The Exploit articles categorized as Exploits
-

Cool Tools Series: How MSFvenom Powers Penetration Testing
By Nathan Anderson Nathan Anderson intros MSFvenom, a Metasploit tool that generates & encodes payloads to obtain reverse shells & gain network access for penetration testing. October 8, 2024 -
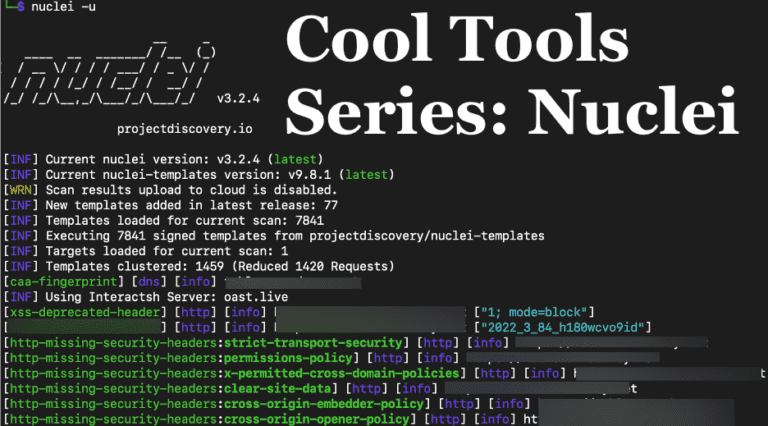
Cool Tools Series: Nuclei for Penetration Tests
By Andrew Trexler Raxis’ Andrew Trexler shows how useful Nuclei is for network and application penetration tests, discovering vulnerabilities such as default passwords and more. September 10, 2024 -

Password Length: More than Just a Question of Compliance
By Brian Tant Password length requirements are a key part of password security, but, with PCI, NIST, OWASP, and CIS offering different recommendations, what length is best? June 4, 2024 -

SQLi Series: SQL Timing Attacks for Penetration Testing
By Andrew Trexler Andrew Trexler’s SQLi Series is back, demonstrating SQL Timing Attacks using MySQL’s sleep function in Blind SQL Injection attacks for penetration testing. May 7, 2024 -

SQLi Series: An Introduction to SQL Injection for Penetration Testing
By Andrew Trexler Raxis’ Andrew Trexler explains what SQL Injection (SQLi) is and how to perform a simple exploit against a web app login page in penetration tests. April 9, 2024 -
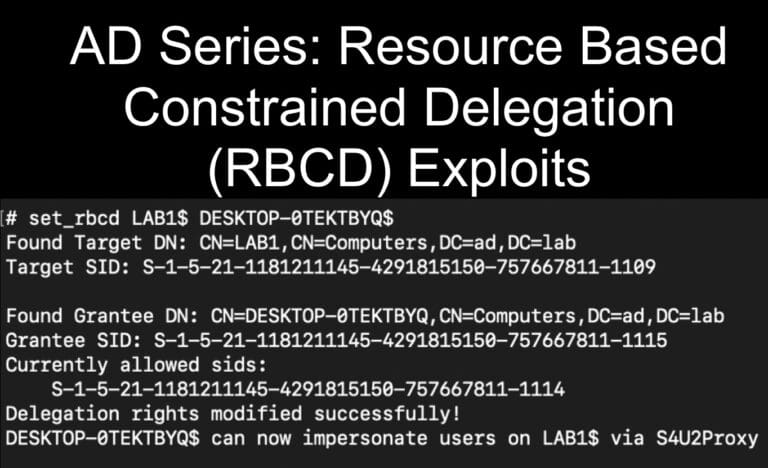
AD Series: Resource Based Constrained Delegation (RBCD) for Penetration Testing
By Andrew Trexler Exploit msDS-AllowedToActOnBehalfOfOtherIdentitity to gain administrative access in a Resource Based Constrained Delegation (RBCD) attack on penetration tests. March 12, 2024