Written by Adam Fernandez
In Scottie’s recent Cool Tools blog about discovery tools, he, like many network penetration testers, starts with Nmap. Nmap is a great discovery tool with many flags and scripts. In this post, I will expand upon Scottie’s ideas and delve more deeply into what Nmap has to offer, specifically for network penetration testing.
Hosts Marked as Down When They Are Up
If you find you have problems with Nmap flagging hosts as down, even though they should be up, I would recommend adding these flags to your command:
- -PS – SYN ping scan. You can optionally add a port number after this.
- –PA – ACK ping scan. You can optionally add a port number after this.
- -PE – Typical ICMP ping echo request, typically blocked by firewalls.
- -PP – ICMP timestamp ping query, which can sometimes get around misconfigured firewalls.
- -PM – ICMP subnet mask ping query, also good for evading misconfigured firewalls.
- -PO -This issues an IP protocol ping, which seems to work a lot of times when other probes don’t.
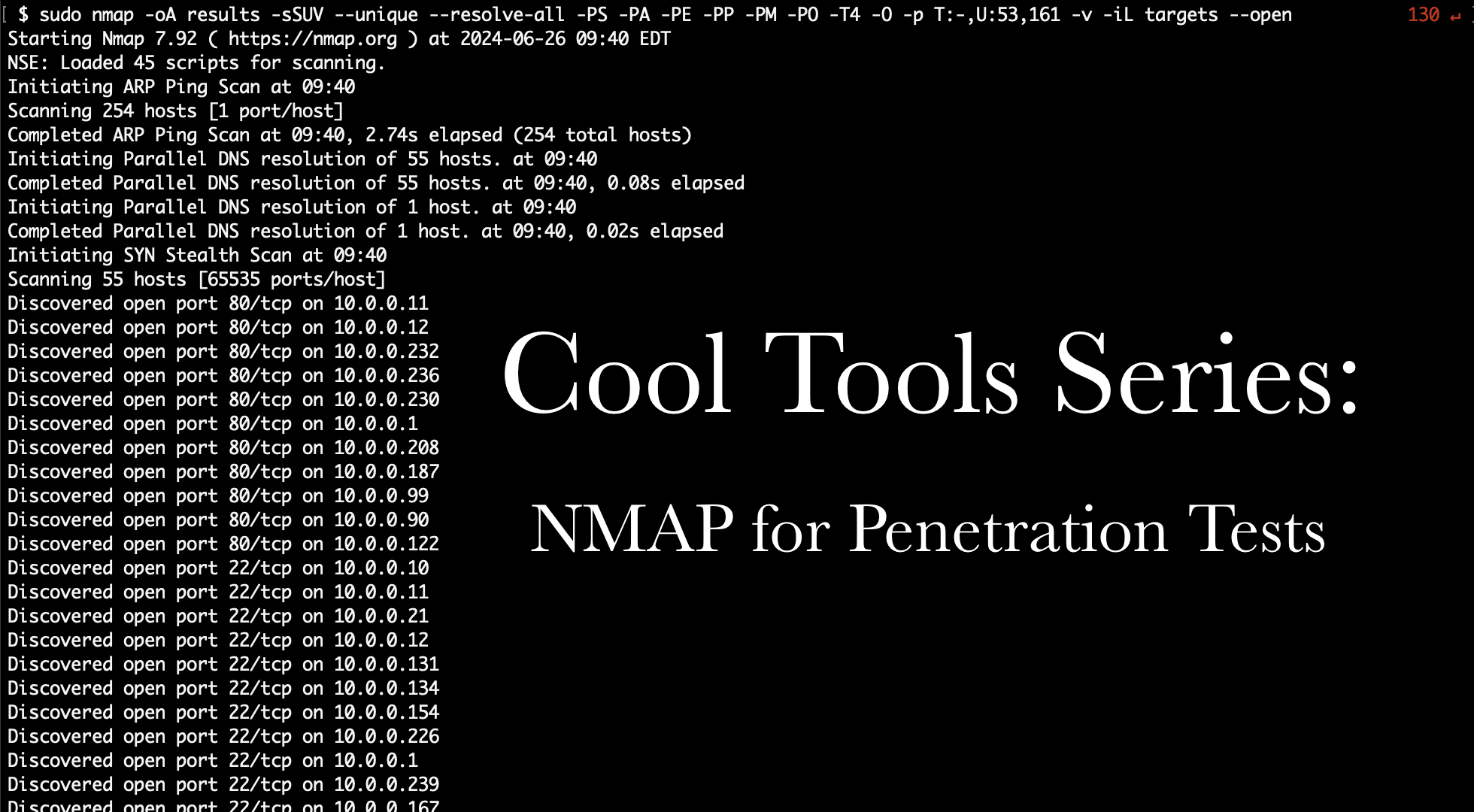
Putting that all together, my typical scans are now starting to look like this:
sudo nmap -oA [output] -sSUV --unique --resolve-all -PS -PA -PE -PP -PM -PO -T4 -O -p T:-,U:53,161 -vv -iL [targets]Some other options present here:
- -oA [output] – Output in all file formats simultaneously.
- -sSUV – Combo of -sS (TCP SYN scan), -sU (UDP scan), and -sV (service version scanning).
- –unique – Scan each IP only once (e.g. if raxis.com resolves to 1.1.1.1, and both are targets, only scan 1.1.1.1 once).
- –resolve-all – If an DNS name resolves to multiple IPs, scan each IP.
- -T4 – Go a bit faster than default, recommended for modern networks (unless you’re trying to be quiet).
- -O – Try to determine operating system.
- -p T:-,U:53,161 – Scan all TCP ports as well as UDP ports 53 (DNS) and 161 (SNMP).
- -vv – Be very verbose in output.
- -iL [targets] – Use the targets in the specified file.
Additionally, when using -oA, if your scan gets interrupted, you can use this to resume the scan where it left off:
nmap --resumeThe Nmap Scripting Engine
The Nmap Scripting Engine (NSE) provides 604 scripts and 139 libraries at the time I’m writing this. That number grows each year, so, needless to say, this is a very useful tool for penetration testers or for blue teams checking out possible vulnerabilities in their systems. I’ll discuss some Useful NSE scripts here, and I encourage you to take a look to see if there are others that would be helpful for your needs.
Shodan
- Queries the Shodan API for the targets. Follow the instructions on the NSE site to setup a Shodan API key.
nmap --script shodan-api [IP Range] -sn -Pn -n --script-args 'shodan-api.outfile=potato.csv,shodan-api.apikey=SHODANAPIKEY'
nmap --script shodan-api --script-args 'shodan-api.target=[IP],shodan-api.apikey=SHODANAPIKEY'Server Message Block (SMB)
- Check if SMB signing is disabled:
nmap --script smb-security-mode -p445 [IP]File Shares
- Attempt to enumerate SMB shares:
nmap --script smb-enum-shares -p445 [IP]- Show NFS Shares (Exports):
nmap -sV --script=nfs-showmount [IP List or Range]- Attempt to get useful information from NFS shares (mimics an -ls command):
nmap -p 111 --script=nfs-ls [IP List or Range]
nmap -sV --script=nfs-ls [IP List or Range]Databases
- Attempts to find configuration and version info for a Microsoft SQL Server instance:
nmap -p 445 --script ms-sql-info [IP]
nmap -p 1433 --script ms-sql-info --script-args mssql.instance-port=1433 [IP]- Looks for MySQL servers with an empty password for root or anonymous:
nmap -sV --script=mysql-empty-password [IP]Domain Name Server (DNS)
- Perform DNS Cache Snooping:
nmap -sU -p 53 --script dns-cache-snoop --script-args 'dns-cache-snoop.mode=timed,dns-cache-snoop.domains={host1,host2,host3}' [IP]- Checks DNS anti-spam and open proxy blacklists to see if an IP has been flagged:
nmap --script dns-blacklist --script-args='dns-blacklist.ip=[IP]'
nmap -sn [IP] --script dns-blacklistVirtual Private Network (VPN)
- Checks if the host is vulnerable to the Cisco ASA SSL VPN Authentication Bypass Vulnerability:
nmap -p 443 --script http-vuln-cve2014-2128 [IP]Network Time Protocol (NTP)
- Shows an NTP server’s monitor data:
sudo nmap -sU -pU:123 -Pn -n --script=ntp-monlist [IP]Remote Access
- Attempts to brute-force a VNC server:
nmap --script vnc-brute -p 5900 [IP]- Discovers the security layer and encryption level that is supported by a RDP service:
nmap -p 3389 --script rdp-enum-encryption <ip>Network Protocols
- Attempts to brute-force a POP3 account:
nmap -sV --script=pop3-brute [IP]- Attempts to brute-force a telnet server:
nmap -p 23 --script telnet-brute --script-args userdb=myusers.lst,passdb=mypwds.lst,telnet-brute.timeout=8s [IP]Java
- Attempts to dump all objects from a remote RMI registry:
nmap --script rmi-dumpregistry -p 1098 [IP]
nmap --script rmi-dumpregistry -sV --version-all -p 443 [IP]Weak Ciphers & Algorithms
- Enumerates all web ciphers that a server accepts:
nmap -sV --script ssl-enum-ciphers -p 443 <host>- Finds the number of algorithms the SSH2 server offers (or lists them with verbosity set):
nmap --script ssh2-enum-algos [IP]Certificates
- Displays the server’s SSL certificate. Set verbosity to add more details:
nmap --script=ssl-cert -p 443 [IP]Http
- Checks if HTTP TRACE is enabled:
nmap --script http-trace -d [IP]And Next
If you enjoyed this Cool Tools post, I hope you’ll take a look at the next post in the series as well.

Adam Fernandez
Search The Exploit Blog
Blog Categories
- AI
- Careers
- Choosing a Penetration Testing Company
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet Our Team
- Mobile Apps
- Networks
- Password Cracking
- Patching
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Web Apps
- What People Are Saying
- Wireless