Matt Dunn
-
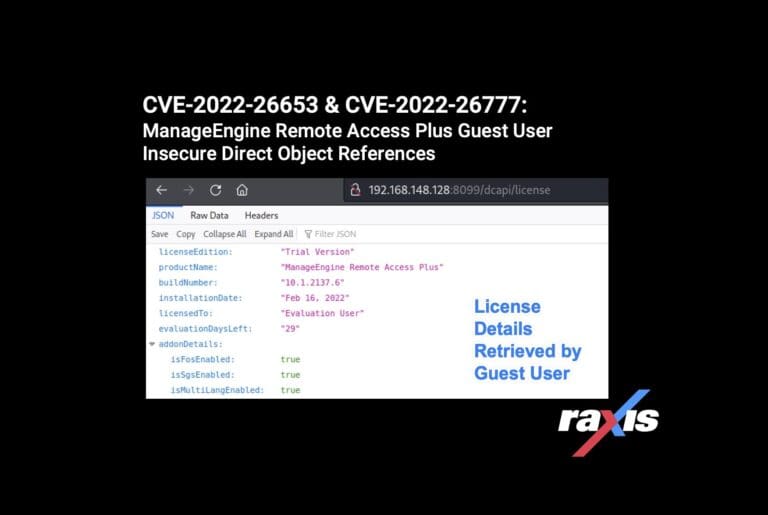
CVE-2022-26653 & CVE-2022-26777: ManageEngine Remote Access Plus Guest User Insecure Direct Object References
By Raxis Research Team Raxis lead penetration tester Matt Dunn uncovers two more ManageEngine vulnerabilities (CVE-2022-26653 & CVE-2022-26777). July 21, 2022 -
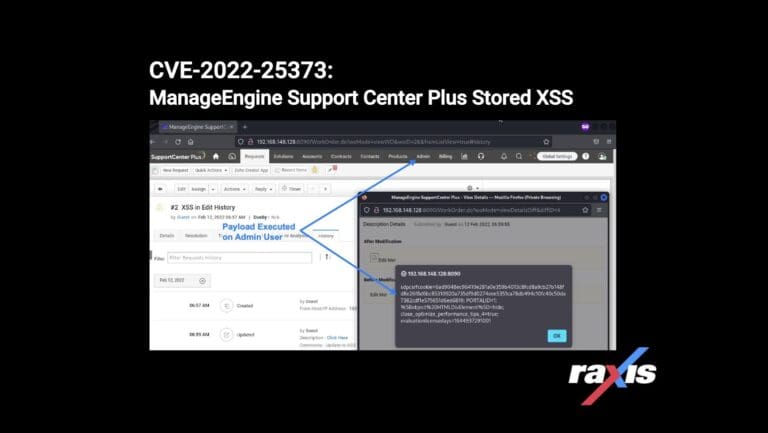
CVE-2022-25373: ManageEngine Support Center Plus Stored Cross-Site Scripting (XSS)
By Raxis Research Team Matt Dunn discovers another ManageEngine Cross-Site Scripting vulnerability, this one in the Support Center Plus application. July 6, 2022 -
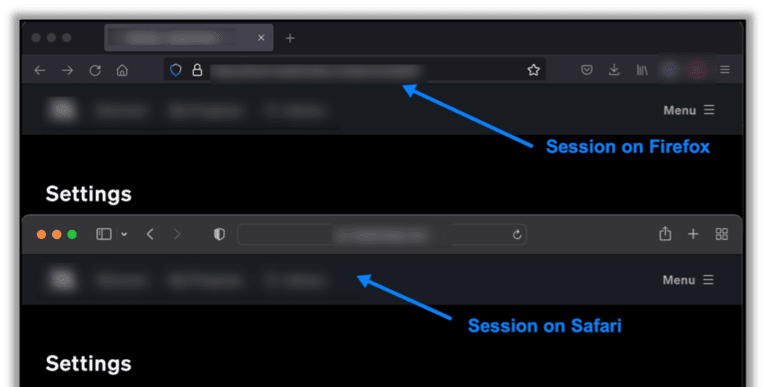
Why We Take Simultaneous Sessions Seriously on Penetration Tests
By Raxis Research Team Raxis Lead Penetration Tester Matt Dunn explains why you simultaneous sessions is a significant finding on a penetration test. April 8, 2022 -

What is Web App Pentesting? (Part Two)
By Raxis Research Team Lead penetration tester Matt Dunn continues his discussion about web application testing. In Part Two, Matt explains testing as an authenticated user vs. as an unauthenticated user. March 4, 2022 -

What is Web Application Penetration Testing?
By Raxis Research Team Learn how Raxis approaches web application testing and how it differs from network penetration testing. Lead penetration tester Matt Dunn explains in this post. February 18, 2022 -

Reporting Tools for Large Penetration Tests
By Raxis Research Team Raxis lead penetration tester Matt Dunn has developed three new tools to make it easier to compile and present findings from large penetration tests. February 11, 2022