The Exploit articles categorized as Penetration Testing
-
The Role of AI in Penetration Testing
By Bonnie Smyre Bonnie Smyre shows how Raxis’ AI-augmented pentesting gives their expert pentesters more time for complex chained attacks and discovery of business-logic flaws. December 2, 2025 -
Wireless Encryption: WPA3 and the Gotchas Every Company Should Know About
By Brian Tant Brian Tant takes a look at WPA3. While offering much deeper security than WPA2, it is still vulnerable to transition Mode and side-channel attacks. November 18, 2025 -

Why We Don’t Change Risk Ratings on Pentest Findings (Even When You Ask Nicely)
By Tim Semchenko Raxis’ Tim Semchenko explains why we can’t lower risk ratings for your penetration test findings just because you ask and why that’s a good thing. November 4, 2025 -
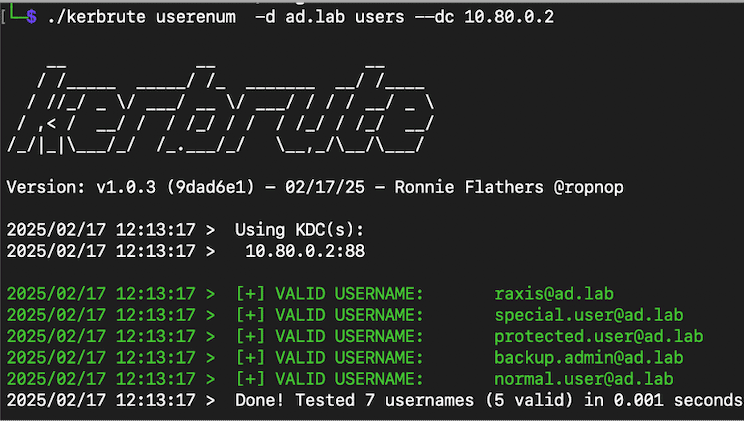
Cool Tools Series: Kerbrute
By Andrew Trexler Raxis Principal Penetration Tester Andrew Trexler walks through the many uses of Kerbrute from user enumeration to brute-forcing and password spraying. October 7, 2025 -

Lateral Movement: From Beachhead to Breach
By Nate Jernigan Raxis Senior Penetration Tester Nate Jernigan discusses lateral movement in penetration testing and the methods and tools he uses when performing these attacks. September 23, 2025 -

Lessons from the DaVita Healthcare Ransomware Attack
By Brian Tant The DaVita ransomware attack is one of the most impactful recent healthcare breaches. Learn what happened and what could have been done to limit the impact. September 18, 2025