Written by Brian Tant
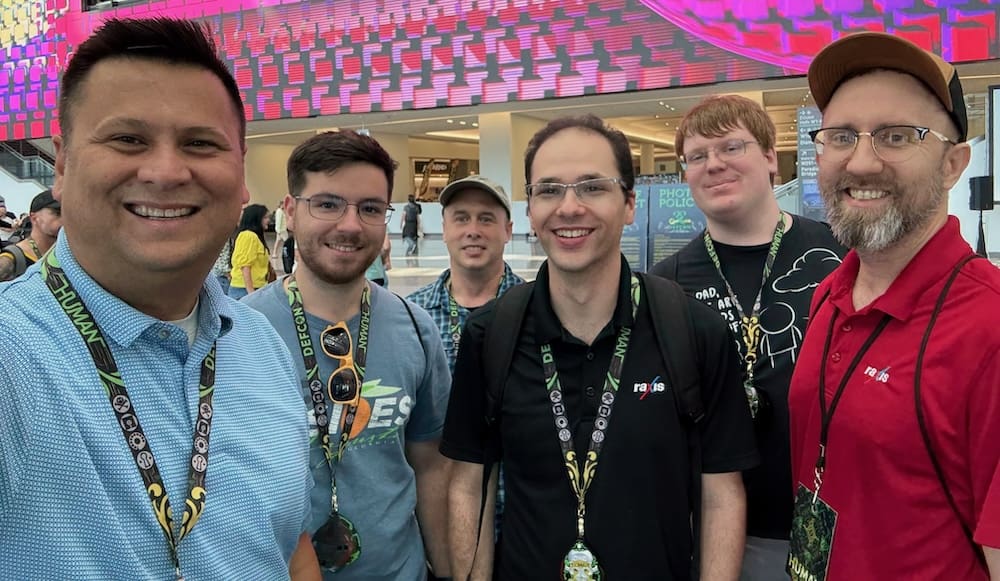
The Raxis team met up at DefCon 33 this past weekend. Always on the cutting edge of ethical & not-so-ethical hacking (what happens in Vegas, stays in Vegas, I suppose), it’s a great way to keep a finger on the pulse of offensive cybersecurity. To protect our customers and keep up to date on the latest pentest and social engineering exploits, we want to know what the bad guys are up to.
A few of the interesting talks, villages, and ideas this year:
- Maritime Hacking
- Active Directory to Entra ID
- Overlooked Attack Surfaces in Apple Devices
- New Surveillance Camera Attacks
- EV Charging Exploits
- Hacking in the Age of AI
- Abusing Google Services
- Remote Code Execution and Arbitrary SMS Attacks on 5G & 4G/LTE Routers
- Mainframe Hacking with SSH
- Counterfeiting Event Badges and Credentials
- Lack of Automotive Privacy
- API Flaws & Control of Cars
- IoT Security Failures
- Exposing Private Data from AI Models
- New DDOS Attacks
Now here are some personal remarks on the experience: For those that have attended DefCon before, most of the list above should look familiar. Between the villages, talks, and workshops, there was something to satisfy any hack-minded seeker. Several talks were concerned with the ever-growing attack surfaces of embedded systems, and of course, the general apathy displayed by society toward them. The RF and Ham Village were good fellowship with other radio nerds. We saw that AI is no longer creeping around the hallways either; it’s front and center asking, “how do you do”? I also attended a fascinating talk on the subject of AI’s role in pentesting. (Spoiler: we’re still not entirely sure how, but it will really be disruptive in the very near future. AI even says so.)
DefCon 33 also indulged us in some of the more practical hacker machination techniques, an area close to my heart. The most memorable was a frightening talk by a surprisingly calm gentleman demonstrating how anyone with a Git account and an SDR can bring about the downfall of critical infrastructure. Okay, that may be an embellishment, but it’s not a big one.
The Policy breakouts were also super engaging with several privacy and digital advocacy headliners sharing news good and also some less so. The take home from this DefCon for me, as it has been in the past, is that we live in a very fragile world, and we depend heavily on fundamentally undependable things. We’re fortunate to have a place recognizing people who are willing to put in the long hours calling out risk. As a grumpy old man looking forward to next year, it also filled me with mischievous joy and hope to see the younger faces walking the halls. The future seems dark indeed, but that’s a good thing. A lot of heroes wear black, after all.

Brian Tant
Search The Exploit Blog
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless