The Exploit articles categorized as Security Recommendations
-

Sponsored Malware: When the Bad Guys Pay for Views
By Jason Taylor When a Raxis pentester Jason Taylor found a suspicious sponsored search result, he broke down the code it would have run and discovered it was malware. March 13, 2026 -

The Hidden Risks in Your Password: What You Type Matters More Than You Think
By Brad Herring Raxis has discovered and cracked our fair share of password hashes. Some that we have discovered may surprise you… and their bosses. Learn what not to do. March 10, 2026 -

Reynolds Ransomware BYOVD Eludes EDR Tools
By Nathan Anderson Reynolds poses a new type of threat by including a Bring Your Own Vulnerable Driver (BYOVD) in the ransomware bundle, making it harder for EDR tools to catch. February 20, 2026 -

BeyondTrust RCE Vulnerability Exploited: Critical 9.9 CVSS Flaw Under Active Attack
By Ryan Chaplin While BeyondTrust patched cloud-hosted Remote Support customers earlier this month, on-premises deployments of BeyondTrust must manually patch to remediate. February 17, 2026 -
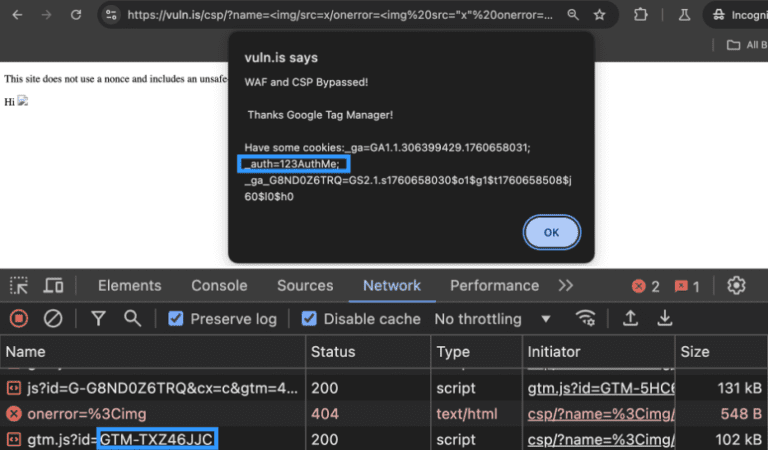
Bypassing a WAF and a CSP with Google Tag Manager: An Attacker’s Perspective and Remediation Advice
By Ryan Chaplin Ryan Chaplin takes an in-depth look at how attackers can use unsafe directives to bypass CSP, notably in Google Tag Manager, and how to remediate the issue. February 10, 2026 -

CVE-2025-59886 Eaton Exploit Code Published
By Jason Taylor With exploit code available for the vulnerabilities in Eaton’s xComfort Ethernet Communication Interface, Jason Taylor recommends replacing or isolating. February 5, 2026