The Exploit articles categorized as Exploits
-
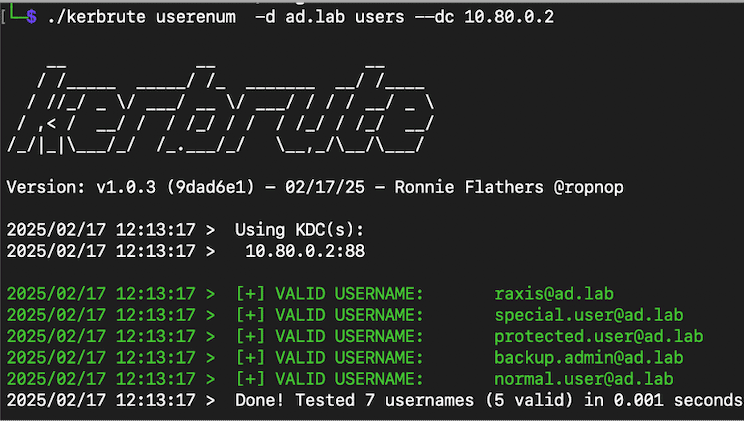
Cool Tools Series: Kerbrute
By Andrew Trexler Raxis Principal Penetration Tester Andrew Trexler walks through the many uses of Kerbrute from user enumeration to brute-forcing and password spraying. October 7, 2025 -

Lateral Movement: From Beachhead to Breach
By Nate Jernigan Raxis Senior Penetration Tester Nate Jernigan discusses lateral movement in penetration testing and the methods and tools he uses when performing these attacks. September 23, 2025 -

Dangers of Storing Sensitive Data in Web Storage: 5 Real Attack Scenarios
By Ryan Chaplin Lead Penetration Tester Ryan Chaplin walks us through 5 real-world attack scenarios used in real-world penetration tests by Raxis. August 26, 2025 -
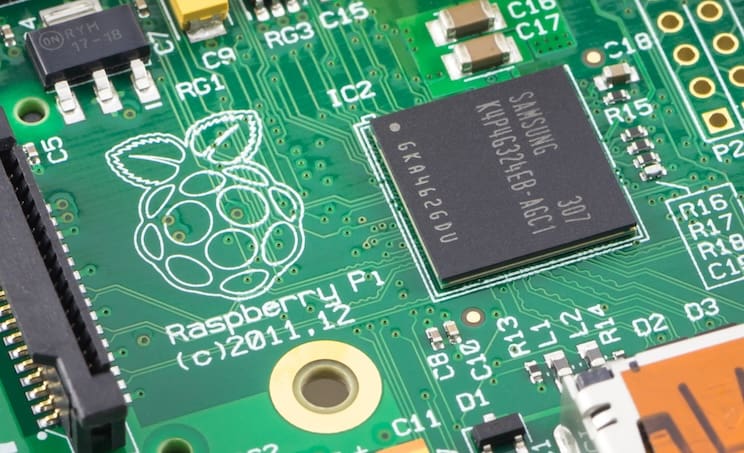
Raspberry Pi Planted in Failed ATM Heist
By Brian Tant Raxis CTO Brian Tant discusses the Raspberry Pi used in a recent ATM heist and how Raxis uses the same type of device in our pentesting. August 14, 2025 -

Microsoft Releases Security Patch for Actively Exploited On-Premises SharePoint Vulnerabilities
By Jason Taylor Microsoft has released patches for two critical vulnerabilities allowing unauthenticated remote code execution that affect on-premises SharePoint installations. July 22, 2025 -
OWASP Top 10 for LLM Applications Penetration Testing
By Jason Taylor Lead Penetration Tester Jason Taylor looks at OWASP’s Top 10 list for LLM applications for penetration testing as AI machine learning becomes prevalent. July 15, 2025