Written by Andrew Trexler
The other day I was on a web application penetration test. During testing I was going through the login functionality to check for common issues like account enumeration and vulnerability to a brute-force attack.
Normally when doing these checks I capture the request with Burp Suite and then send it to the Repeater tab. From there I make changes and send the request over and over again. On this particular engagement, I kept running into an issue where the request would expire after a short amount of time.
After some investigation I narrowed it down to a particular cookie. With the help of AI, I was able to identify the function that generated the cookie then reimplement it in python so I could create my own brute-force script.
In this blog I’ll go through this process with a lab site to show just how this can be done and what web developers will want to watch for to protect their sites.
Setting Up the Sample Site with a Cookie
First, we need a web server that takes a request. For testing and demonstration, I’m just going to have the app check the cookie and respond when we click a button:
- If the cookie is old, it will say expired
- If the cookie is still valid, it will say success
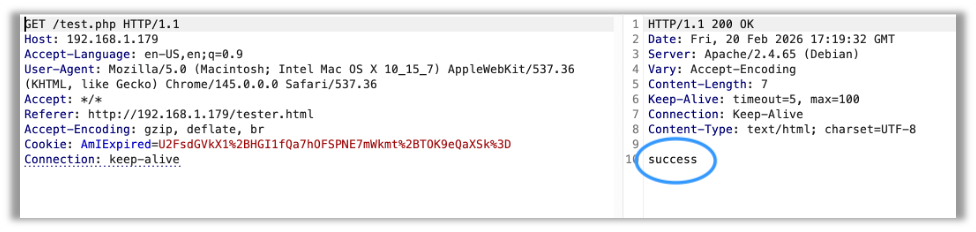
If you’re anything like me, you already have access to a web server with PHP for testing. If not, you can follow along in this blog. Once the test site is setup, we click the button which sends a request, intercept that request, and send it to Burp Suite’s Repeater tab. We can replay the request and get the expected success message.
Now we have a little bit of time before it expires for our test, but eventually it will expire like shown.
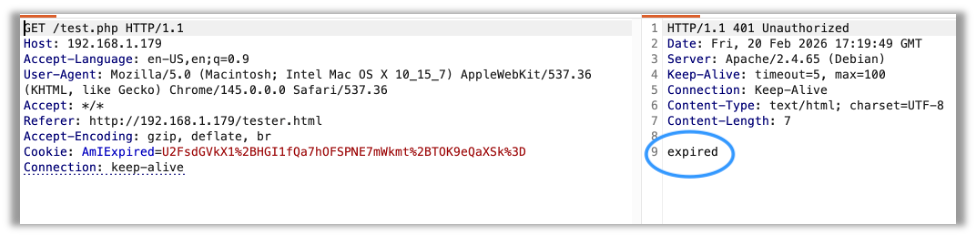
This matches the functionality I saw on my pentest closely enough for a demonstration.
Using AI to Write a Script
Now, in our case, the HTML file isn’t that complex, so you could simply right click, view source, and understand what’s happening. But on many modern apps this isn’t the case as there are thousands of lines of code. Not to mention many times they get minified, so the function and variable names aren’t helpful as they are single letters.
So, what’s a good way to find the functionality we need?
Breakpoints.
Now this was the first point where AI made my life easier. It gave me a block of code I could enter into the console that would look for where the cookie I needed got its value set and then call the debugger so I could take a look more closely.
// Intercept cookie setting
const orig = Object.getOwnPropertyDescriptor(Document.prototype, 'cookie');
Object.defineProperty(document, 'cookie', {
set(val) { if (val.startsWith('AmIExpired')) debugger; orig.set.call(this, val); }
});After running the command (make sure to change your cookie name if it’s different), you can trigger the request. In our example, we click the button. Now the code throws us into the debugger, paused on our code.
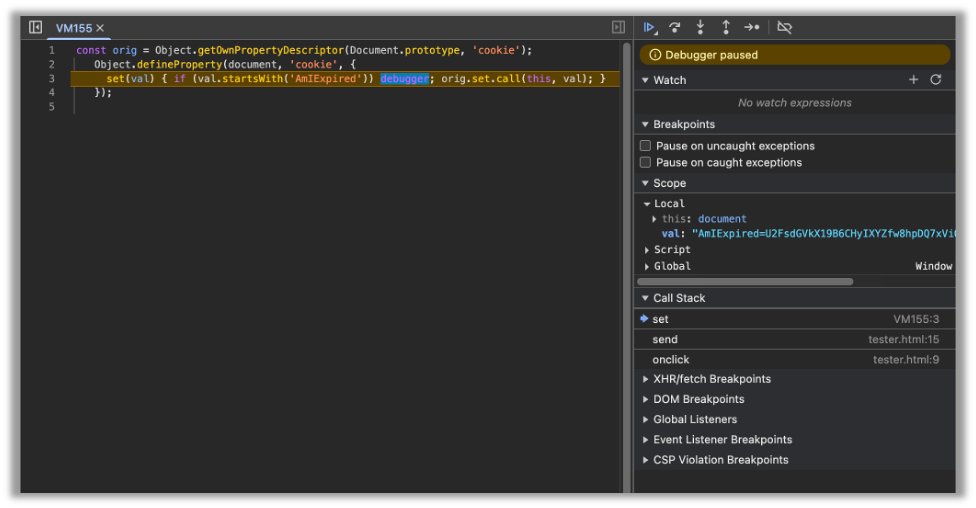
Let’s pay particular attention to the call stack:
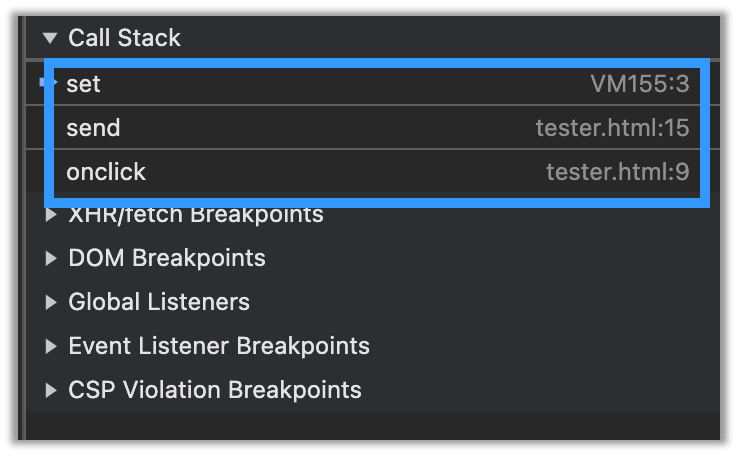
We only have three functions in the call stack, but in real modern apps, this could be a lot more. So now we go through them and search for the code that creates the cookie. Let’s check the send function:
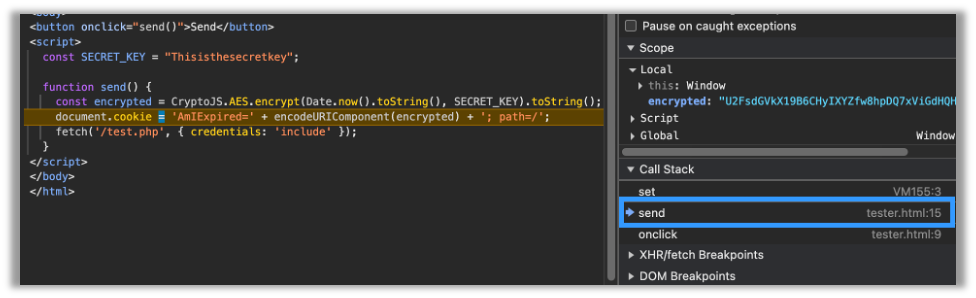
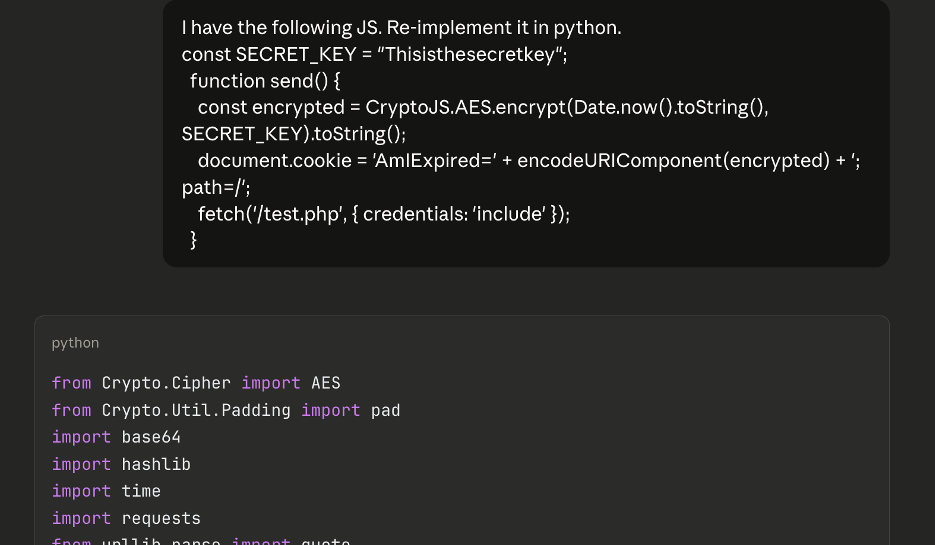
Hey, that looks like the code that’s generating the cookie. Now here’s where the AI saved me a ton of time. I took the code, gave it to the AI, and asked it to reimplement it in python.
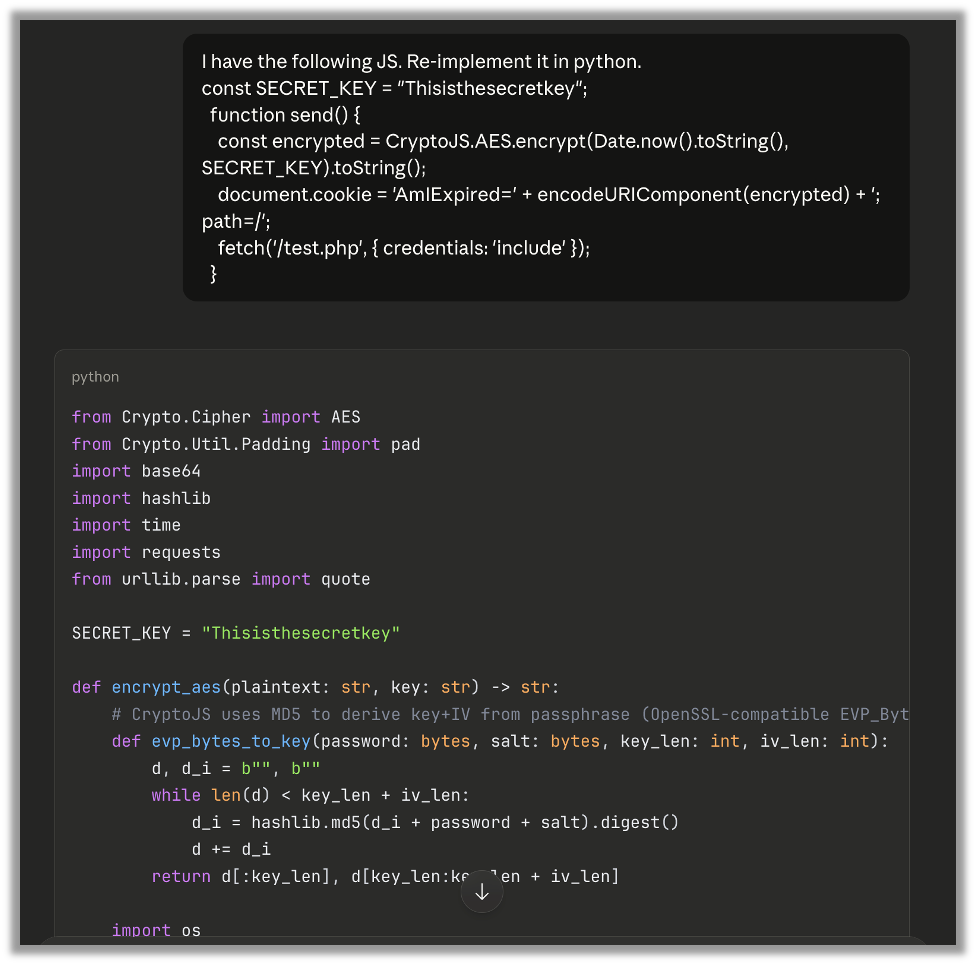
Wow that was easy and also much faster than doing it manually myself.
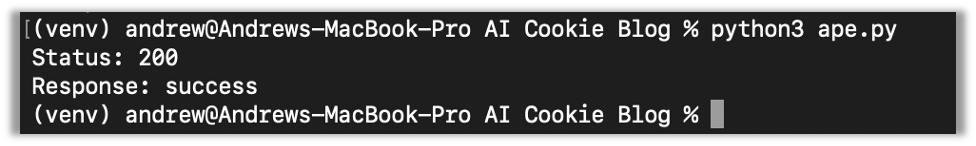
Now after changing the target in the script, I ran it and got a 200 Success, so we know it works.
Some Pointers
I almost always work in a venv with python. After creating it, I had to install requests and pycryptodome with pip.
At this point I could add additional functionality to handle whatever else I need it to do, but I’ll leave that for an actual penetration test. As a side note the pages and scripts used in recreating this exploit for this blog were also generated by AI with my guidance so that I could show the details clearly.
What the Devs Need to Know
Anything client side can be replicated, so you can’t rely on client-side code for controls like rate limiting. It may stop a low level person but not someone dedicated to hacking the site. When coding anything for controls, it needs to be coded on the server-side.
Final Thoughts
Pentests are time-boxed, meaning sales teams work with customers to figure out how long they should take to test as much as possible and discover the most important vulnerabilities (and to stay on budget).
Using AI like we did here saves pentesters time when exploiting important vulnerabilities. In the past, we may not have had time to complete a full exploit to show our customers how important the finding was, or we may have spent that time and limited our time testing other areas.
This is what makes AI so useful. Now we get the best of both worlds, and our customers get even deeper penetration testing results so that they can remediate findings that would leave their organization vulnerable.

Andrew Trexler
Search The Exploit Blog
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless