The Exploit articles categorized as Social Engineering
-

Deepfakes: The Face on Your Screen Might Not Be Real
By Scottie Cole Phishing and other social engineering techniques have crossed a threshold with deepfake attacks. Scottie Cole discusses how to protect your organization. April 17, 2026 -

PSE & Red Team Series: Social Engineering
By Nathan Anderson Lead Penetration Tester Nathan Anderson is back with more PSE and red team tips, including tailgating, impersonating, and pretexts to gain onsite access. January 27, 2026 -

CrowdStrike Fires Insider Who Shared Screens Externally
By Andrew Trexler Though hacker groups claimed to have access to internal systems, CrowdStrike announced they fired an insider who shared external screens with the attackers. December 1, 2025 -

PSE & Red Team Series: Badge Cloning
By Nathan Anderson Lead Penetration Tester Nathan Anderson is back with more PSE and red team advice, this time looking into three tools he uses to clone badges and gain access. October 21, 2025 -
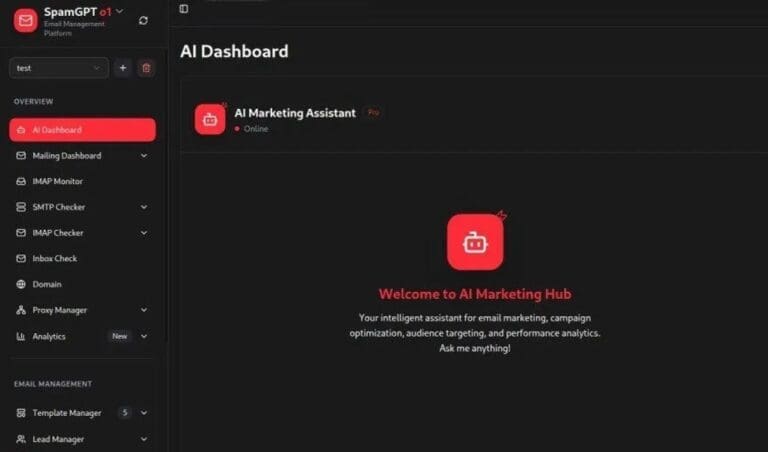
SpamGPT: Protecting Your Company From Large-Scale Phishing
By Nathan Anderson SpamGPT, a complex phishing and social engineering suite has made the news recently. Learn what it is and how organizations can protect their employees. October 9, 2025 -

Lessons from the DaVita Healthcare Ransomware Attack
By Brian Tant The DaVita ransomware attack is one of the most impactful recent healthcare breaches. Learn what happened and what could have been done to limit the impact. September 18, 2025