Written by Raxis Research Team
I’m Matt Dunn, lead penetration tester here at Raxis.This is a summary of the third stored cross-site scripting vulnerability I discovered while testing several Zoho-owned ManageEngine products. This vulnerability exists in the Applications Manager product.
Summary
Recently I discovered a stored Cross-Site Scripting vulnerability in ManageEngine Applications Manager. The vulnerability exists in a users’ name fields when they are imported from Active Directory. This can be performed in any of the name fields and is executed when selecting the user for import on /admin/userconfiguration.do after fetching users from the domain. After the import loads and the user is selected, the user’s name is loaded with unescaped content, allowing malicious JavaScript to be reflected back to the user.
Proof of Concept
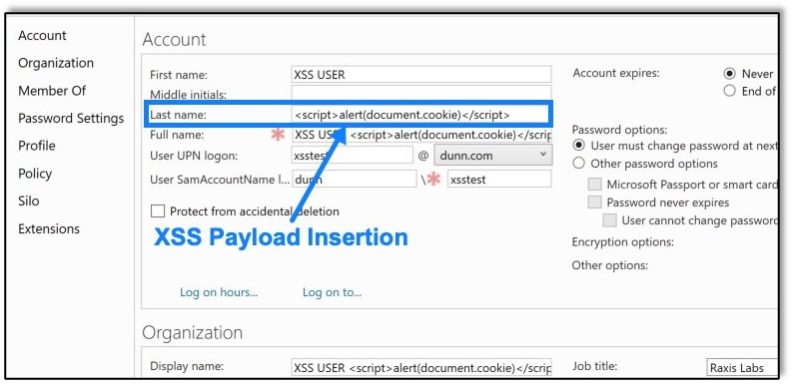
The vulnerability can be triggered by inserting html content, specifically script tags, into the first or last name of an Active Directory user. The following was inserted as a proof of concept to reflect the user’s cookie in an alert box:
<script>alert(document.cookie)</script>An example of this in the Last Name field of one such user can be seen here:
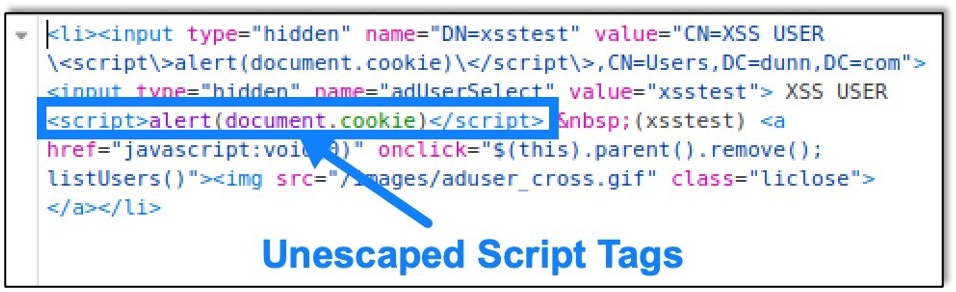
After that user is selected and the details load on the “User Imported from Active Directory” page, the HTML is presented unescaped on the web page, which allows the script tags to be loaded as valid JavaScript. The unescaped HTML as loaded can be seen here:
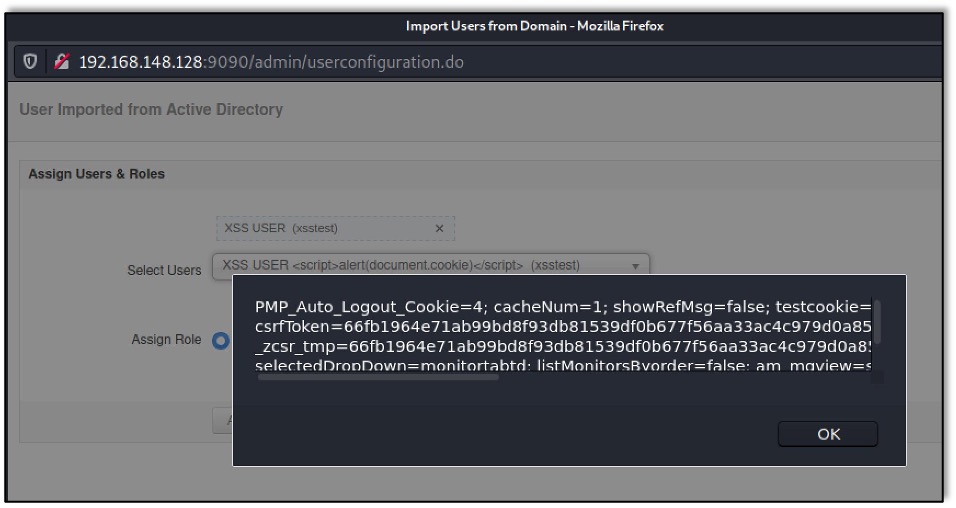
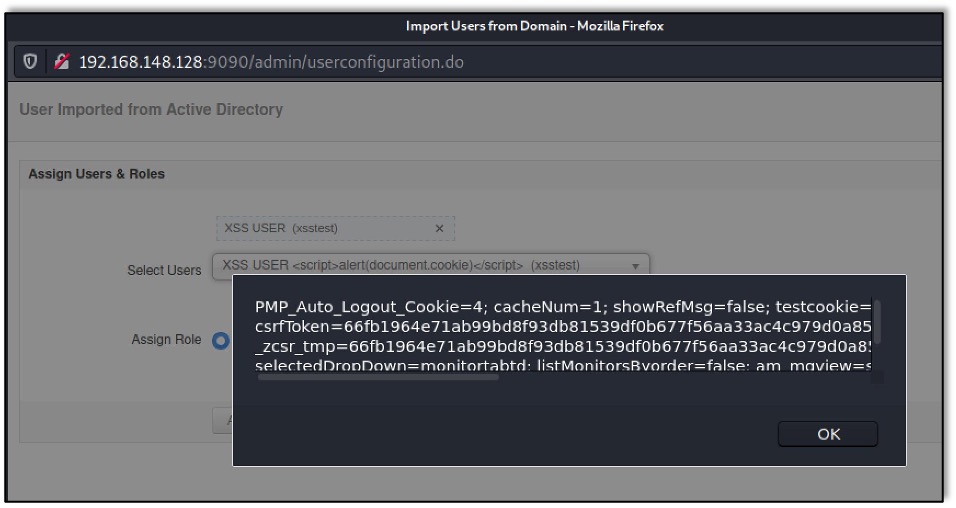
After loading the selected user, the malicious content is executed, as shown below:
Affected Versions
Raxis discovered this vulnerability on Manage Engine Applications Manager 15, Build 15080.
Remediation
Upgrade ManageEngine Applications Manager to Version 15.1 Build 15130 or later immediately which can be found here:
- Download Link – https://www.manageengine.com/products/applications_manager/download.html
- Release Notes – https://www.manageengine.com/products/applications_manager/release-notes.html
Disclosure Timeline
- March 18, 2021 – Vulnerability reported to Zoho
- March 18, 2021 – Zoho begins investigation into report
- April 27, 2021 – Zoho releases fixed version 15.1 Build 15130
- April 27, 2021 – CVE-2021-31813 is assigned to this vulnerability
CVE Links

Raxis Research Team
Search The Exploit Blog
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless