The Exploit articles categorized as Exploits
-

How to Pull Off a Mousejacking Attack
By Raxis Research Team Raxis’ penetration testing team demonstrates how to conduct a mousejacking attack to gain access as part of a penetration test. February 5, 2021 -

Imminent Threat for US Hospitals and Clinics, RYUK Ransomware Alert (AA20-302A) – Updated 11/2/2020
By Brian Tant A new nationwide cyberattack appears to be targeted at U.S. based hospitals, clinics, and other health care facilities. Healthcare on heightened alert. October 29, 2020 -

Why Tailgating is an Effective Hacker Tactic
By Bonnie Smyre We’re conditioned to be helpful and accommodating. That’s why tailgating works so well for hackers. The Raxis penetration testing team shows how. October 9, 2020 -
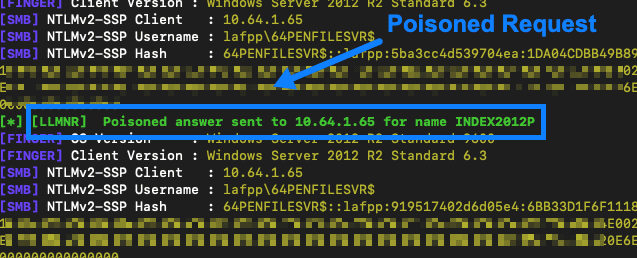
AttackTek: How to Launch a Broadcast Resolution Poisoning and SMB Relay Attack
By Raxis Research Team Learn an easy, effective way to test corporate networks with broadcast poisoning and SMB relay attacks used in tandem from the Raxis penetration testing team. September 25, 2020 -

Understanding the Why Behind Password Management
By Bonnie Smyre In this video, Raxis CTO Brian Tant explains why password mismanagement is still one of the most reliable ways to breach a company network and what you can do to secure your network. July 10, 2020 -

3 Steps You Should Take Right Now to Reduce Your Risk of a Cyberattack
By Brian Tant In this video, Raxis CTO Brian Tant talks about three steps you should take to secure your network against hackers. June 22, 2020