Written by Brian Tant
Red Teams, Blue Teams, and Purple Teams are terms used in cybersecurity to describe different approaches to testing and improving security measures within an organization. Red Teams and Blue Teams – and working together, Purple Teams – each play a key role in the cybersecurity process, and, when used effectively, they can help identify and mitigate vulnerabilities and improve an organization’s overall security posture.
What They Are
Red Teams
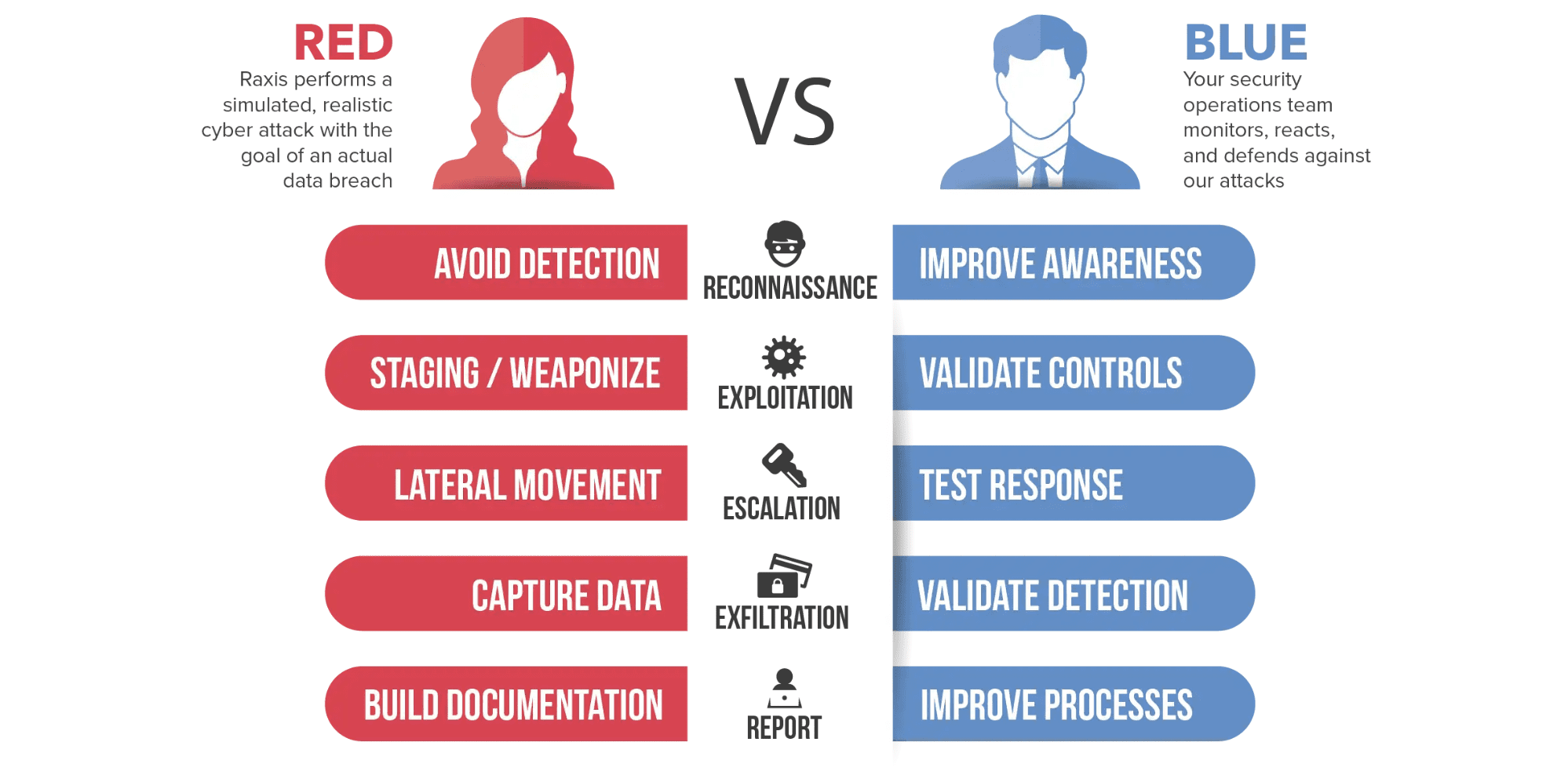
Red Teams are offensive security teams that simulate cyberattacks against an organization. They act as adversaries, attempting to breach an organization’s defenses using the same tools, techniques, and procedures as real attackers in order to identify vulnerabilities and weaknesses in an organization’s security posture before real attackers can exploit them. Red Teams use techniques such as penetration testing and social engineering to assess the organization’s security.
Blue Teams
Blue Teams are defensive security teams that are responsible for maintaining and improving the organization’s security posture. They work to detect, respond to, and prevent cyberattacks and security incidents. Blue Teams are often responsible for implementing and managing security tools and technologies, monitoring network traffic for signs of malicious activity, and responding to security incidents when they occur. They may also work closely with Red Teams to understand and address vulnerabilities identified during testing.
Purple Teams
Purple Teams combine elements of both Red Teams and Blue Teams. They focus on collaboration and communication between the offensive and defensive teams to improve overall security. Purple Teams often work together to develop and test security controls, identify and prioritize vulnerabilities, and improve incident response processes. By working together, Red and Blue Teams can better understand each other’s perspectives and improve an organization’s security posture.

How They Can Help You
These teams are useful because they provide a structured and systematic approach to testing and improving security. By simulating real-world attacks, organizations can identify and address vulnerabilities before they are exploited by real attackers.
Additionally, by working together in a Purple Team, Red Teams and Blue Teams can improve communication and collaboration, leading to more effective security measures. Overall, these teams help organizations identify and mitigate security risks, protect sensitive data, and maintain the trust of their customers and stakeholders.
What It’s Like to Take Part in a Red Team
All cybersecurity companies are different, so we’ll focus on the Raxis Red Team. First, you scope the Red Team. While a full scope of all of your physical locations, employees, applications, and networks is most like a malicious hacker’s landscape, Raxis works with you to make necessary exclusions, such as critical medical devices or sensitive locations.
With the scope in mind, the Raxis Red Team gets started. Much like a crime drama, the early stages of the test are slow. The team carefully researches the target company for possible weaknesses and entry points, from physical information (locked doors, badge readers, cameras, etc.) to network infrastructure (websites, VPNs, operating systems, etc.).
Using employee lists found on sites such as social media, company websites, and tools that scour the internet for employee information, the Red Team often begins the attack with small spear phishing campaigns. Unlike large phishing tests to train your employees, these are aimed to stay below the radar and to get results. Often spear phishing emails encourage the target to call Red Team members in order to build trust before attempting to discover sensitive information. In other cases, our team has sent emails that lead employee targets to open phishing webpages immediately and enter usernames and passwords.
During a Red Team, testers are standing by to receive and use that information. Even if an employee gets suspicious and changes their password, a Red Team may already be inside the network. If that same password was reused for multiple systems, the Red Team may have further access unless the employee remembers to change the password on each system. All of this can be accomplished remotely using external network systems that the Red Team discovers.

Once credentials are in hand, the Red Team moves to the next level. From sitting in a parking lot with a powerful antenna accessing the organization’s wireless network to entering a building and installing a device on the internal network, the credentials acquired above take on new urgency as they have the potential to be used on any system on the internal or wireless networks as well as the external network.
Why Take Part in a Red Team?
The power of a Red Team is that almost everything is in play. As malicious attackers use anything they can find to piece together an attack, so can your Red Team. These tests are less about reporting on every issue you should fix and more about showing your organization what an attacker could accomplish against your systems.
Past Raxis Red Team engagements have discovered vulnerabilities that may look small on their own but, together, give Raxis full and persistent access to organizations’ networks and buildings. Our teams have tailgated into buildings, casually walked past or talked their way past security guards, cloned badges (even for data centers) to gain unquestioned access, planted devices that allow remote access to internal systems, sent phishing emails to employees as employees, gained domain administrator access via wireless networks, and more.
Red Teams Benefit You
Often a first impression while thinking about performing a Red Team test is that your organization will fail or that it will be a painful experience. We encourage you to think about it more positively. A Red Team, whether through Raxis or another reputable firm, gives your team information to strengthen your physical and network security controls and also gives you real-world examples that show your employees the importance of keeping security at top of mind.

One last story. In one Red Team engagement, Raxis initially gained access via a successful spear phish that provided a username and password that worked on the organization’s internal production wireless network. While this employee fell for the phish initially, he contacted IT within a day to say that he had seen strange activity in his account. IT blew him off and said it was fine. How do we know? Because our Red Team was monitoring his emails.
It took Raxis more than one day to use those credentials to gain persistent access to the network. If IT has listened to the employee and reset his password, our team would have been back at square one. That is a powerful message commending the employee for alerting IT and helping IT recognize that it’s always best to be safe rather than sorry.
Purple Teams Provide Even More Insight
For a Purple Team engagement, Raxis team members work both offense and defense. While the Red Team performs as usual, another Raxis team member also works with your Blue Team to both watch and assess and, sometimes, to guide. In the end, a Purple Team report includes (in addition to a full Red Team report) an evaluation of your Blue Team’s activities as well as advice on how to strengthen them for the future.
If your organization has an internal Red Team or has performed external Red Team tests in the past, a Purple Team engagement can be the next step to strengthen your Blue Team. The Raxis team member working with your Blue Team is kept apprised of what the Red Team is doing. If your Blue Team catches the Red Team, great! If not, the Raxis team member will evaluate your Blue Team’s actions and may – depending on your scope – guide them on key points.

Brian Tant
Search The Exploit Blog
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless