The Exploit articles categorized as How To
-
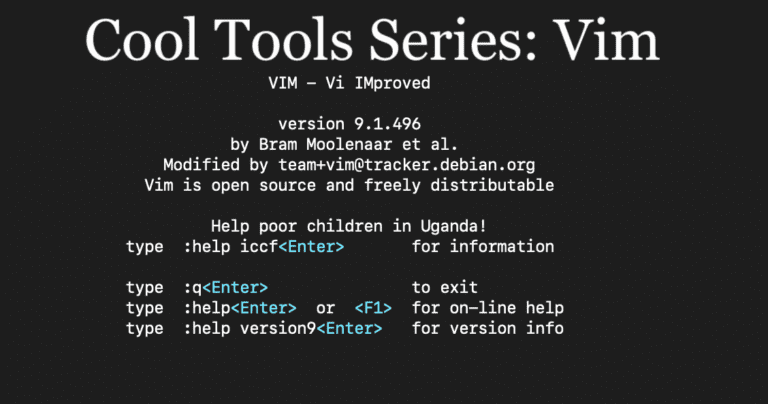
Cool Tools Series: How Vim Powers Penetration Testing
By Andrew Trexler Principal Penetration Tester, Andrew Trexler, dives into Vim, a powerful command line tool for text files, and shows useful commands for penetration testing. January 14, 2025 -
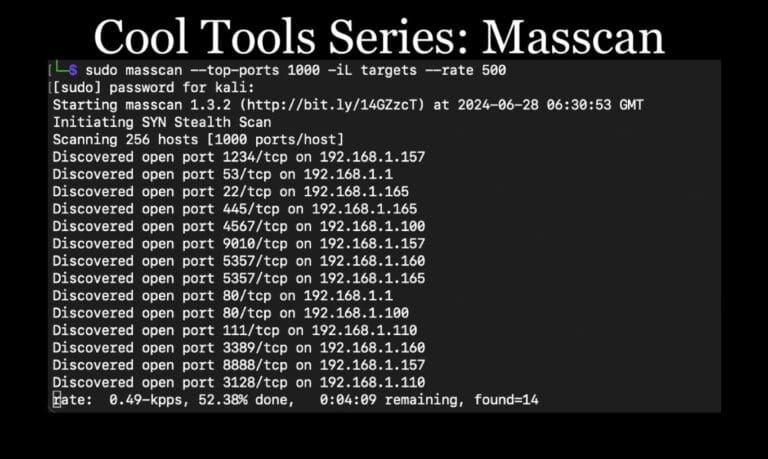
Cool Tools Series: Masscan for Penetration Testing
By Andrew Trexler Continuing our Cool Tools Series, Lead Penetration Tester Andrew Trexler shows how to use masscan for discovery scanning on large networks in penetration tests. December 3, 2024 -

Password Series: Defeating Emerging Password Security Trends with Psudohash for Penetration Testing
By Ryan Chaplin Lead Pentester Ryan Chaplin discusses emerging improvements in password security and how Psudohash can help bypass them on penetration tests. November 5, 2024 -

Cool Tools Series: How MSFvenom Powers Penetration Testing
By Nathan Anderson Nathan Anderson intros MSFvenom, a Metasploit tool that generates & encodes payloads to obtain reverse shells & gain network access for penetration testing. October 8, 2024 -
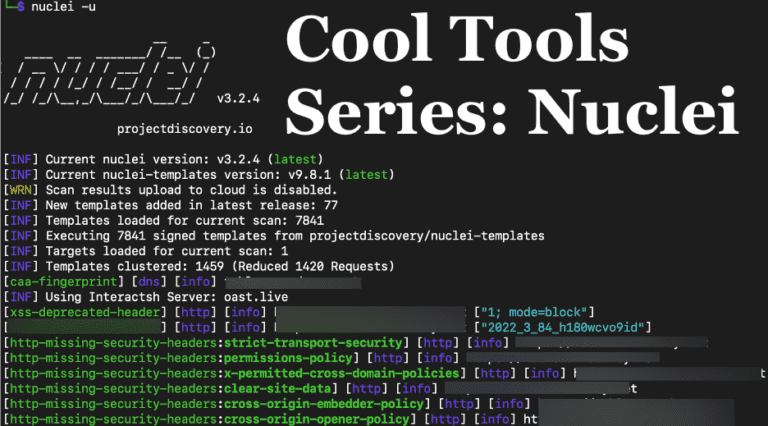
Cool Tools Series: Nuclei for Penetration Tests
By Andrew Trexler Raxis’ Andrew Trexler shows how useful Nuclei is for network and application penetration tests, discovering vulnerabilities such as default passwords and more. September 10, 2024 -
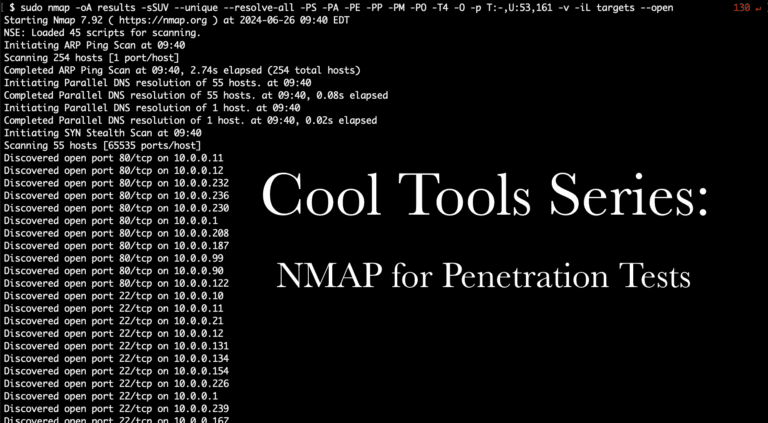
Cool Tools Series: NMAP for Penetration Tests
By Adam Fernandez Raxis’ lead developer, Adam Fernandez, adds to our Cool Tools Series with a focus on Nmap: discovering live hosts that appear to be down and useful NSE scripts. July 30, 2024