The Exploit articles categorized as Patching
-

BeyondTrust RCE Vulnerability Exploited: Critical 9.9 CVSS Flaw Under Active Attack
By Ryan Chaplin While BeyondTrust patched cloud-hosted Remote Support customers earlier this month, on-premises deployments of BeyondTrust must manually patch to remediate. February 17, 2026 -

CVE-2025-59886 Eaton Exploit Code Published
By Jason Taylor With exploit code available for the vulnerabilities in Eaton’s xComfort Ethernet Communication Interface, Jason Taylor recommends replacing or isolating. February 5, 2026 -

CVE‑2020‑12812 and Why It’s Still an Issue Five Years Later
By Scottie Cole Principal Penetration Tester Scottie Cole explains why Fortinet released a new security advisory about CVE‑2020‑12812 and what your organization should check. January 16, 2026 -

Microsoft Releases Security Patch for Actively Exploited On-Premises SharePoint Vulnerabilities
By Jason Taylor Microsoft has released patches for two critical vulnerabilities allowing unauthenticated remote code execution that affect on-premises SharePoint installations. July 22, 2025 -
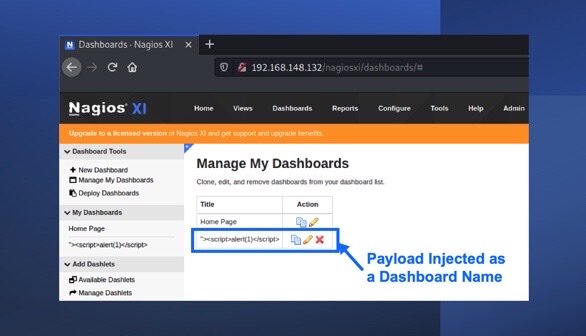
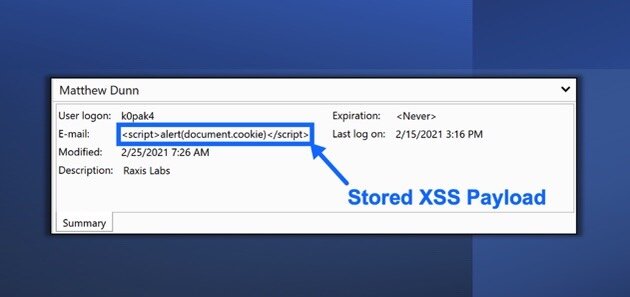
Nagios XI Stored Cross-Site Scripting (XSS): CVE-2021-38156
By Raxis Research Team Nagios is open-source network and system monitoring software. Raxis’ Matt Dunn has discovered a cross-site scripting vulnerability that could leave users open to attack. September 17, 2021 -
PRTG Network Monitor Stored Cross-Site Scripting Vulnerability (CVE-2021-29643)
By Raxis Research Team Raxis lead penetration tester Matt Dunn uncovers a new vulnerability in the PRTG Network Monitor (CVE-2021-29643). Read more here. August 20, 2021