The Exploit articles categorized as Exploits
-
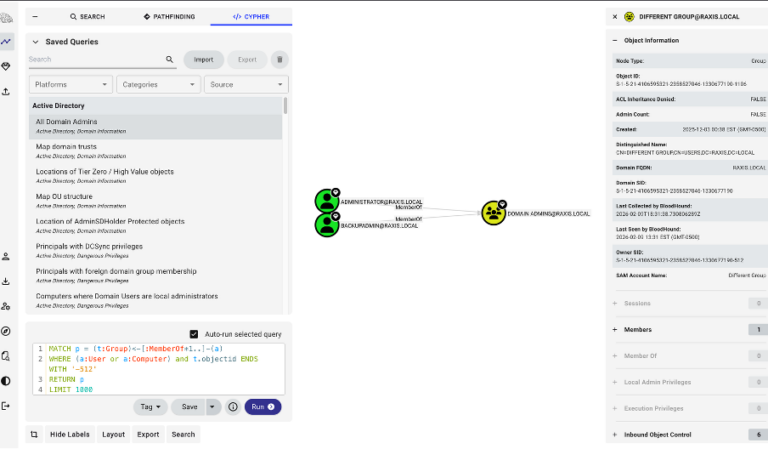
Cool Tools: Bloodhound CE
By Andrew Trexler BloodHound’s Community Edition has everything a penetration tester needs to enumerate relationships in a domain in order to gain more access, even Domain Admin. June 2, 2026 -
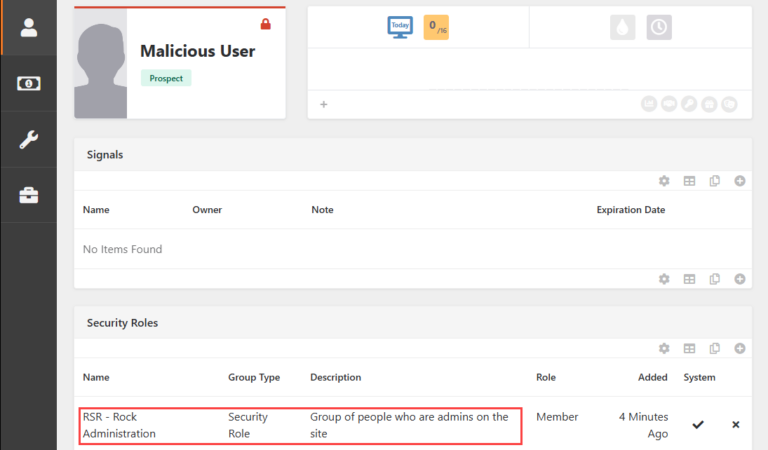
CVE-2026-36748: XSS in Rock RMS Leads to Privilege Escalation
By Jason Taylor Raxis Lead Pentester Jason Taylor recently discovered CVE-2026-36748, a high-risk XSS vulnerability in Rock RMS that allows privilege escalation to admin. June 1, 2026 -

Defense in Depth Against Linux Kernel Privilege Escalation: A Practical Guide for Container Workloads
By Ryan Chaplin With current local privilege escalation exploits like Copy Fail and Dirty Frag active in the wild, harden your defenses to halt attacks even before patching. May 26, 2026 -
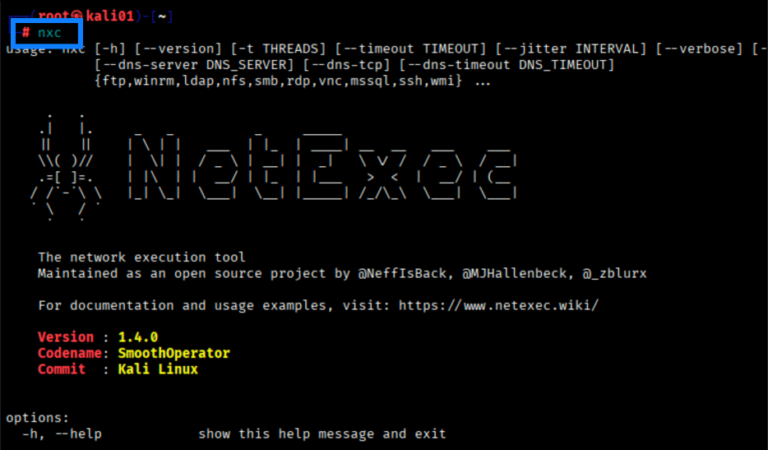
Cool Tools: NetExec (NXC) Fundamentals
By Scottie Cole Now that CrackMapExec is no more, how is a pentester to rapidly test credentials, enumerate assets, spray passwords, and more? Learn the basics of NetExec here. May 19, 2026 -
Copy Fail – Local Linux Privilege Escalation in 4 lines
By Jason Taylor CVE-2026-31431, dubbed Copy Fail, allows privilege escalation to root on Linux distros missing the latest kernel patches. Learn what to do in this blog. May 8, 2026 -

No Malware Required
By Brian Tant The March 2026 attack on Stryker Corporation was not Malware and did not make Ransomware demands. Instead it used compromised credentials to disrupt business. May 1, 2026