The Exploit articles categorized as How To
-
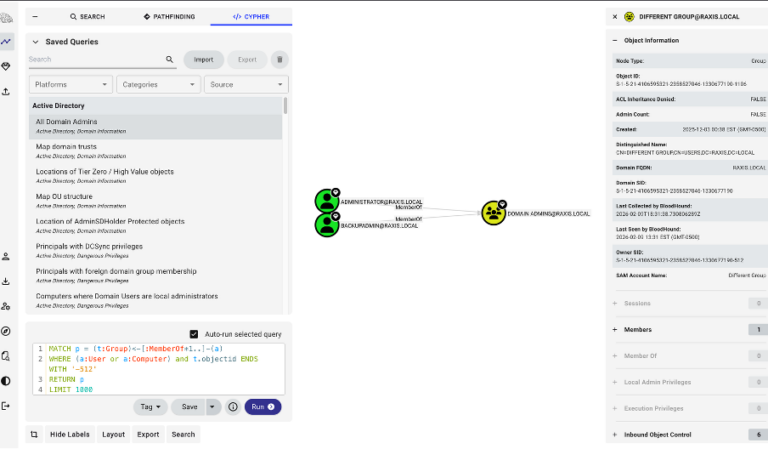
Cool Tools: Bloodhound CE
By Andrew Trexler BloodHound’s Community Edition has everything a penetration tester needs to enumerate relationships in a domain in order to gain more access, even Domain Admin. June 2, 2026 -

Defense in Depth Against Linux Kernel Privilege Escalation: A Practical Guide for Container Workloads
By Ryan Chaplin With current local privilege escalation exploits like Copy Fail and Dirty Frag active in the wild, harden your defenses to halt attacks even before patching. May 26, 2026 -
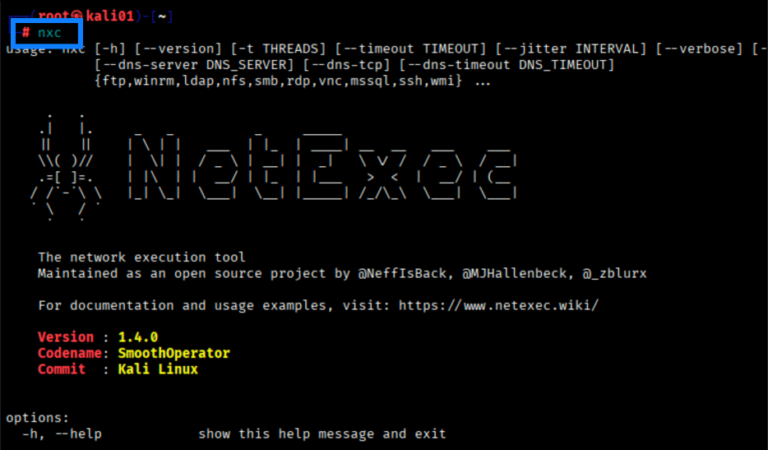
Cool Tools: NetExec (NXC) Fundamentals
By Scottie Cole Now that CrackMapExec is no more, how is a pentester to rapidly test credentials, enumerate assets, spray passwords, and more? Learn the basics of NetExec here. May 19, 2026 -

Bypassing ChatGPT’s Open-Source Model Security Restrictions for Agentic Hacking
By Ryan Chaplin Ryan Chaplin wondered what it would take to bypass ChatGPT’s open-source model security restrictions to allow AI to hack his website. See how he did it here. May 5, 2026 -
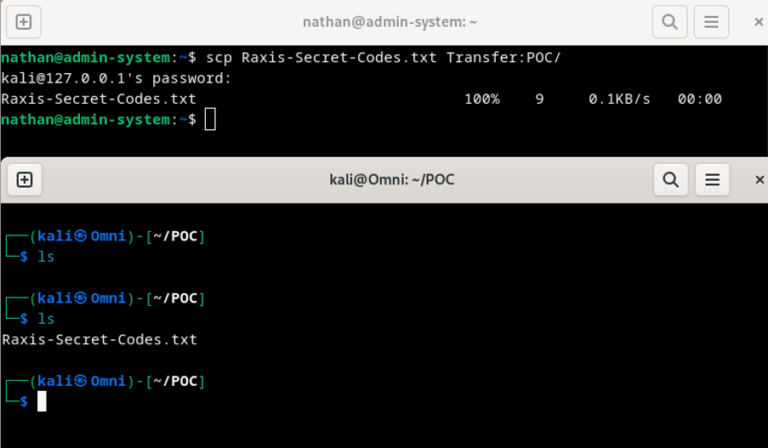
Cool Tools Series: SCP
By Nathan Anderson Raxis Lead Penetration Tester Nathan Anderson continues our Cool Tool Series with SCP for data exfiltration on internal network pentests and red teams. April 21, 2026 -
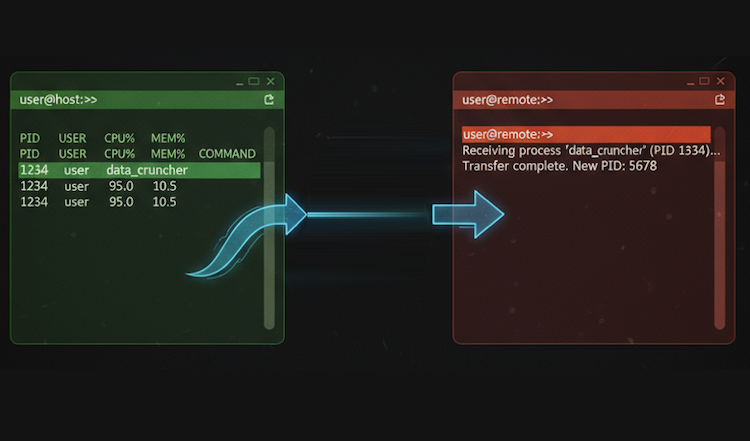
Cool Tools Series: Reptyr
By Jason Taylor Jason Taylor brings highlights reptyr in our Cool Tools series, showing how to take a long-running process, like an Nmap scan, and move it to a new screen. April 7, 2026