Articles Categorized as Penetration Testing
-
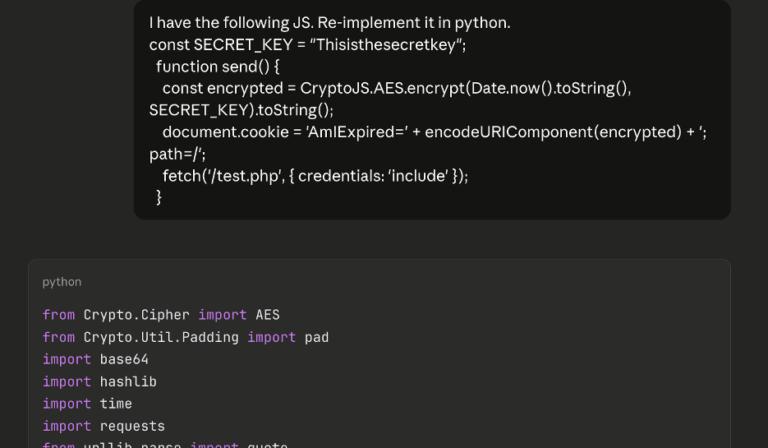
AI-Augmented Series: AI Scripting for Brute-Forcing on a Web App Pentest
By Andrew Trexler On a recent web app pentest, Andrew Trexler used AI to find client-side code that stopped his brute-force attack then used AI again to thwart that code. March 4, 2026 -
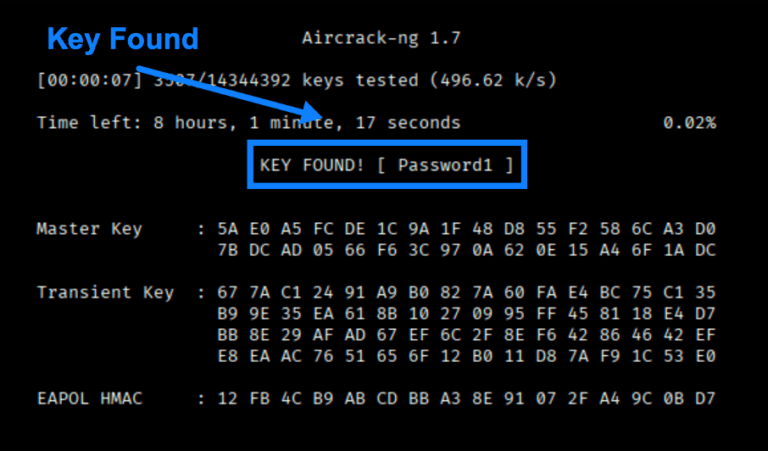
Wireless Series: The Aircrack-ng Suite for All Your Wireless Pentesting Needs
By Scottie Cole Principal Penetration Tester Scottie Cole continues our wireless series with the Aircrack-ng Suite, a set of tools for wireless pentest discovery and exploits. February 24, 2026 -

Data Theft Exploit Part 2: DNS Exfiltration Attack
By Jason Taylor Raxis’ Jason Taylor is back with a detailed tutorial on performing both manual and automated DNS exfiltration attacks for pentesting. January 13, 2026 -

Why 8-Character Passwords Are No Longer Enough: Lessons from the Raxis Password Cracker
By Brad Herring With the start of 2026, the Raxis team is already busy. A new upgrade to our password-cracking system shows how quickly 8-character passwords can be cracked. January 9, 2026 -

The Future of Security: Why AI-Augmented Penetration Testing Is the Way Forward
By Mark Puckett Raxis CEO Mark Puckett looks back at a year of many changes and forward to the ways AI-augmented pentesting is changing the industry. December 30, 2025 -

Data Theft Exploit Part 1: DNS Exfiltration Setup
By Jason Taylor Raxis Lead Penetration Tester Jason Taylor’s in-depth tutorial explains setting up a server for DNS exfiltration. Check back next month to run the attack. December 16, 2025