The Exploit articles categorized as Injection Attacks
-
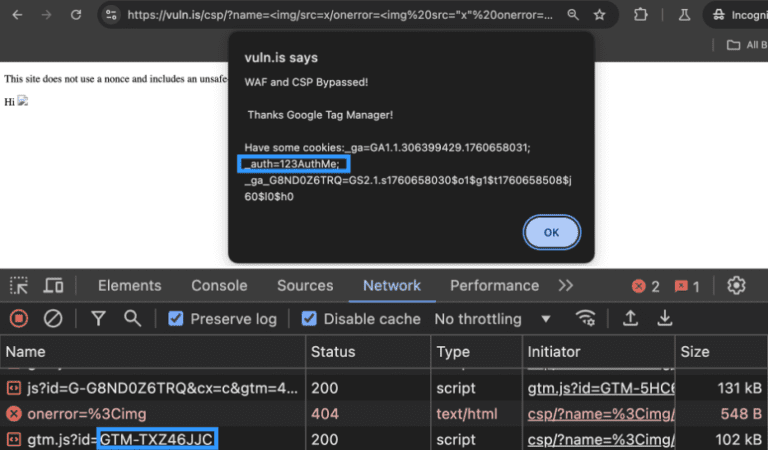
Bypassing a WAF and a CSP with Google Tag Manager: An Attacker’s Perspective and Remediation Advice
By Ryan Chaplin Ryan Chaplin takes an in-depth look at how attackers can use unsafe directives to bypass CSP, notably in Google Tag Manager, and how to remediate the issue. February 10, 2026 -

SQLi Series: SQL Timing Attacks for Penetration Testing
By Andrew Trexler Andrew Trexler’s SQLi Series is back, demonstrating SQL Timing Attacks using MySQL’s sleep function in Blind SQL Injection attacks for penetration testing. May 7, 2024 -

SQLi Series: An Introduction to SQL Injection for Penetration Testing
By Andrew Trexler Raxis’ Andrew Trexler explains what SQL Injection (SQLi) is and how to perform a simple exploit against a web app login page in penetration tests. April 9, 2024 -

Hackers See Opportunity Where You See Only a Button
By Brad Herring In this post, Raxis VP Brad Herring explains how web proxy tools can turn even simple buttons and check-boxes into avenues for an attack. April 1, 2022