Jim McClellan, Marketing Director
Raxis’ new marketing director, Jim McClellan, talks about the unusual career path that led from consultant to full-time team member.
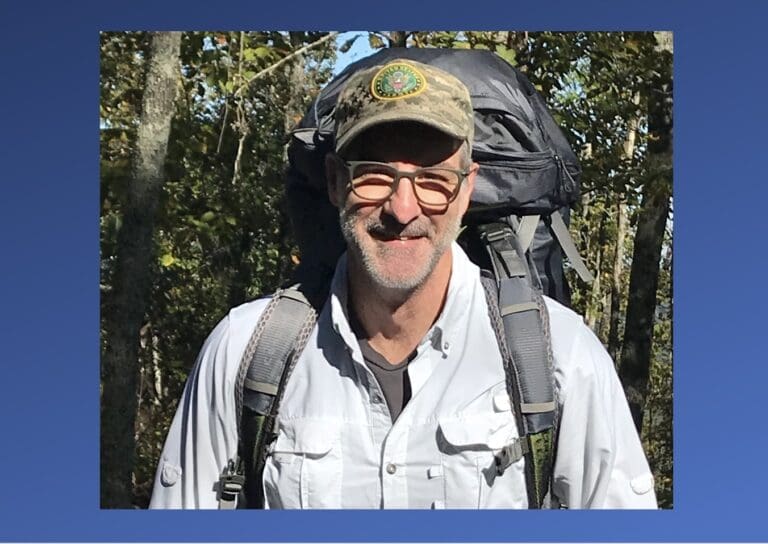
Raxis’ new marketing director, Jim McClellan, talks about the unusual career path that led from consultant to full-time team member.
Is your organization is in the market for a penetration test? Raxis’ COO Bonnie Smyre continues her two-part series on how to hire a penetration testing firm.

The FTC has finalized changes to the GLBA Safeguards Rule. Here’s our take on how they are likely to affect financial institutions’ cybersecurity posture.

Lead penetration tester Matt Dunn continues his discussion about web application testing. In Part Two, Matt explains testing as an authenticated user vs. as an unauthenticated user.