Written by Nathan Anderson
A recently surfaced tool, known as SpamGPT, is circulating in underground forums. In today’s blog I’ll give an overview of what the tool can do and what to watch for to protect your company from these easily automated large-scale scams.
What is SpamGPT?
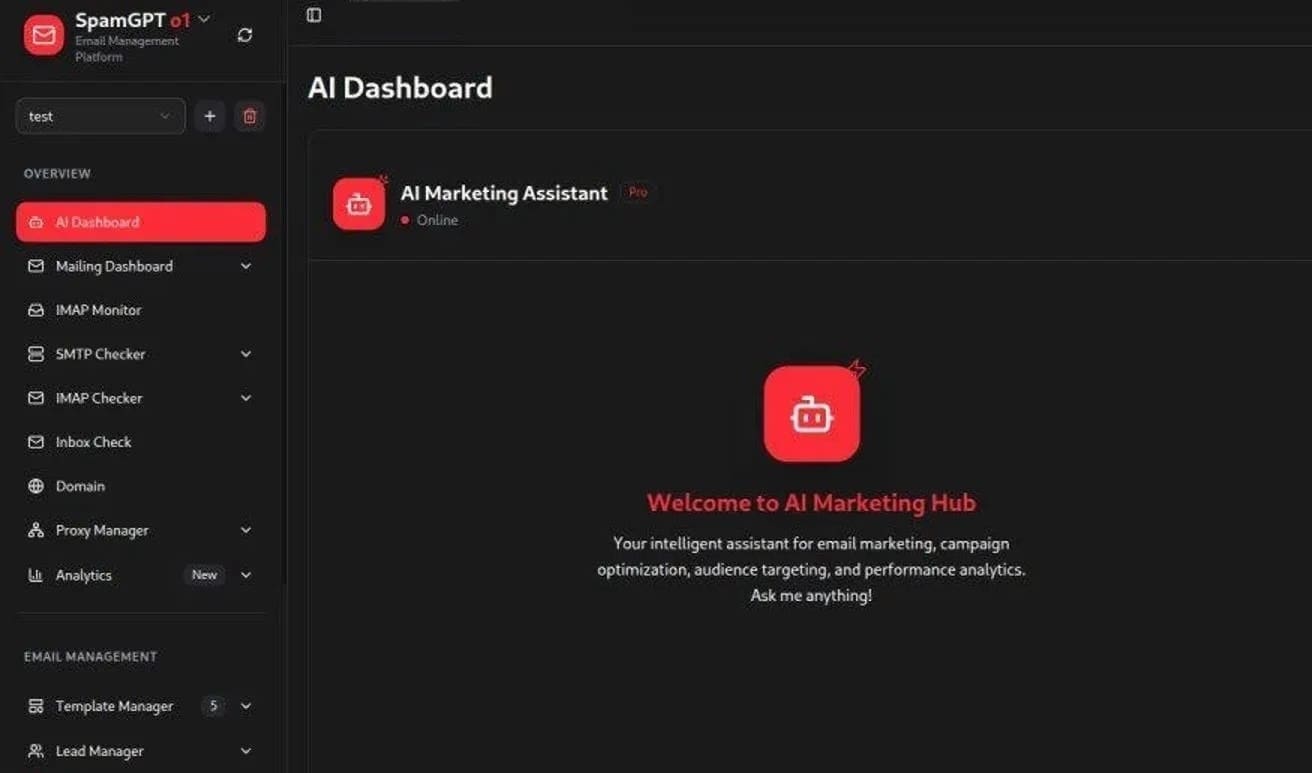
Functioning like a business‑grade CRM powered by generative AI to automate and scale scams, SpamGPT bundles contact management, campaign scheduling, customizable message templates, and AI‑generated copy for emails, SMS, and social‑media lures. This allows the attackers using it to run targeted, high‑volume phishing and fraud campaigns with minimal technical skills.
The platform can personalize messages at scale, track campaign performance, and iterate content quickly, effectively turning criminal operations into “marketing” workflows.
What Can Your Company Do?
To defend against these automated scams, there are several things companies can do:
- Strengthen email authentication with monitoring and flagging on detection of AI‑generated messaging patterns across email, SMS, and other platforms.
- Enforce multi‑factor authentication (MFA).
- Tighten email and SMS filtering.
- Strengthen email authentication through DMARC, DKIM, and SPF.
- Run regular phishing simulations and user training so recipients can spot suspicious content.
In Conclusion
Attacks like these are not new, the difference here is how easy it is for an attacker with no technical prowess to send and manage complex sets of messages. This allows the attacks to become much more frequent, to build trust, and to sometimes hit the mark.
Over the years, as I’ve performed phishing and other social engineering engagements for our customers, I’ve found that the individuals who take a moment to stop and think before taking any action often save the day. If a phish like this makes it past all the technical controls and gets to your inbox or your phone, notifying your IT department so that they can warn others and block the attack is often the difference between a compromise and a non-event. Let’s all stay vigilant!

Nathan Anderson
Search The Exploit Blog
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless