Exploits
Raxis Blog Posts by Category
-
 SQLi Series: An Introduction to SQL Injection for Penetration TestingRaxis’ Andrew Trexler explains what SQL Injection (SQLi) is and how to perform a simple exploit against a web app login page in penetration tests.
SQLi Series: An Introduction to SQL Injection for Penetration TestingRaxis’ Andrew Trexler explains what SQL Injection (SQLi) is and how to perform a simple exploit against a web app login page in penetration tests. -
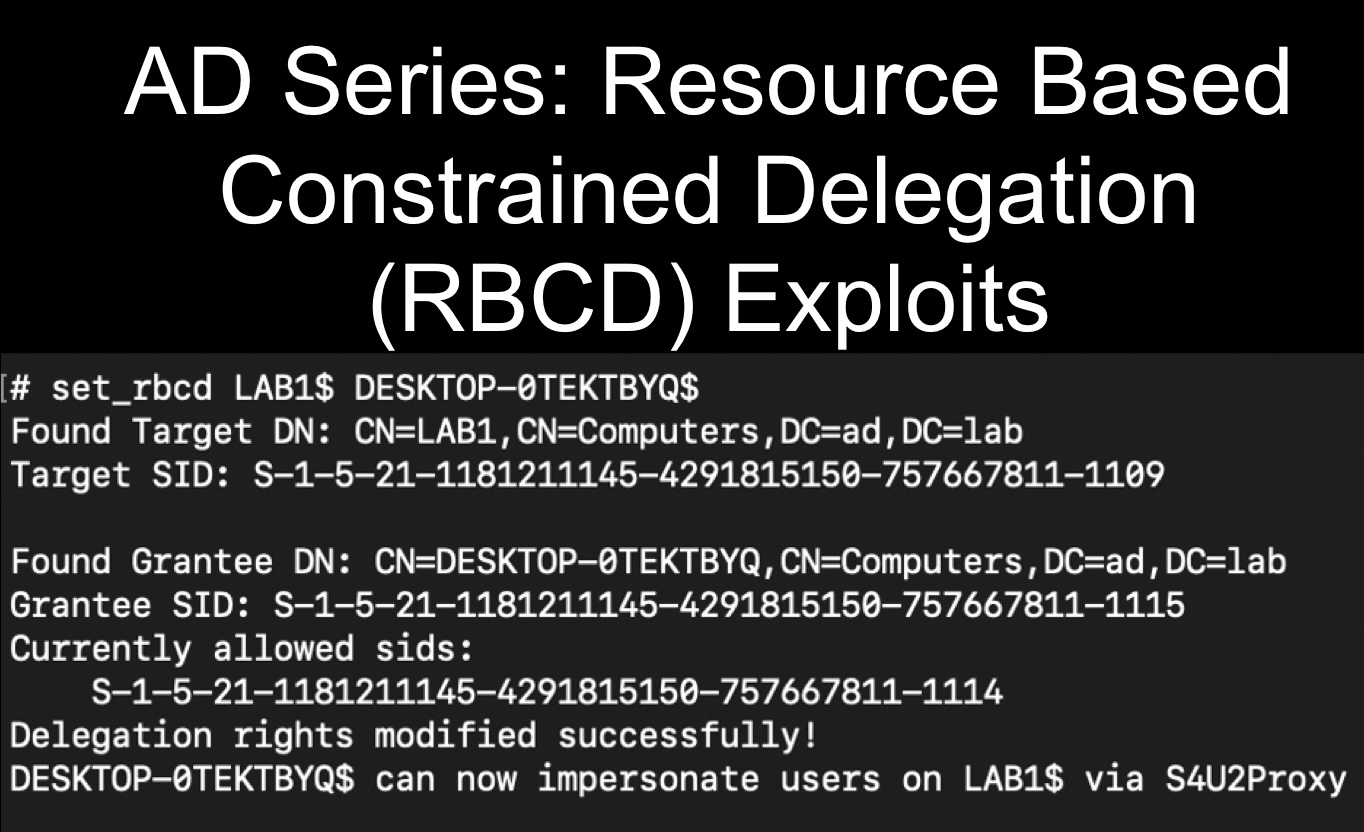 AD Series: Resource Based Constrained Delegation (RBCD) for Penetration TestingExploit msDS-AllowedToActOnBehalfOfOtherIdentitity to gain administrative access in a Resource Based Constrained Delegation (RBCD) attack on penetration tests.
AD Series: Resource Based Constrained Delegation (RBCD) for Penetration TestingExploit msDS-AllowedToActOnBehalfOfOtherIdentitity to gain administrative access in a Resource Based Constrained Delegation (RBCD) attack on penetration tests. -
 An Inside Look at a Raxis Red TeamThe Raxis Red Team Test is our top tier test that gives a true feel of what hackers could do. Curious to know more? Take a look at this short video.
An Inside Look at a Raxis Red TeamThe Raxis Red Team Test is our top tier test that gives a true feel of what hackers could do. Curious to know more? Take a look at this short video. -
 AD Series: Active Directory Certificate Services (ADCS) Exploits Using NTLMRelayx.py for Penetration TestsAndrew Trexler ran into issues with certipy when testing on port 443 and found that NTLMRelayx.py worked better in for those ADCS Exploits on penetration tests.
AD Series: Active Directory Certificate Services (ADCS) Exploits Using NTLMRelayx.py for Penetration TestsAndrew Trexler ran into issues with certipy when testing on port 443 and found that NTLMRelayx.py worked better in for those ADCS Exploits on penetration tests. -
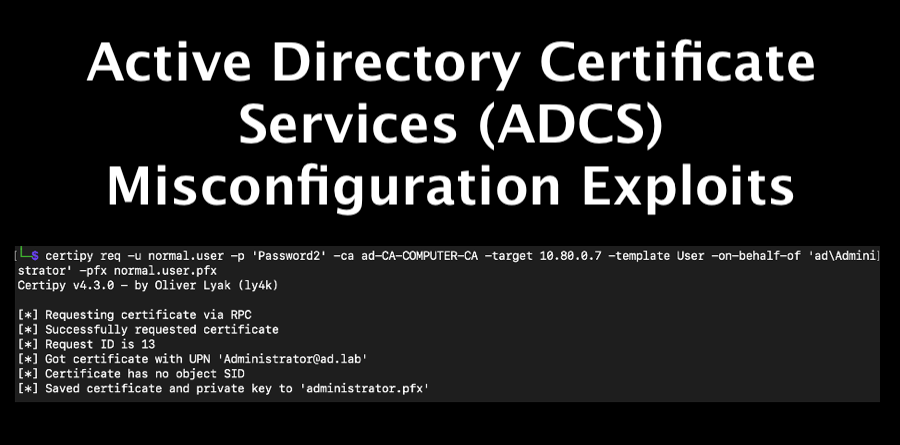 AD Series: Active Directory Certificate Services (ADCS) Misconfiguration Exploits for Penetration TestsAndrew Trexler adds to his Active Directory series with a tutorial of Active Directory Certificate Services (ADCS) misconfiguration exploits for penetration tests.
AD Series: Active Directory Certificate Services (ADCS) Misconfiguration Exploits for Penetration TestsAndrew Trexler adds to his Active Directory series with a tutorial of Active Directory Certificate Services (ADCS) misconfiguration exploits for penetration tests. -
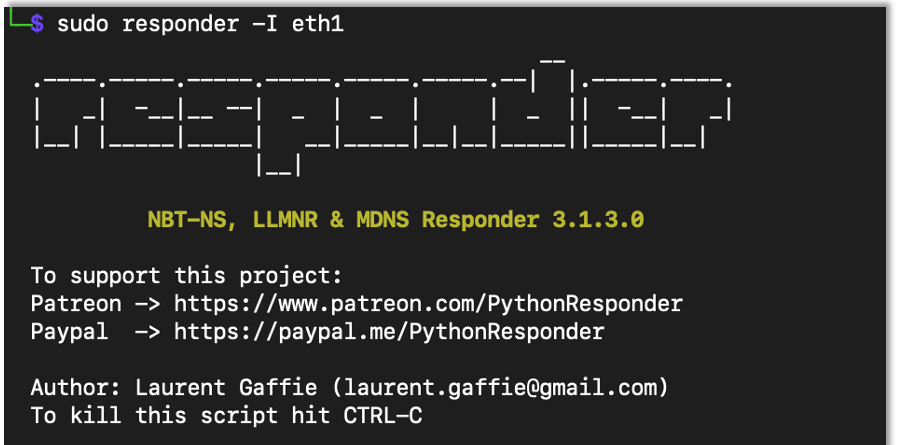 AD Series: How to Perform Broadcast Attacks Using NTLMRelayx, MiTM6 and Responder for Penetration TestsAndrew Trexler continues his AD Series with an in-depth tutorial on broadcast Attacks using NTLMRelayx, MiTM6 and Responder for penetration tests.
AD Series: How to Perform Broadcast Attacks Using NTLMRelayx, MiTM6 and Responder for Penetration TestsAndrew Trexler continues his AD Series with an in-depth tutorial on broadcast Attacks using NTLMRelayx, MiTM6 and Responder for penetration tests. -
 How to Create an AD Test Environment to Use for Penetration TestingAndrew Trexler walks us through creating a simple AD test environment to test new hacks before trying them on a penetration test.
How to Create an AD Test Environment to Use for Penetration TestingAndrew Trexler walks us through creating a simple AD test environment to test new hacks before trying them on a penetration test. -
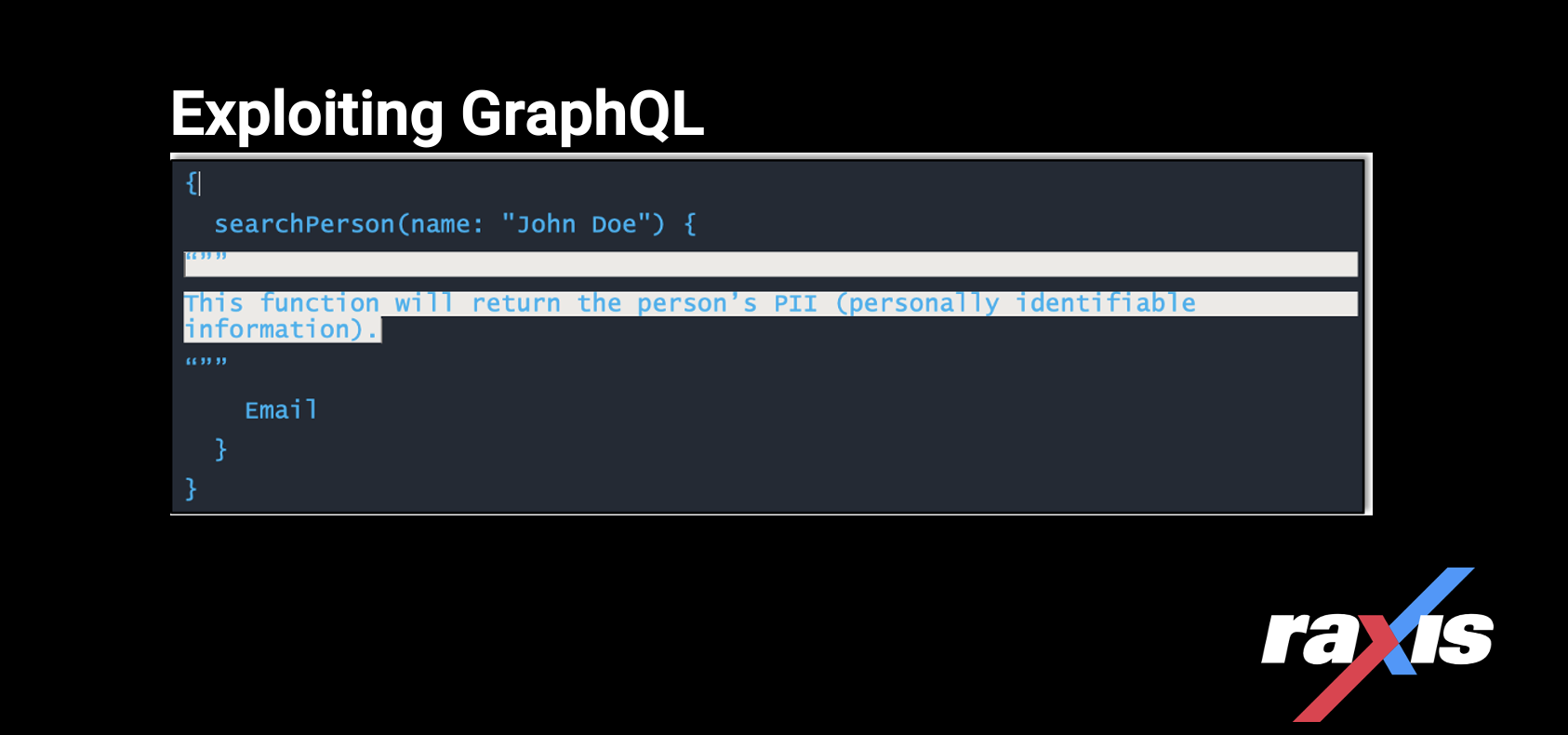 Exploiting GraphQL for Penetration TestingExploiting GraphQL, a query language inspired by the structure & functionality of online data storage & collaboration platforms Meta, Instagram & Google Sheets.
Exploiting GraphQL for Penetration TestingExploiting GraphQL, a query language inspired by the structure & functionality of online data storage & collaboration platforms Meta, Instagram & Google Sheets. -
 Log4j: How to Exploit and Test this Critical Vulnerability on Penetration TestsRaxis demonstrates how to obtain a remote shell on a target system during penetration tests using a Log4j open-source exploit available to all. (CVE-2021-44228)
Log4j: How to Exploit and Test this Critical Vulnerability on Penetration TestsRaxis demonstrates how to obtain a remote shell on a target system during penetration tests using a Log4j open-source exploit available to all. (CVE-2021-44228) -
 RAXIS THREAT ALERT: VULNERABILITY IN OPENSSL v3.0.xIn the cyberworld, news of a critical vulnerability affecting OpenSSL versions 3.0 – 3.0.6 will likely be the scariest part of Halloween ’22.
RAXIS THREAT ALERT: VULNERABILITY IN OPENSSL v3.0.xIn the cyberworld, news of a critical vulnerability affecting OpenSSL versions 3.0 – 3.0.6 will likely be the scariest part of Halloween ’22. -
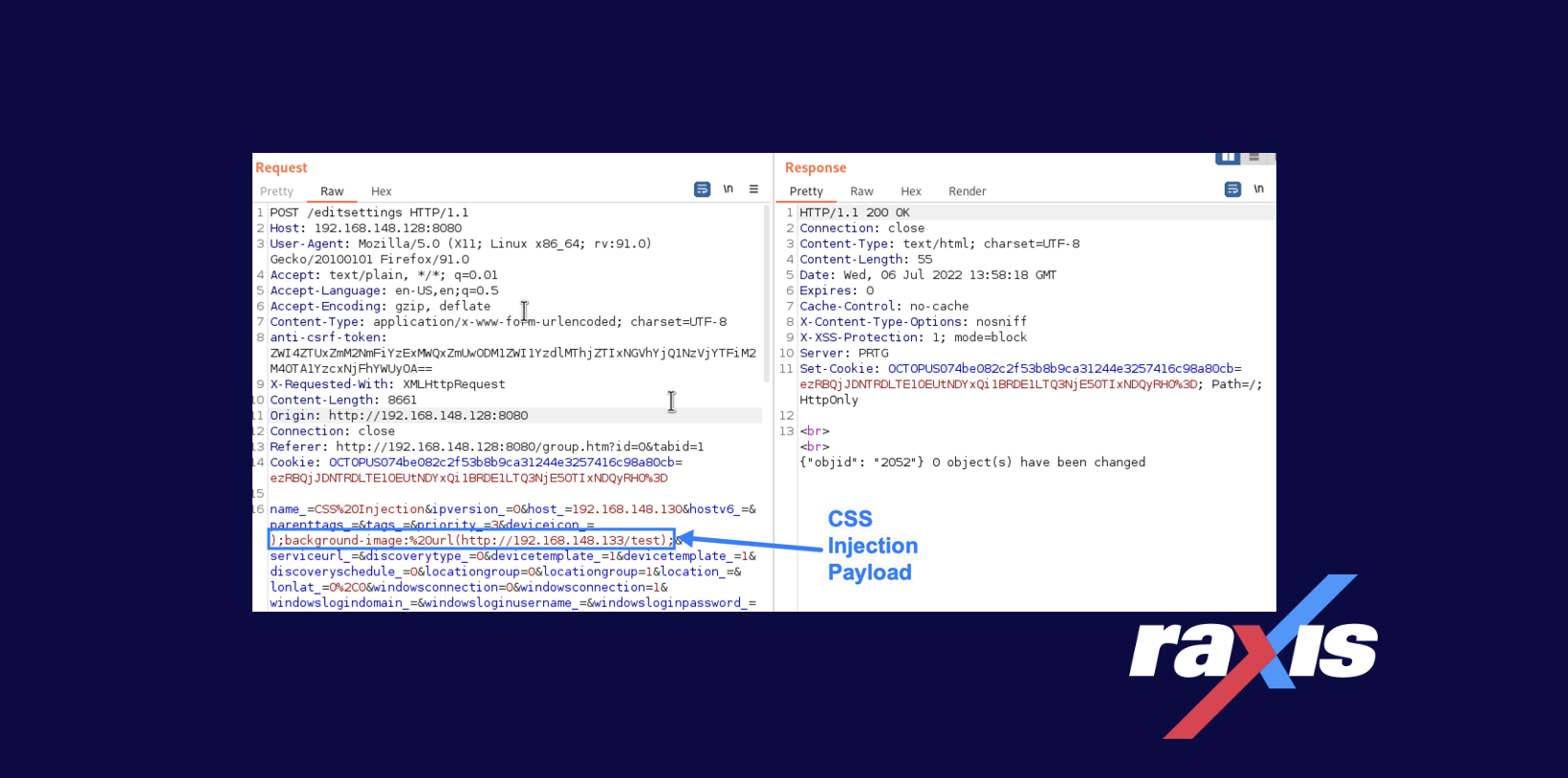 CVE-2022-35739: PRTG Network Monitor Cascading Style Sheets (CSS) InjectionThis CSS vulnerability, discovered by Raxis lead penetration tester Matt Mathur, lies in a device’s properties and how they are verified and displayed within PRTG Network Monitor.
CVE-2022-35739: PRTG Network Monitor Cascading Style Sheets (CSS) InjectionThis CSS vulnerability, discovered by Raxis lead penetration tester Matt Mathur, lies in a device’s properties and how they are verified and displayed within PRTG Network Monitor. -
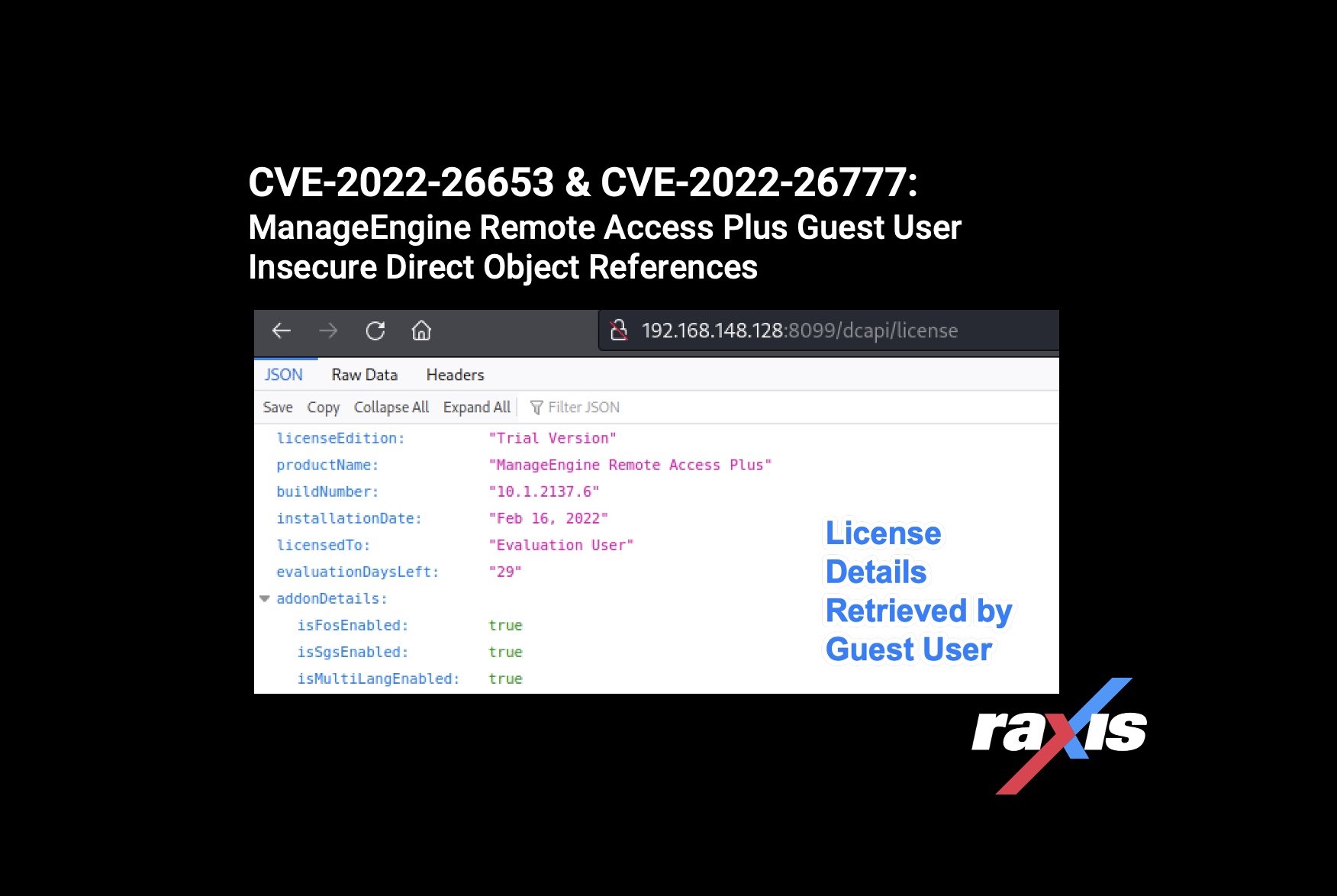 CVE-2022-26653 & CVE-2022-26777: ManageEngine Remote Access Plus Guest User Insecure Direct Object ReferencesRaxis lead penetration tester Matt Dunn uncovers two more ManageEngine vulnerabilities (CVE-2022-26653 & CVE-2022-26777).
CVE-2022-26653 & CVE-2022-26777: ManageEngine Remote Access Plus Guest User Insecure Direct Object ReferencesRaxis lead penetration tester Matt Dunn uncovers two more ManageEngine vulnerabilities (CVE-2022-26653 & CVE-2022-26777).
Categories
- Careers
- Exploits
- How To
- In The News
- Injection Attacks
- Just For Fun
- Meet The Team
- Mobile Apps
- Networks
- Password Cracking
- Penetration Testing
- Phishing
- PTaaS
- Raxis In The Community
- Red Team
- Security Recommendations
- Social Engineering
- Tips For Everyone
- Unsupported Software Unpatched Systems
- Web Apps
- What People Are Saying
- Wireless
