The Exploit articles categorized as AI
-

Bypassing ChatGPT’s Open-Source Model Security Restrictions for Agentic Hacking
By Ryan Chaplin Ryan Chaplin wondered what it would take to bypass ChatGPT’s open-source model security restrictions to allow AI to hack his website. See how he did it here. May 5, 2026 -

Deepfakes: The Face on Your Screen Might Not Be Real
By Scottie Cole Phishing and other social engineering techniques have crossed a threshold with deepfake attacks. Scottie Cole discusses how to protect your organization. April 17, 2026 -
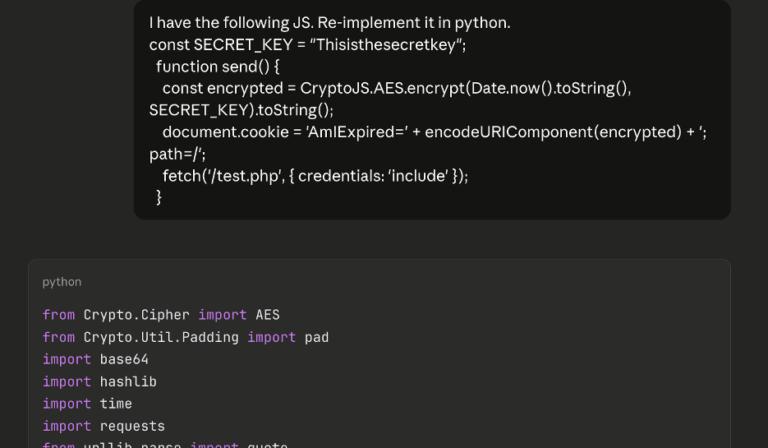
AI-Augmented Series: AI Scripting for Brute-Forcing on a Web App Pentest
By Andrew Trexler On a recent web app pentest, Andrew Trexler used AI to find client-side code that stopped his brute-force attack then used AI again to thwart that code. March 4, 2026 -

BeyondTrust RCE Vulnerability Exploited: Critical 9.9 CVSS Flaw Under Active Attack
By Ryan Chaplin While BeyondTrust patched cloud-hosted Remote Support customers earlier this month, on-premises deployments of BeyondTrust must manually patch to remediate. February 17, 2026 -

The Future of Security: Why AI-Augmented Penetration Testing Is the Way Forward
By Mark Puckett Raxis CEO Mark Puckett looks back at a year of many changes and forward to the ways AI-augmented pentesting is changing the industry. December 30, 2025 -

Autonomous Supply-Chain Worm Compromises Postman, PostHog, Zapier, and 26k Others
By Ryan Chaplin Operating fully autonomously, this new supply-chain malware has compromised Postman, PostHog, Zapier and 26k others. Learn what your organization should do now. December 10, 2025