Cybersecurity Tips
-

Cyber Civil Defense: We Can All Fight the Russians
By Bonnie Smyre If you’re outraged over the invasion of Ukraine, there are some things you can do that will actually help make it harder for the Russian government to expand its hostilities. February 28, 2022 -
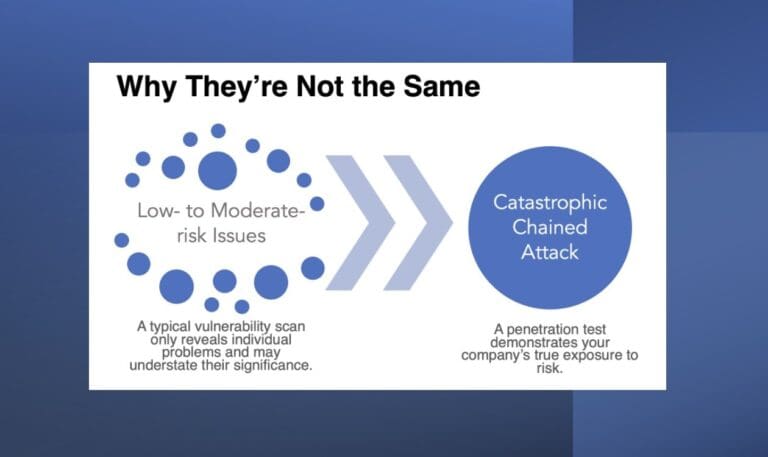
Chained Attacks and How a Scan Can Leave You Vulnerable
By Tim Semchenko Vulnerability scans are useful tools for protecting your network. Find out why you shouldn’t rely on them exclusively. December 10, 2021 -
Keep Your Cookies in the Cookie Jar: HttpOnly and Secure Flags
By Raxis Research Team How can cookies be used against you? And how do you keep that from happening? Raxis’ Matt Dunn explains. September 3, 2021 -

Hurricane Ida: Limiting the Damage
By Scottie Cole Lead penetration tester Scottie Cole is a Gulf Coast resident and former first responder. Read his tips for avoiding hackers and scams that can be as costly as a natural disaster. September 1, 2021 -

Don’t Take the Smishbait
By Bonnie Smyre Unwanted text messages are annoying, but some also hide malicious links. Here are some ways to avoid being “smished.” July 30, 2021 -

12 New Cyber Terms the World Needs Now
By Bonnie Smyre The cybersecurity profession has its own lingo. As experts in the field, the Raxis team felt compelled to add a few we thought were missing. July 23, 2021