The Exploit articles categorized as How To
-

Five Things to Always Do After Getting Domain Admin
By Andrew Trexler So you got DA on your red team or internal network penetration test. Here are the five things that Principal Penetration Tester Andrew Trexler does next. March 24, 2026 -
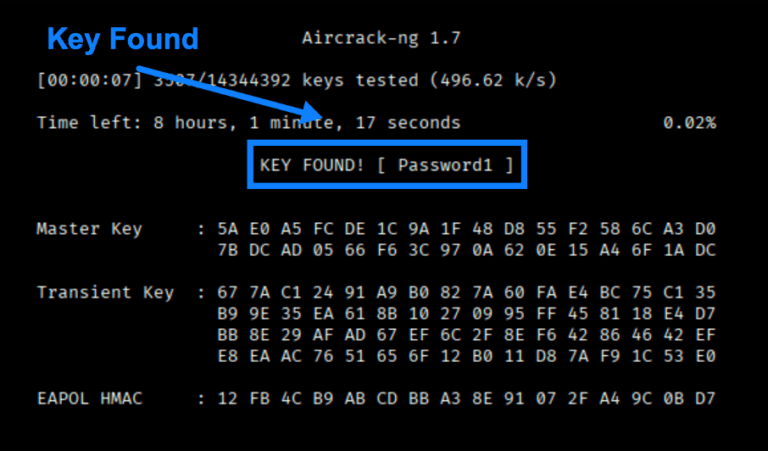
Wireless Series: The Aircrack-ng Suite for All Your Wireless Pentesting Needs
By Scottie Cole Principal Penetration Tester Scottie Cole continues our wireless series with the Aircrack-ng Suite, a set of tools for wireless pentest discovery and exploits. February 24, 2026 -
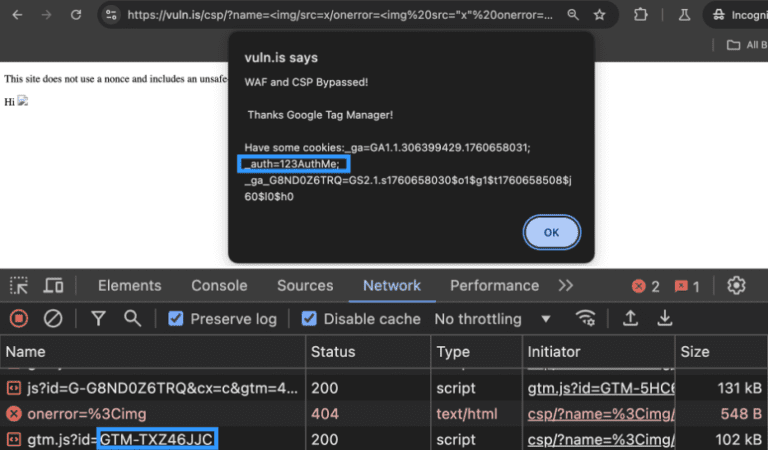
Bypassing a WAF and a CSP with Google Tag Manager: An Attacker’s Perspective and Remediation Advice
By Ryan Chaplin Ryan Chaplin takes an in-depth look at how attackers can use unsafe directives to bypass CSP, notably in Google Tag Manager, and how to remediate the issue. February 10, 2026 -

PSE & Red Team Series: Social Engineering
By Nathan Anderson Lead Penetration Tester Nathan Anderson is back with more PSE and red team tips, including tailgating, impersonating, and pretexts to gain onsite access. January 27, 2026 -

Data Theft Exploit Part 2: DNS Exfiltration Attack
By Jason Taylor Raxis’ Jason Taylor is back with a detailed tutorial on performing both manual and automated DNS exfiltration attacks for pentesting. January 13, 2026 -

Cross-Site Scripting (XSS): Cookie Theft – Advanced Payloads
By Raxis Research Team We reached into our vaults to bring you the final video in our cross-site scripting (XSS) series. Learn about cookie theft, website defacement, and CSRF attacks. December 18, 2025