The Exploit articles categorized as Networks
-
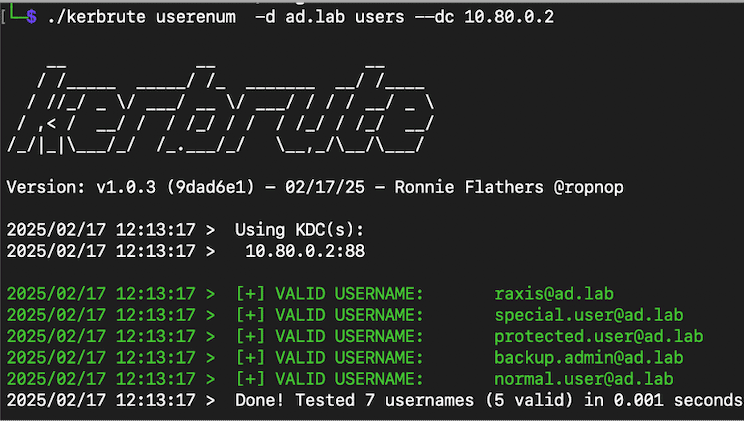
Cool Tools Series: Kerbrute
By Andrew Trexler Raxis Principal Penetration Tester Andrew Trexler walks through the many uses of Kerbrute from user enumeration to brute-forcing and password spraying. October 7, 2025 -

Lateral Movement: From Beachhead to Breach
By Nate Jernigan Raxis Senior Penetration Tester Nate Jernigan discusses lateral movement in penetration testing and the methods and tools he uses when performing these attacks. September 23, 2025 -

Lessons from the DaVita Healthcare Ransomware Attack
By Brian Tant The DaVita ransomware attack is one of the most impactful recent healthcare breaches. Learn what happened and what could have been done to limit the impact. September 18, 2025 -
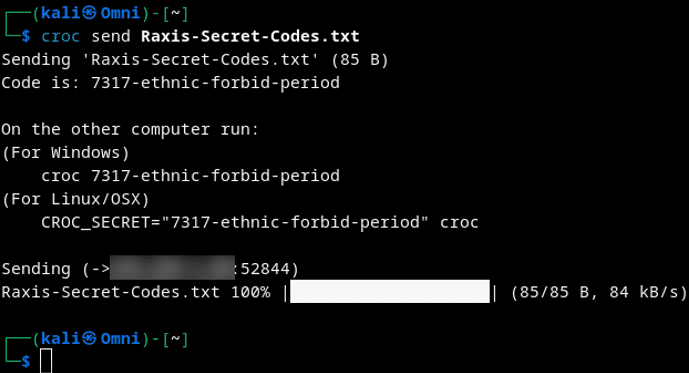
Cool Tools Series: Croc for Secure Data Exfiltration
By Nathan Anderson Lead Penetration Tester Nathan Anderson provides tips on using croc for secure data exfiltration just like he does on red team engagements. September 9, 2025 -
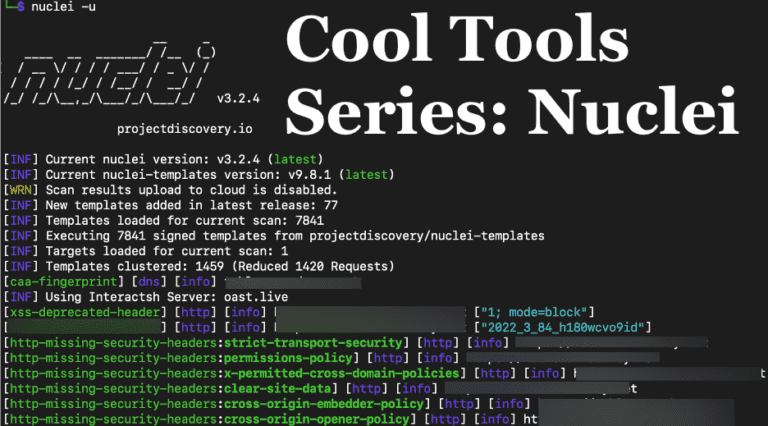
Cool Tools Series: Nuclei for Penetration Tests
By Andrew Trexler Raxis’ Andrew Trexler shows how useful Nuclei is for network and application penetration tests, discovering vulnerabilities such as default passwords and more. September 10, 2024 -
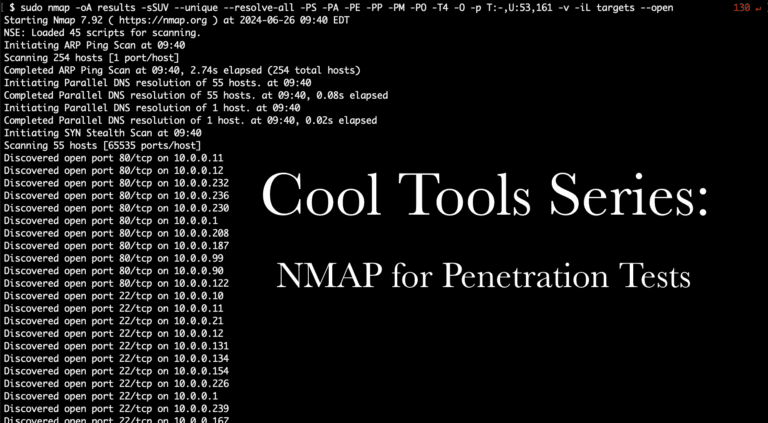
Cool Tools Series: NMAP for Penetration Tests
By Adam Fernandez Raxis’ lead developer, Adam Fernandez, adds to our Cool Tools Series with a focus on Nmap: discovering live hosts that appear to be down and useful NSE scripts. July 30, 2024