Cross-Site Scripting (XSS): Filter Evasion and Sideloading
In this second in a series, learn how to perform Cross-Site Scripting (XSS) attacks such as filter evasion and sideloading content.

In this second in a series, learn how to perform Cross-Site Scripting (XSS) attacks such as filter evasion and sideloading content.

This video covers the basics of cross-site scripting, including reflected, stored, and DOM-based XSS as well as remediation to protect against these attacks.
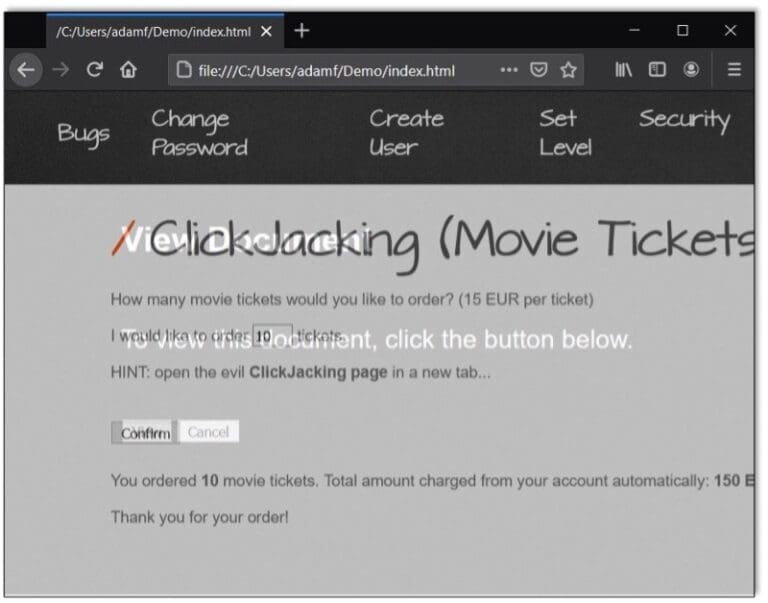
Raxis’ Lead Developer Adam Fernandez discusses clickjacking, explaining what it is and why it represents less of a threat now than it once did. Adam also talks about how clickjacking differs from similar attacks.

Phish attacks are a significant threat to all organizations. In this video Raxis’ Scottie Cole shares tips and tricks for phishing assessments.
LDAP passback exploits are easy when companies fail to change default passwords on network devices or fail to assign a password at all. If you connect it, you must protect it.