The Exploit articles categorized as How To
-

Data Theft Exploit Part 1: DNS Exfiltration Setup
By Jason Taylor Raxis Lead Penetration Tester Jason Taylor’s in-depth tutorial explains setting up a server for DNS exfiltration. Check back next month to run the attack. December 16, 2025 -

PSE & Red Team Series: Badge Cloning
By Nathan Anderson Lead Penetration Tester Nathan Anderson is back with more PSE and red team advice, this time looking into three tools he uses to clone badges and gain access. October 21, 2025 -

Lateral Movement: From Beachhead to Breach
By Nate Jernigan Raxis Senior Penetration Tester Nate Jernigan discusses lateral movement in penetration testing and the methods and tools he uses when performing these attacks. September 23, 2025 -
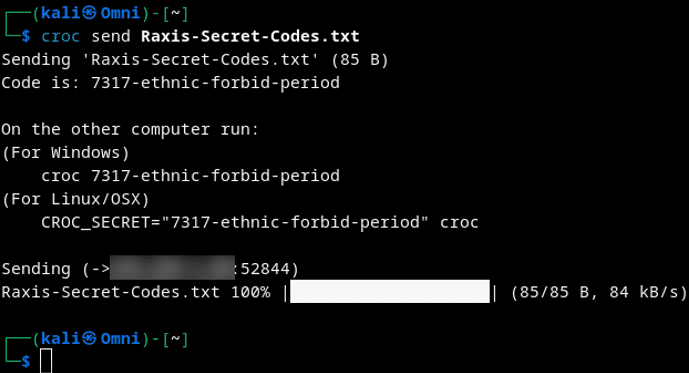
Cool Tools Series: Croc for Secure Data Exfiltration
By Nathan Anderson Lead Penetration Tester Nathan Anderson provides tips on using croc for secure data exfiltration just like he does on red team engagements. September 9, 2025 -

PSE & Red Team Series: The Power of Grip to Enhance the Under-Door Tool
By Brad Herring In this next post in our PSE and Red Team Series, Brad Herring explains how to use gaffer’s tape or heat-shrink tubing to make an under-door tool easier to use. August 12, 2025 -
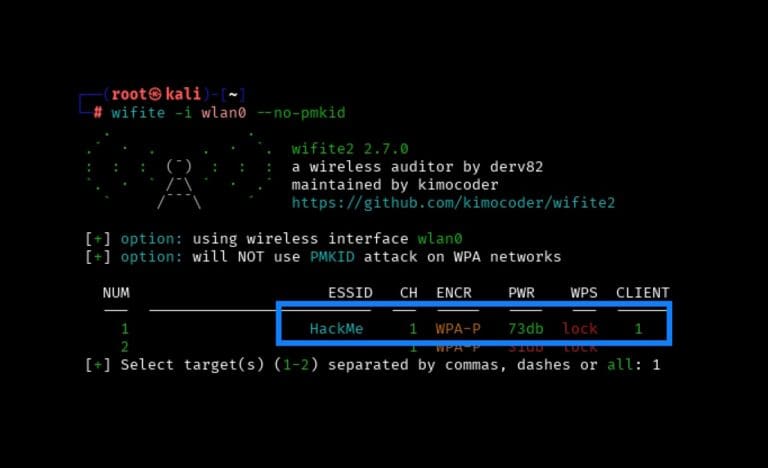
Wireless Series: Using Wifite to Capture and Crack a WPA2 Pre-Shared Key for Penetration Testing
By Scottie Cole Principal Penetration Tester Scottie Cole begins our wireless penetration testing series with capturing and cracking a WPA2 Pre-Shared Key using Wifite. June 17, 2025