Exploit
-
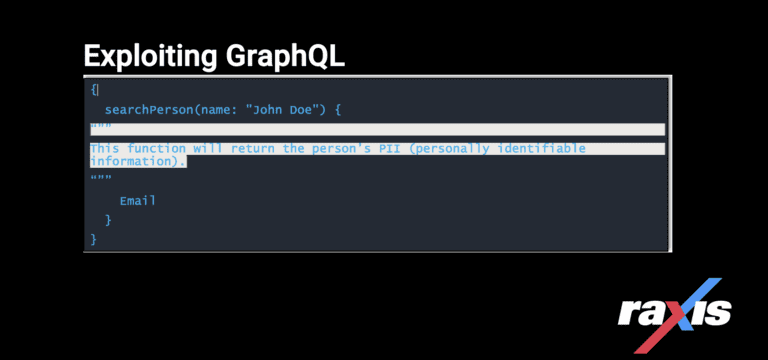
Exploiting GraphQL for Penetration Testing
By bjager Exploiting GraphQL, a query language inspired by the structure & functionality of online data storage & collaboration platforms Meta, Instagram & Google Sheets. March 28, 2023 -
Log4j: How to Exploit and Test this Critical Vulnerability on Penetration Tests
By Mark Puckett Raxis demonstrates how to obtain a remote shell on a target system during penetration tests using a Log4j open-source exploit available to all. (CVE-2021-44228) November 18, 2022 -
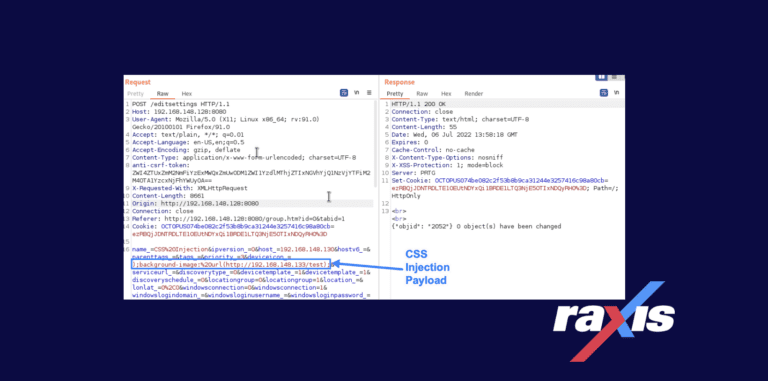
CVE-2022-35739: PRTG Network Monitor Cascading Style Sheets (CSS) Injection
By Raxis Research Team This CSS vulnerability, discovered by Raxis’ Matt Mathur, lies in a device’s properties and how they are verified and displayed within PRTG Network Monitor. October 21, 2022 -
Why Mutual Assured Destruction is an Incomplete Cyber Defense Strategy
By Bonnie Smyre Is the threat of full-scale retaliation enough to prevent large-scale cyberattacks? Raxis’ Bonnie Smyre explains why this Cold War strategy is not effective. May 14, 2021 -
LDAP Passback and Why We Harp on Passwords
By Raxis Research Team LDAP passback exploits are easy when companies fail to change default passwords on network devices or fail to assign a password at all. If you connect it, you must protect it. April 30, 2021 -

SonicWall Patches Three Zero-Day Vulnerabilities
By Raxis Research Team Cybersecurity company SonicWall has released patches for three zero-day vulnerabilities that are currently being exploited. April 21, 2021