest Wireless Traversal
Guest networks are designed to keep guests separated from corporate networks; however, configuration errors sometimes can be leveraged to escape the isolation.
Authentication weaknesses
Older encryption methods may be inadvertently configured, allowing for an attacker to exploit weaknesses to obtain access.
Device Misconfiguration
Some devices, such as IoT or regular workstations, may be connected to two or more networks and insecurely configured.
Brute Force
Strategically planned attacks will be made against your wireless passwords in an attempt to gain unauthorized access.
Man-In-The-Middle
Man-in-the-middle attacks leverage a specially crafted access point to capture and exploit legitimate wireless traffic.
Rouge Access Points
Unapproved access points connected to the network, either by attackers or unknowing employees, may offer weaker security configurations and even unauthorized access.
Hackers Work on a Least-Risk, Most-Reward Basis


Convenience and Security with Remote Wireless Penetration Testing
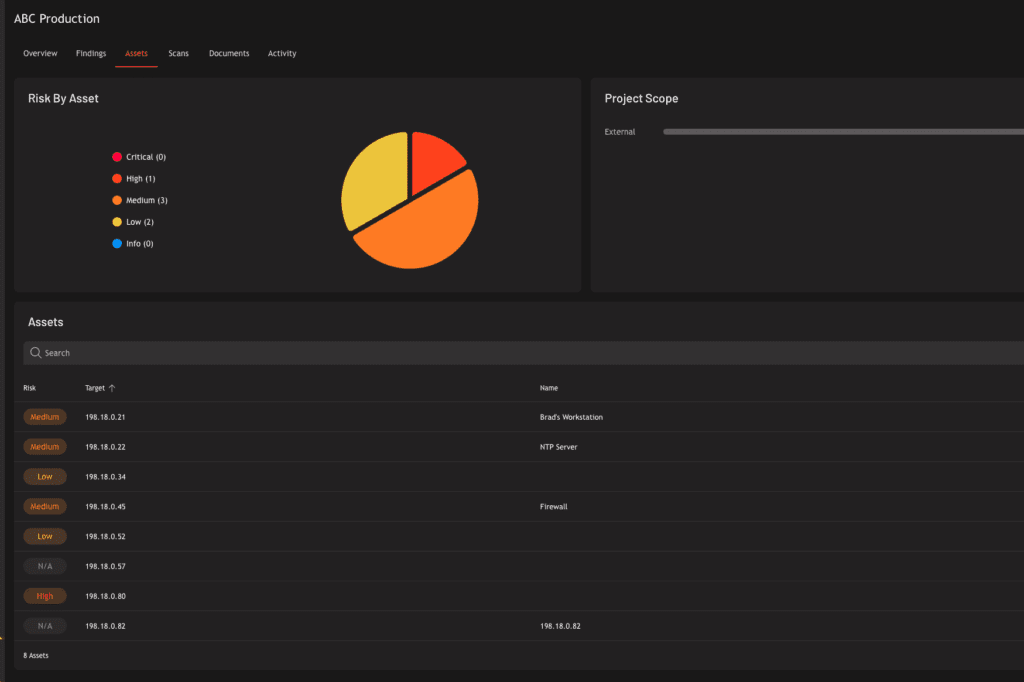
Raxis Attack: Wireless Network PTaaS
Raxis Hack Stories
Our stories are based on real events encountered by Raxis engineers; however, some details have been altered or omitted to protect our customers’ identities.
Attack from the Company Parking Lot
Wireless attackers don’t need access to your buildings in order to initiate an attack, and neither does the Raxis penetration testing team. Sitting in a car in the guest parking area, and using a large antenna easily hidden within the car, our pentester got to work.
First using the AirCrack Suite to discover target SSIDs, our pentester chose one that appeared to be the wireless network used by company employees. Next he used Hostapd-wpe to setup a rogue access point mimicking that SSID and quickly saw users connecting and revealing their user accounts and sometimes the NTLM hashes they used to login. Throwing these hashes into hashcat, our pentester successfully cracked one of them and used the resulting password to login to the wireless network.
While our client had tools in place that alerted them to the rogue access point, our pentester was logged in to the legitimate employee network and looking around by the time they discovered the alert. If they had also required devices to check the certificate of the wireless network before joining, no devices would have attempted to connect to our rogue access point in the first place. With their Raxis report in hand, our client was able to remediate that so that a malicious hacker could not do the same thing.
Choosing the Best Encryption for Your Wireless Network
Raxis CTO Brian Tant explains recent developments in encryption and which is right for your organization.