The Exploit articles categorized as Exploits
-

Windows 10 Vulnerability Highlights Need for Physical Security Testing
By Raxis Research Team A Windows 10 security problem offers an excellent example of what can happen when a bad guy gets to spend a few minutes alone with your computer. May 28, 2020 -
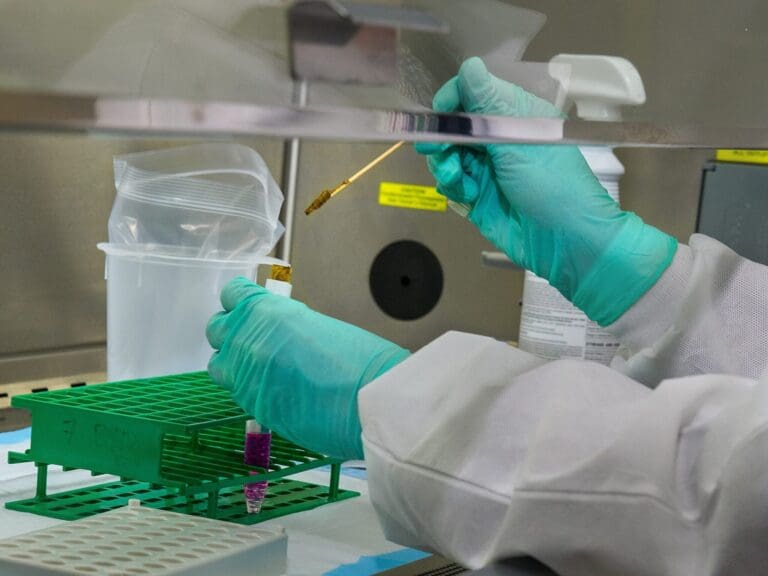
Pharma Breaches and the Terrifying Prospect of Data Manipulation
By Brian Tant Raxis CTO Brian Tant shares his thoughts on cybersecurity threats to the pharma industry and what pharma companies can do to protect themselves. May 14, 2020 -
IKE VPNs Supporting Aggressive Mode
By Bonnie Smyre In this post we’ll look at why IKE VPNs with Aggressive Mode enabled continue to be a vulnerability, how it can be exploited, and how to mitigate this risk. May 23, 2018 -

Web Attacks: Insecure Transmission of Data
By Bonnie Smyre Raxis COO Bonnie Smyre discusses the vulnerabilities that arise when web apps transmit data insecurely and what you can do to secure your apps. April 26, 2018 -

Web Attacks: Clickjacking
By Bonnie Smyre Many of the external network and web application penetration tests that we perform list ‘clickjacking’ as a vulnerability. Here Raxis COO Bonnie Smyre explains what clickjacking is and how you can protect against it. April 19, 2018 -

Aerial Drones – A New Frontier for Hackers
By Brad Herring Raxis VP of Business Development discusses how aerial drones, which are now prevalent, can be used in attacks on your security and what you can do to protect your company. January 2, 2017