A High-Tech Take on an Old-Time Scam
Don’t fall prey to scammers trying to convince you that your domain name is about to be stolen by an overseas company.
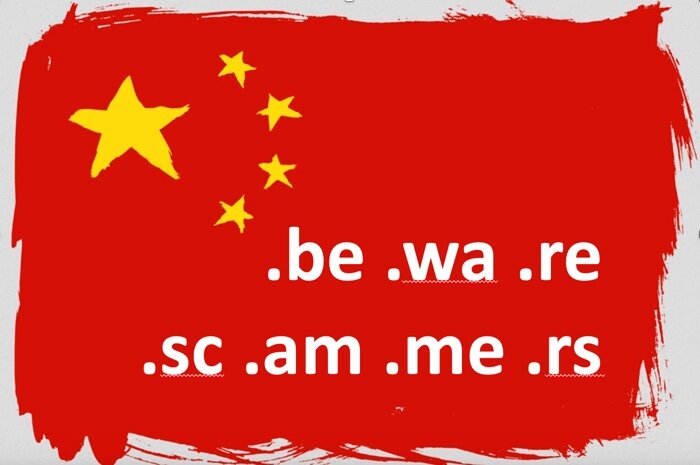
Don’t fall prey to scammers trying to convince you that your domain name is about to be stolen by an overseas company.

Cybersecurity company SonicWall has released patches for three zero-day vulnerabilities that are currently being exploited.

The US government is warning businesses to beware of vulnerabilities being exploited by the Russian Foreign Intelligence Service (SVR RF). But that’s not the only group taking advantage. Here’s what you should do.

Account enumeration reveals whether usernames are valid for use in other attacks. Lead Penetration Tester Matt Dunn explains how it works and how to prevent it.

Should you connect your latest device to the Internet? Lead Penetration Tester Scottie Cole recommends asking yourself some questions before you do.