The Exploit articles categorized as Penetration Testing
-

Understanding PTaaS: Penetration Testing as a Service
By Bonnie Smyre What does Penetration Testing as a Service (PTaaS) really mean? In this blog we discuss the details and how do you find the best PTaaS for your organization. March 5, 2025 -
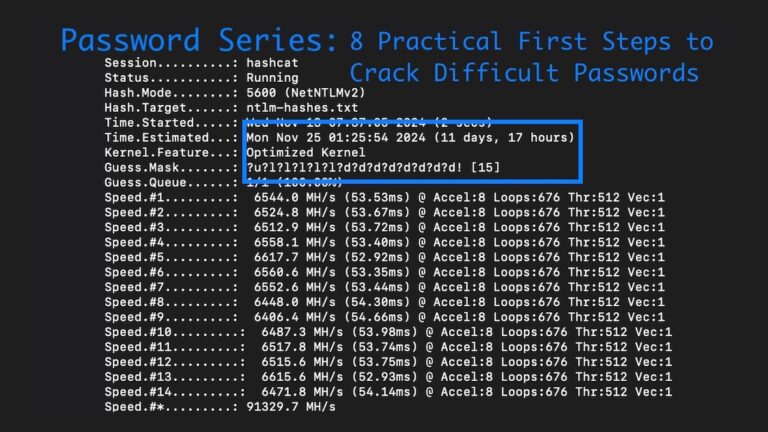
Password Series: 8 Practical First Steps to Crack Difficult Passwords in Penetration Tests
By Ryan Chaplin From rulesets & hardware to wordlists and mask attacks, Lead Penetration Tester Ryan Chaplin shows how to crack difficult password hashes in penetration tests. February 25, 2025 -
Tips for Scoping Your Penetration Test
By Brad Herring Scoping your penetration test (especially your first one) can be daunting. Our team is always happy to help, and Brad Herring gives you a head start here. January 28, 2025 -
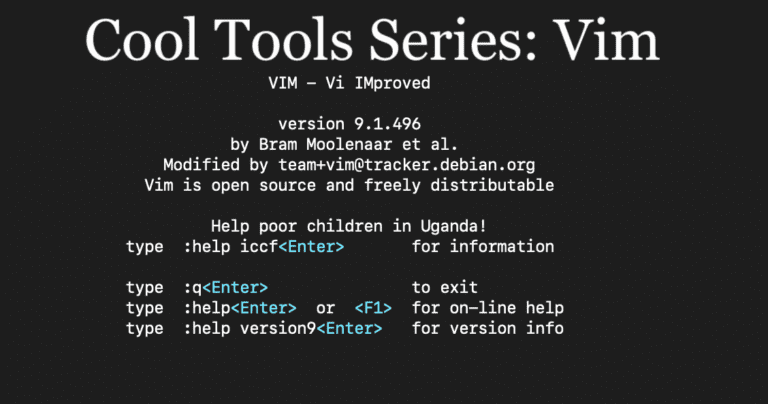
Cool Tools Series: How Vim Powers Penetration Testing
By Andrew Trexler Principal Penetration Tester, Andrew Trexler, dives into Vim, a powerful command line tool for text files, and shows useful commands for penetration testing. January 14, 2025 -

Accepting Penetration Test Risks & How Compensating Controls Can Help
By Tim Semchenko Tim Semchenko discusses documenting acceptance of risks and implementing compensating controls as options when pentest findings cannot be fixed immediately. December 17, 2024 -
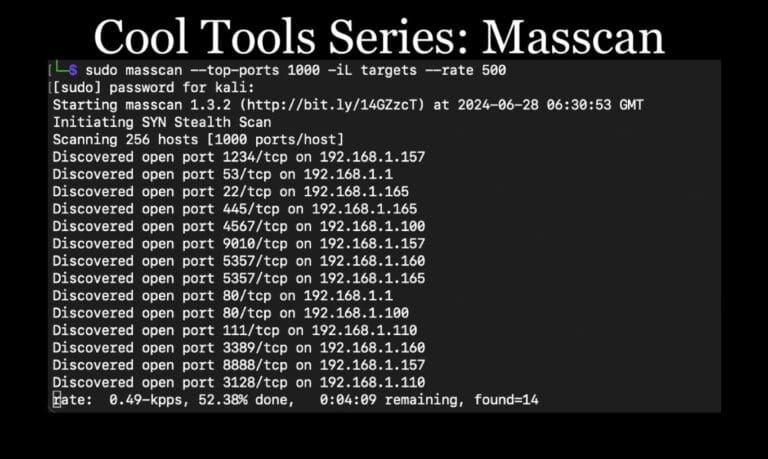
Cool Tools Series: Masscan for Penetration Testing
By Andrew Trexler Continuing our Cool Tools Series, Lead Penetration Tester Andrew Trexler shows how to use masscan for discovery scanning on large networks in penetration tests. December 3, 2024