The Exploit articles categorized as How To
-
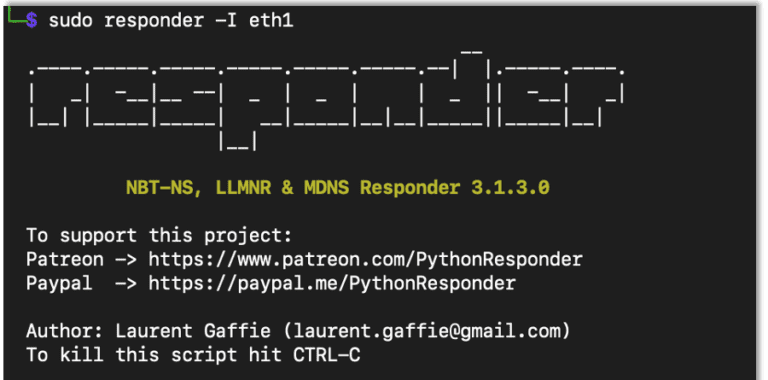
AD Series: How to Perform Broadcast Attacks Using NTLMRelayx, MiTM6 and Responder for Penetration Tests
By Andrew Trexler Andrew Trexler continues his AD Series with an in-depth tutorial on broadcast Attacks using NTLMRelayx, MiTM6 and Responder for penetration tests. June 19, 2023 -

How to Create an AD Test Environment to Use for Penetration Testing
By Andrew Trexler Andrew Trexler walks us through creating a simple AD test environment to test new hacks before trying them on a penetration test. April 27, 2023 -
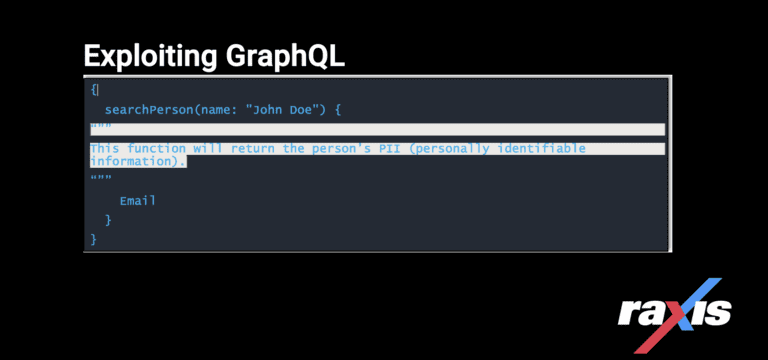
Exploiting GraphQL for Penetration Testing
By bjager Exploiting GraphQL, a query language inspired by the structure & functionality of online data storage & collaboration platforms Meta, Instagram & Google Sheets. March 28, 2023 -
Log4j: How to Exploit and Test this Critical Vulnerability on Penetration Tests
By Mark Puckett Raxis demonstrates how to obtain a remote shell on a target system during penetration tests using a Log4j open-source exploit available to all. (CVE-2021-44228) November 18, 2022 -
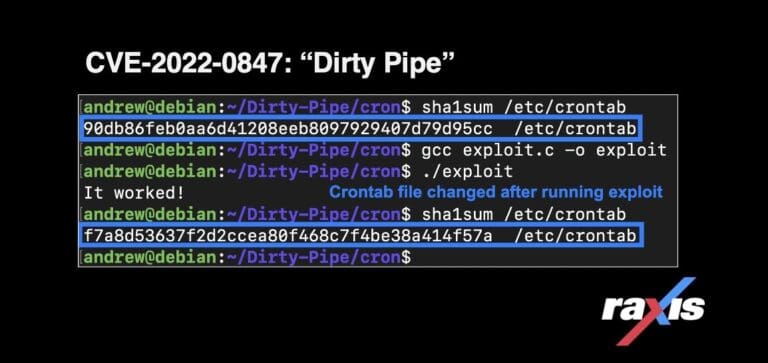
Exploiting Dirty Pipe (CVE-2022-0847)
By Andrew Trexler The Dirty Pipe vulnerability (CVE-2022-0847) allows any user to write to read-only files, including files that are owned by root, allowing privilege escalation. May 26, 2022 -

Hackers See Opportunity Where You See Only a Button
By Brad Herring In this post, Raxis VP Brad Herring explains how web proxy tools can turn even simple buttons and check-boxes into avenues for an attack. April 1, 2022