The Exploit articles categorized as How To
-

How to Pull Off a Mousejacking Attack
By Raxis Research Team Raxis’ penetration testing team demonstrates how to conduct a mousejacking attack to gain access as part of a penetration test. February 5, 2021 -
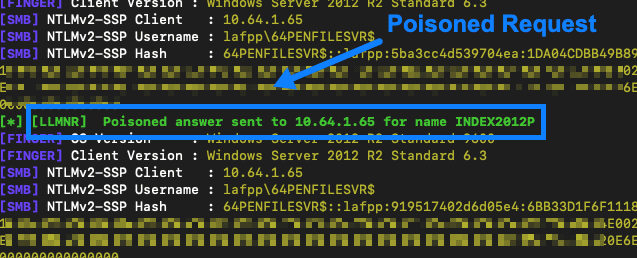
AttackTek: How to Launch a Broadcast Resolution Poisoning and SMB Relay Attack
By Raxis Research Team Learn an easy, effective way to test corporate networks with broadcast poisoning and SMB relay attacks used in tandem from the Raxis penetration testing team. September 25, 2020 -
Goodies for Hoodies: TCP Timestamps
By Brian Tant Does your penetration test always return a low-risk finding about TCP Timestamps? Why worry about it? Because it gives hackers info to use in other attacks. June 4, 2018 -
IKE VPNs Supporting Aggressive Mode
By Bonnie Smyre In this post we’ll look at why IKE VPNs with Aggressive Mode enabled continue to be a vulnerability, how it can be exploited, and how to mitigate this risk. May 23, 2018 -

Raxis API Tool
By Bonnie Smyre Raxis Lead Developer, Adam Fernandez, has developed a tool to use for testing JSON-based REST APIs, and we’re sharing this tool on GitHub to help API developers test their own code during the SDLC process and to prepare for third-party API penetration tests. May 4, 2018 -

The Weakest Link in the Password Hash
By Brad Herring Raxis VP of Business Development explains easy rules to use to make your passwords more secure and harder for hackers to crack. October 16, 2016