I’m Matt Dunn, lead penetration tester at Raxis, and I’ve uncovered a couple more ManageEngine vulnerabilities you should know about if your company is using the platform.
Summary
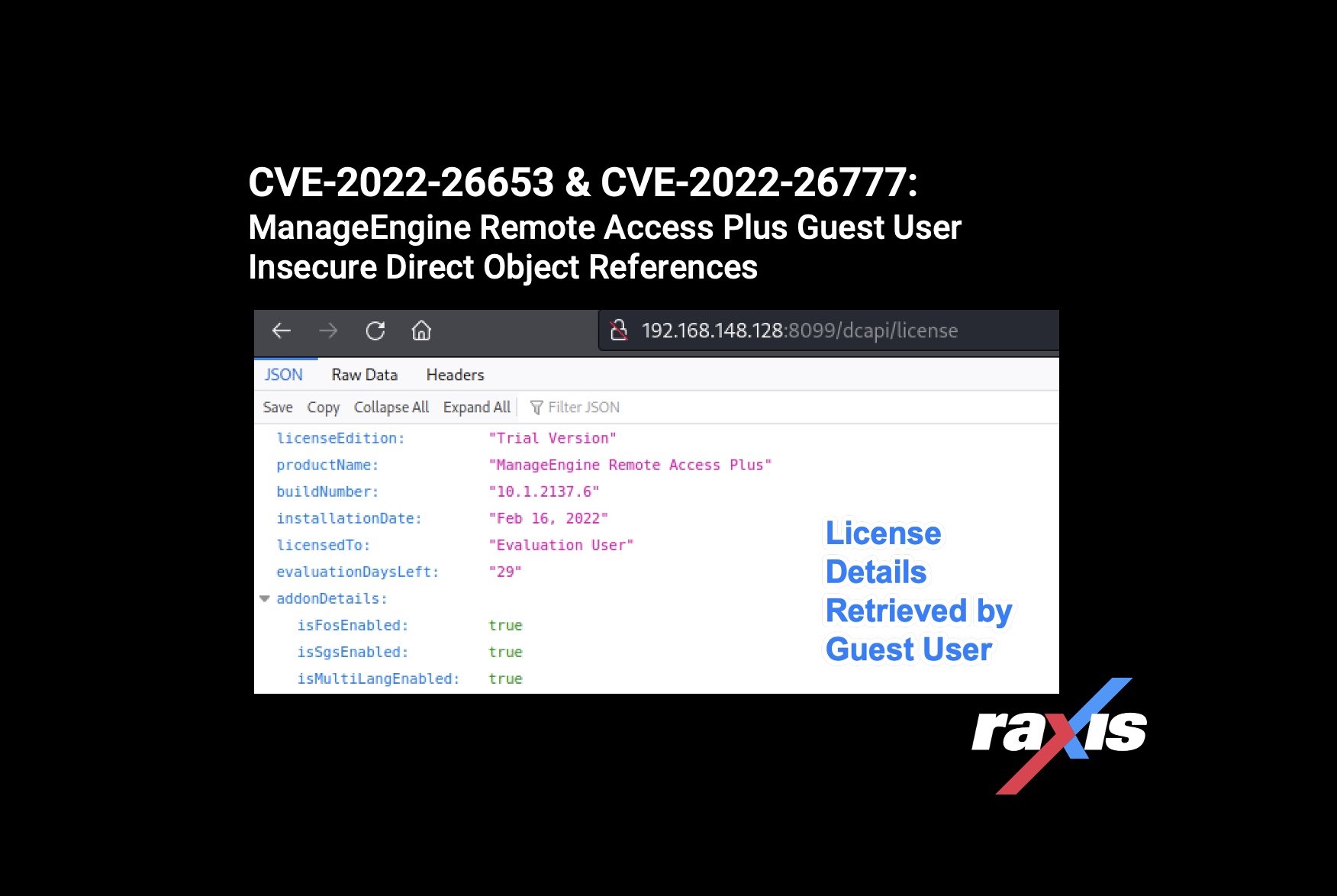
I discovered two instances in ManageEngine Remote Access Plus where a user with Guest permissions can access administrative details of the installation. In each case, an authenticated ‘Guest’ user can make a direct request to the /dcapi/ API endpoint to retrieve information. This allows the ‘Guest’ user to discover information about the connected Domains as well as the License information for the installation.
Proof of Concept
The two vulnerabilities are similar in that they allow a user with ‘Guest’ level permissions to access details about the installation. Each CVE refers to a specific piece of information that the user can retrieve, as detailed below:
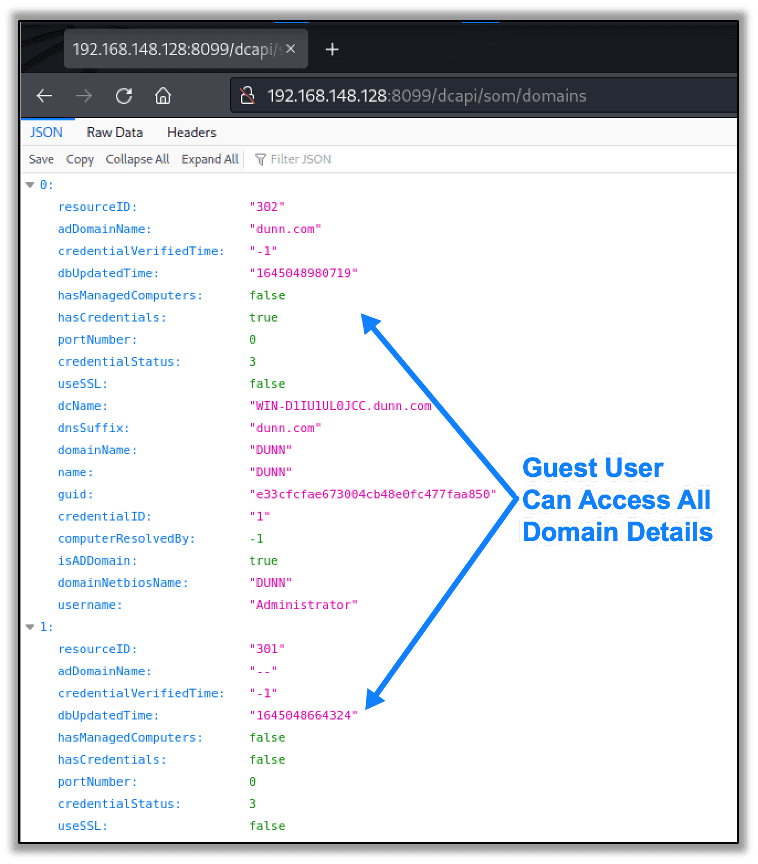
CVE-2022-26653 – The ‘Guest’ user can retrieve details of connected Domains.
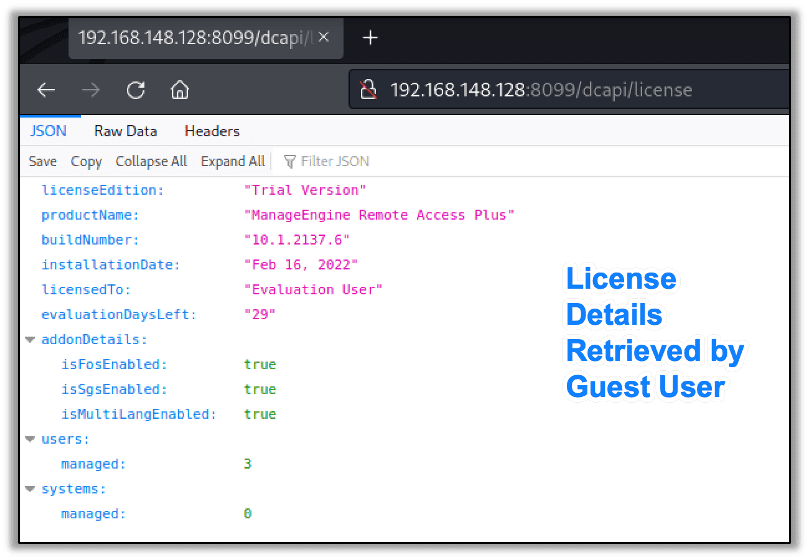
CVE-2022-26777 – The ‘Guest’ user can retrieve details about the installation’s License.
The user with ‘Guest’ permissions can access all the Domain’s details, including the connected Domain Controller, the account used for authentication, and when it was last updated, as shown here:
Similarly, the ‘Guest’ user can access all the License information, including the amount of users, amount of managed systems, who the license is for, and the exact build number, as shown below:
Affected Versions
Raxis discovered these vulnerabilities on ManageEngine Remote Access Plus version 10.1.2137.6.
Remediation
Upgrade ManageEngine Remote Access Plus to Version 10 Build 10.1.2137.15 or later which can be found here:
- Download Link – https://www.manageengine.com/remote-desktop-management/service-packs.html
- Release Notes – https://www.manageengine.com/remote-desktop-management/hotfix-readme.html
Disclosure Timeline
- February 16, 2022 – Vulnerabilities reported to Zoho
- February 17, 2022 – Zoho begins investigation into reports
- March 8, 2022 – CVE-2022-26653 is assigned to the Domain Details vulnerability
- March 9, 2022 – CVE-2022-26777 is assigned to the License Details vulnerability
- April 8, 2022 – Zoho releases fixed version 11 Build 10.1.2137.15 that addresses both vulnerabilities
CVE Links
CVE-2022-26653
- Mitre CVE – https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-26653
- NVD – https://nvd.nist.gov/vuln/detail/CVE-2022-26653
CVE-2022-26777
- Mitre CVE – https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-26777
- NVD – https://nvd.nist.gov/vuln/detail/CVE-2022-26777

Raxis Research Team
About The Exploit Blog
The Exploit is written by Raxis penetration testers. Every post is a technical writeup from someone who runs engagements for a living, with code, command output, and the reasoning behind each step. Topics include exploit research, vulnerability disclosure, tool development, and the offensive techniques showing up in current client work.
Search The Exploit Blog
Raxis Discovered Vulnerabilities
View the CVEs and bugs that Raxis pentesters have uncovered and submitted.
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis Discovered Vulnerabilities
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless