The Exploit articles categorized as Security Recommendations
-

Monitor. Detect. Alert. It’s worth the effort.
By Brian Tant Do you monitor effectively for threats on your network? How well does your team respond? Testing can help you find out for sure. August 28, 2020 -
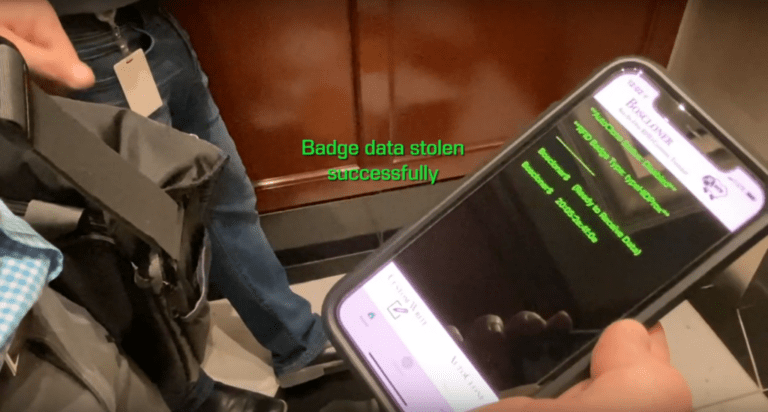
Badge Cloning is Easier Than You’d Expect
By Raxis Research Team Badge cloning can happen in an instant without your employees even noticing. Our penetration testing team shows how it’s done and how you can stay secure. August 21, 2020 -

Securing Your Wireless Network
By Bonnie Smyre What’s the best encryption for your company’s wireless network? Raxis CTO Brian Tant explains the details and why securing your wireless network is critical. August 7, 2020 -

What to Expect When You’re Expecting a (Raxis) Penetration Test
By Bonnie Smyre You know you need to do penetration testing, but you’re not sure how it works. Raxis COO Bonnie Smyre explains how we work. July 31, 2020 -

Securing the Internet of Things
By Bonnie Smyre Any connected device is a potential vulnerability. Watch and find out how to secure your smart thermostat. July 24, 2020 -

Understanding the Why Behind Password Management
By Bonnie Smyre In this video, Raxis CTO Brian Tant explains why password mismanagement is still one of the most reliable ways to breach a company network and what you can do to secure your network. July 10, 2020