The Exploit articles categorized as Password Cracking
-
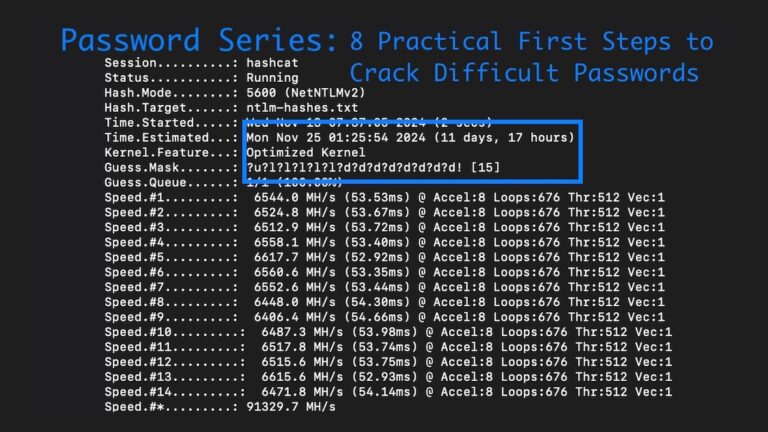
Password Series: 8 Practical First Steps to Crack Difficult Passwords in Penetration Tests
By Ryan Chaplin From rulesets & hardware to wordlists and mask attacks, Lead Penetration Tester Ryan Chaplin shows how to crack difficult password hashes in penetration tests. February 25, 2025 -

Password Series: Defeating Emerging Password Security Trends with Psudohash for Penetration Testing
By Ryan Chaplin Lead Pentester Ryan Chaplin discusses emerging improvements in password security and how Psudohash can help bypass them on penetration tests. November 5, 2024 -

Password Length: More than Just a Question of Compliance
By Brian Tant Password length requirements are a key part of password security, but, with PCI, NIST, OWASP, and CIS offering different recommendations, what length is best? June 4, 2024 -
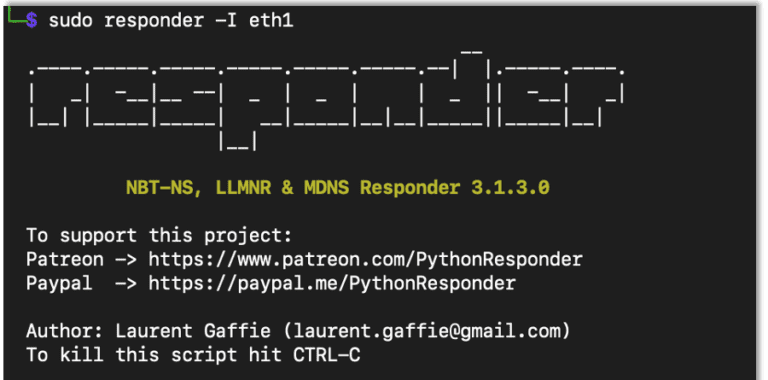
AD Series: How to Perform Broadcast Attacks Using NTLMRelayx, MiTM6 and Responder for Penetration Tests
By Andrew Trexler Andrew Trexler continues his AD Series with an in-depth tutorial on broadcast Attacks using NTLMRelayx, MiTM6 and Responder for penetration tests. June 19, 2023 -

How to Create an AD Test Environment to Use for Penetration Testing
By Andrew Trexler Andrew Trexler walks us through creating a simple AD test environment to test new hacks before trying them on a penetration test. April 27, 2023 -

Understanding the Why Behind Password Management
By Bonnie Smyre In this video, Raxis CTO Brian Tant explains why password mismanagement is still one of the most reliable ways to breach a company network and what you can do to secure your network. July 10, 2020