So, I Hacked a Tesla . . .
Tesla deserves great credit for bringing electric vehicles into the mainstream. Say what you will about Elon Musk, his vision is proving wildly successful in a space where many others have failed.
Even so, if the two of us could have a conversation, I’d probably recommend that the company invest more time and resources in cybersecurity for its vehicles.
Here’s why:
Recently I decided to see how easy it would be for my personal Tesla to be hacked — and stolen. As you will see in the video below, with some commonly used tactics, it was relatively quick and easy.
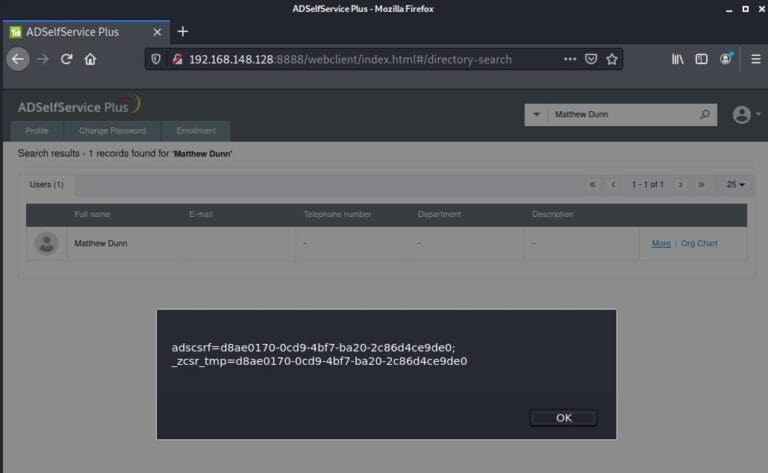
The attack demonstrated in the video relies on phishing to get the victim’s credentials. At that point, the hacker has complete control and can do pretty much whatever they wish — including unlocking the car and driving away.
The video demonstrates why, if you’re not careful, your Tesla could be compromised and stolen without a lot of effort from the attacker.
Until the company itself adds more protection, it’s up to you to take some basic precautions. By the way, it’s wise to follow these practices no matter if it’s your Tesla, your bank account, your Twitter feed, or any online account.
- Stay vigilant and question any WiFi network that asks you to connect.
- Never give account information, credentials, or access tokens to a third party unless it is absolutely necessary.
- Every account you create should have a unique and strong password. Every. Single. Account.
- If your account is compromised, immediately reset your password and let the company or companies know.
Here at Raxis, we offer a broad range of services to help find security vulnerabilities within your organization. And though a typical penetration test would not uncover this type of vulnerability, a Raxis red team assessment could.
Our red team assessments tests your organization’s security from top to bottom and end to end to uncover any way your network can be compromised by a skilled and determined attacker. If you are ready to take control of your company’s security, contact us and let us see how we can help.

![Voice Phishing - Social Engineering[Part 2]](https://raxis.com/wp-content/uploads/2023/05/img-12-1-768x403.webp)